What are the most common threats to IT/OT environments?
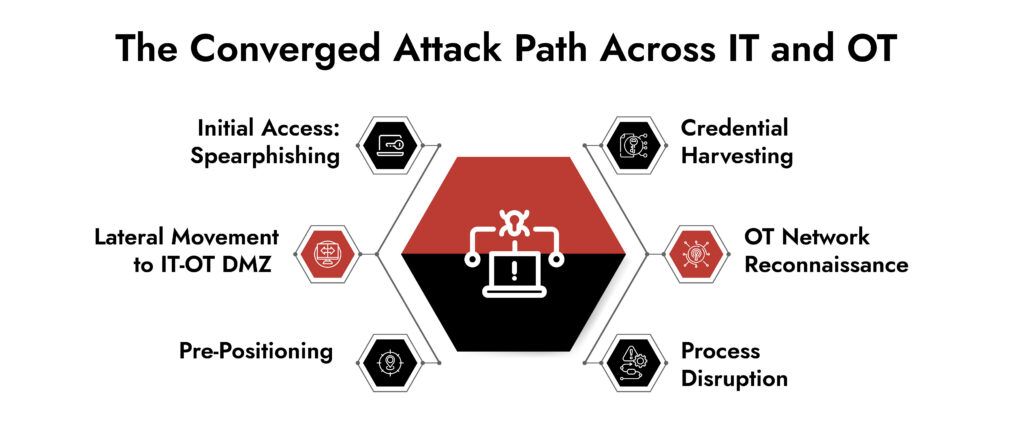
The most prevalent IT/OT security threats include
- Ransomware deployed via IT infrastructure
- Identity-based attacks leveraging compromised credentials to traverse IT-OT boundaries,
- Supply chain compromises through vendor remote access,
- Industrial protocol manipulation targeting PLCs and field devices,
- Covert long-term reconnaissance in insufficiently segmented OT environments
Picture this: a mid-sized energy utility IT helpdesk gets a routine phishing alert at 7:42 AM. The ticket is triaged, the endpoint is quarantined, and the analyst moves on. By 11:15 AM, an engineering workstation in the substation control room loses communication with field devices. SCADA alarms pile up. By the time the OT network team traces the disruption back to a compromised jump server that bridged both networks, four hours of generation data are missing.
The scary part is that this scenario isn’t hypothetical; it mirrors the operational anatomy of dozens of incidents that have impacted utilities, manufacturers, and critical infrastructure operators over the past three years. The adversary didn’t “attack OT.” They attacked IT, and the blast radius did the rest.
54% of OT organizations experienced a cyberattack impacting OT systems in 2024.
The growing entanglement of IT and OT isn’t a future risk. It’s an active attack surface that adversaries are already mapping, probing, and exploiting. Security leaders who still treat IT and OT as parallel but separate domains are operating with a dangerous blind spot.
Why IT-OT Threat Exposure is Growing
For most of industrial history, OT networks were physically isolated. Air gaps, proprietary protocols, and closed architectures made them difficult targets by default. That era is essentially over.
Digital transformation initiatives, remote access requirements accelerated by the pandemic, cloud-connected historian systems, vendor remote maintenance agreements, and enterprise ERP integrations have collectively dismantled the isolation model. The average industrial facility today has dozens of external connections into its OT environment, many of which are unmonitored, undocumented, or both.
Legacy systems compound the problem. They were never designed to operate alongside cloud endpoints. PLCs running decade-old firmware can’t be patched on a standard IT cycle without risking process disruption. Yet these assets now sit on the same routable network segments as systems that touch the internet. The IT/OT security threats this creates are structural, not incidental.
Meanwhile, the threat actor landscape has shifted. Nation-state groups like Volt Typhoon, Sandworm, and CHERNOVITE, with documented interest in critical infrastructure, are no longer just conducting espionage. Ransomware groups have evolved into operationally sophisticated criminal enterprises that specifically hunt for IT-to-OT pivot paths, knowing that threatening uptime commands larger ransom payments.
What consistently surprises incident responders in OT environments isn’t the sophistication of the attack it’s how long the adversary had been present before anyone noticed. In several major industrial incidents, post-breach forensic analysis revealed reconnaissance activity that predated the disruptive action by six, nine, sometimes fourteen months. The organization had security tools. They had monitoring. But they had no visibility into OT-specific behaviors, and they had no packet history to reconstruct what the adversary had learned about their processes. By the time the disruption occurred, the attacker understood the facility better than most of the operations staff.
— Nolan Ross, Sales Engineer, NetWitness
Key IT-Originated Threats Escalating into OT Impact
Identity Compromise and Lateral Movement
Stolen credentials remain the single most reliable entry point into converged environments. Domain admin credentials harvested from a corporate workstation often provide unchallenged access to engineering workstations, historian servers, and OT-adjacent jump hosts. Active Directory misconfiguration, flat network segments, and over-privileged service accounts create lateral movement paths that adversaries can traverse with minimal tooling.
Most OT network environments lack the telemetry to distinguish legitimate engineering access from adversarial lateral movement. Authentication logs are sparse, behavioral baselines don’t exist, and SIEM rules built for IT environments don’t understand industrial protocol context.
Ransomware and Malware
The Colonial Pipeline incident established a template: encrypt the IT side, threaten the OT side, collect ransom from operators who can’t afford operational downtime. Even when ransomware doesn’t cross into the OT network directly, operators routinely shut down OT systems as a precaution.
But the recent ransomware in OT environments has demonstrated the ability to deploy ransomware payloads specifically designed to interact with industrial control interfaces. The operational impact is the main objective.
Supply Chain and Vendor Access Risks
Third-party remote access is the unguarded door in most OT environments. Vendor technicians, system integrators, and OEM support teams routinely connect to OT systems with minimal authentication controls, no session recording, and persistent credentials that are rarely rotated. The compromise of a single integrator can simultaneously expose dozens of industrial customers to a risk profile that doesn’t exist anywhere else in the enterprise security landscape.
Industrial Protocol Manipulation
Protocols like Modbus, DNP3, EtherNet/IP, and IEC 61850 were not designed for cybersecurity. They don’t carry authentication, encryption, or integrity checking. An adversary who has gained access to an OT network can issue legitimate-looking commands to field devices to adjust setpoints, modify control logic, or disable safety instrumentation.
These cyber threats in operational technology are functionally invisible to IT security tooling. A SIEM doesn’t understand Modbus function codes. An EDR agent doesn’t run on a remote terminal unit. The only way to detect the manipulation is purpose-built OT network monitoring that parses industrial traffic at the packet level.
Denial of Service Attacks
Availability remains the most critical security objective in industrial environments, which makes denial of service attacks particularly effective. Unlike enterprise outages that may be tolerated for short durations, OT network disruptions can halt production lines.
Threat actors increasingly use targeted network flooding, malformed industrial packets, or resource exhaustion techniques against control system infrastructure. Even limited disruptions to historian connectivity or supervisory control communications can force operators into manual fallback modes. In safety-sensitive sectors, precautionary shutdown procedures are often initiated long before the root cause is fully understood, amplifying the operational impact of relatively simple attack techniques.
Insider Threats
Engineers, contractors, and plant operators routinely hold access that, in any other security context, would require multi-party approval and a paper trail. It is operationally normal to push logic changes to controllers, modify safety interlock configurations, and bypass change management entirely when production pressure is high enough. That’s what makes this hard to defend against.
The uncomfortable reality is that most OT environments simply don’t have the monitoring to reconstruct what happened after the fact. No record of which configuration files were transferred. No command-level audit trail. No behavioral baseline to flag that someone spent forty-five minutes in a controller that isn’t part of their normal work.
Capabilities Security Leaders Should Prioritize
OT threats are moving faster than most security programs are built to handle. So what actually works?
- Unified visibility across IT and OT: You can’t protect what you can’t see. Passive asset discovery and traffic baselining across both environments gives SOC teams and OT engineers a shared operational picture, because right now those two groups are often working from completely different information.
- Protocol-aware inspection: Generic NDR tools don’t speak Modbus or DNP3. They’ll miss an unauthorized function code or a malformed command sequence entirely because they don’t know what they’re looking at. Security tooling in OT environments needs to understand the traffic natively, not approximate it.
- Behavioral detection for OT threats: What’s anomalous in a refinery control system looks nothing like what’s anomalous in a corporate IT environment. Detection logic needs to know what normal looks like for that specific process, otherwise you’re generating noise at best and missing real threats at worst.
- Full-packet capture: Logs in OT environments are incomplete by default. Continuous network recording fills that gap and completely changes what incident response looks like. Forensic reconstruction becomes possible instead of speculative.
- Risk-based alert prioritization: A PLC receiving an unauthorized configuration push is not the same priority as a laptop hitting an unusual domain. Alert tuning needs to reflect that, or SOC teams end up burying the signals that matter most.
- Integrated SOC-OT workflows: Workflows that actually connect SOC to the plant floor. Detection without a clear escalation path is just an unread notification. Runbooks need to bridge IT security and OT operations so that when something is caught, the right people act on it fast enough to matter.
NetWitness with the above features, allows organizations running purpose-built OT security alongside their IT stack to consistently see faster detection and cleaner forensic outcomes.
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
Conclusion
The business case for OT network security has never been clearer. The average cost of an unplanned industrial downtime event exceeds $125,000 per hour in manufacturing and for energy, utilities, and process industries, that figure climbs dramatically. Regulatory pressure is also intensifying: NERC CIP, IEC 62443, the NIS2 Directive, and TSA pipeline security directives all increasingly mandate active OT monitoring, documented incident response capabilities, and formal security assessments.
Security leaders who are still approaching OT risk through an IT security lens are mismatched to the threat. The convergence of IT and OT isn’t a reason to extend existing IT tools further — it’s a reason to build security capabilities that were designed from the ground up to understand industrial environments, industrial protocols, and operational consequences.
The organizations that will navigate the next wave of IT OT cybersecurity risks most effectively aren’t the ones with the most technology. They’re the ones that built genuine visibility into their OT network, trained their SOC to think in operational context, and established detection and response workflows that reflect the operational realities of the shop floor.
Frequently Asked Questions
1. How does IT/OT convergence increase cybersecurity risks?
IT/OT convergence increases risk through several compounding mechanisms. Legacy OT assets designed without security controls are now connected to enterprise networks. Remote access requirements create persistent external connection paths into OT environments. Shared credentials, overlapping network segments, and IT systems that bridge both domains create lateral movement pathways that adversaries can exploit. Security architecture designed for IT environments doesn’t translate cleanly to OT environments where availability is the primary requirement.
2. What role does ransomware play in IT/OT security threats?
Ransomware has become the dominant monetization mechanism for OT-impacting attacks. Even when ransomware doesn’t cross into the OT network directly, operators frequently shut down OT systems as a precaution, achieving the adversary’s operational disruption objective without requiring OT-specific capabilities. More sophisticated groups specifically search for IT/OT pivot paths, knowing that threatened operational downtime generates faster payment decisions. A subset of ransomware groups has now developed payloads designed to interact with industrial control interfaces directly.
3. How to monitor IT/OT network traffic effectively?
Effective OT network monitoring requires passive traffic collection at key network boundaries, including IT/OT DMZ segments, OT zone interconnects, and remote access ingress points. Deep packet inspection capable of parsing industrial protocols is essential. Behavioral baselining over a representative period of normal operations should precede alerting configuration to avoid false-positive flooding. Cross-domain correlation dramatically improves the ability to detect converged attack paths before they reach the disruptive stage.





