What are the common causes of healthcare data breaches?
Healthcare data breaches are caused by ransomware and cyberattacks that encrypt hospital systems and demand payment, phishing attacks that trick staff into surrendering credentials, insider threats from both accidental mishandling and malicious data theft, third-party vendor vulnerabilities that expose patient data through supply chain access, system weaknesses like unpatched software and misconfigured databases, and physical security failures involving lost devices or improperly disposed records. Healthcare cybersecurity risks are amplified by the high value of medical records, the sector’s low tolerance for downtime, and the complexity of interconnected healthcare IT environments.
Introduction
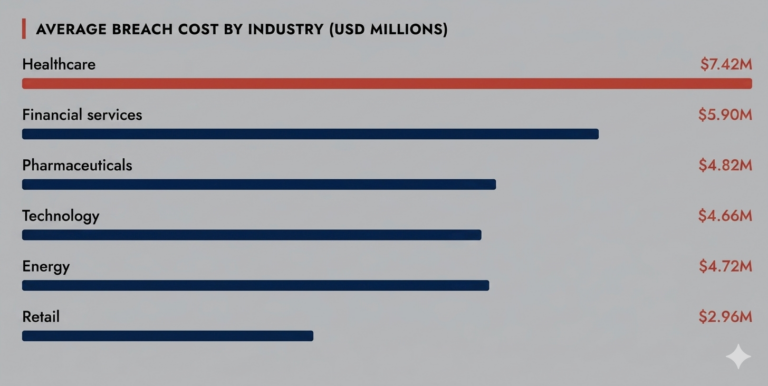
Healthcare is the most expensive industry to breach. Not by a little. A single incident costs an average of $7.42 million in 2025, and organizations take 279 days just to detect and contain it. Five weeks longer than any other industry. The attacks are not getting more sophisticated in ways that should be surprising. What is surprising is how consistently the same vulnerabilities get exploited, year after year, across organizations that absolutely know better.
So what is actually going wrong with healthcare data breaches?
Why Healthcare Is a Prime Target
A stolen credit card sells for a few dollars on the dark web. A complete medical record can fetch hundreds. Insurance policy numbers, Social Security data, billing history, prescription records it is all in one file. Healthcare data security threats are so persistent partly because the product being stolen is genuinely valuable in ways most industries cannot match.
The other piece is operational pressure. When a retail business gets hit with ransomware, they can absorb a day of downtime. Hospitals cannot make that calculation. Care does not pause while IT rebuilds systems. Ransomware in the healthcare industry is effective precisely because attackers understand that the cost of not paying often feels higher than the cost of paying. That psychology drives a lot of decisions that organizations later regret.
The Six Core Causes of Healthcare Data Breaches
1. Ransomware and Cyberattacks
Ransomware in the healthcare industry has a simple operational logic behind it. Encrypt the EHR, the pharmacy system, the scheduling platform. Wait. The hospital needs those systems to function, so the pressure to restore access fast is enormous. What most people miss is that by the time ransomware deploys, attackers have often been inside the network for weeks. They have already pulled data. The encryption is almost the final step, not the primary one.
The Change Healthcare ransomware attack in 2024 made this concrete at a scale nobody had fully anticipated. Because Change Healthcare handled roughly one-third of all US patient transactions, a single breach did not just damage one organization. It cut off claims processing and pharmacy verification for thousands of providers across the country. Smaller practices that depended on that infrastructure for cash flow faced weeks of disruption. One vulnerable node, one attack, and the damage rippled through an entire national system. Network health monitoring and early detection are not optional extras in this environment. They are the difference between catching an intrusion early and discovering it after the encryption notice appears on every screen.
2. Phishing Attacks in Healthcare
Phishing attacks in healthcare succeed because they are engineered around the realities of clinical work. A spear phishing email arrives looking like an internal IT ticket or a message from a known vendor contact. It has the right name, the right tone, sometimes even the right hospital branding. A nurse checking messages between patients is not running a fraud investigation on every link. Nobody is. Attackers build their campaigns knowing that.
Once credentials are captured, the attacker has legitimate access. No alarms trip. No anomalies appear. They move through clinical and administrative systems the same way a real user would. Phishing is also how most ransomware and malware payloads get delivered in the first place, which makes it the root cause behind a disproportionate share of serious healthcare cyber attacks. Fixing this requires treating it as an infrastructure problem. Layered technical controls, one-click internal reporting that does not punish staff for clicking, and short role-specific training that gets updated when attack patterns change. Not a once-a-year compliance session that everyone forgets by the following week.
3. Insider Threats in Healthcare
Insider threats in healthcare rarely look the way people expect. The accidental category is actually the larger one. A staff member emails a patient file to the wrong recipient. A laptop goes missing on the commute home. Printed records get left in a break room. These incidents do not make headlines but they trigger HIPAA notification obligations and they happen constantly across organizations of every size.
Malicious insider threats are less frequent but harder to deal with. A staff member accessing patient records outside their clinical scope, pulling data to sell, can operate for months without detection if monitoring is built around static rules. The access looks normal because it technically is normal credentials being used. Catching it requires behavioral analytics that understand what a given role actually needs to access and flags deviations from that baseline. Healthcare data security threats from inside the organization are not a secondary concern. They are one of the most consistent sources of breach incidents in the sector and one of the least resourced areas of healthcare cybersecurity.
4. Third-Party and Supply Chain Risks
Here is something worth sitting with. Your organization can have solid internal security practices and still get breached because a billing vendor left a database misconfigured. Third-party and supply chain risks are responsible for a significant share of healthcare data breaches, and most organizations do not have visibility into what their vendors are actually doing with the access they have been granted.
Billing companies, cloud storage providers, transcription services, IT contractors all of them touch patient data. Many operate with security postures that would not pass an internal audit. The Change Healthcare ransomware attack is again the clearest illustration of how supply chain exposure works at scale. Healthcare cybersecurity solutions that only look inward miss half the problem. Vendor risk management needs real teeth actual security control reviews, access scoped tightly to what the role requires, and contractual breach notification requirements that create accountability rather than just paperwork.
5. System and Process Weaknesses
Legacy systems and unpatched software are endemic in healthcare, and the reasons are more structural than negligent. Clinical devices often cannot be updated without vendor recertification, a process that can take years. So a networked imaging machine runs a decade-old operating system with known vulnerabilities, sitting on the same network as the EHR, and nobody has a fast path to fix it. Attackers do not need to invent exploits for this. Automated scanners find these gaps routinely.
Misconfigured cloud storage and databases left publicly accessible have exposed millions of patient records in incidents that required no hacking at all in the traditional sense. Over-provisioned access rights mean that when one account is compromised, the attacker inherits far more access than the role ever needed. Consistent network health monitoring, least-privilege access controls, and a disciplined patching cadence address most of this. The challenge is that healthcare cybersecurity risks in this category tend to get treated as background problems until they become front-page ones.
6. Physical Security Failures
Physical breaches do not generate the same attention as ransomware but they produce the same regulatory consequences. A lost laptop with unencrypted patient data is a reportable breach. So is a USB drive left in a car, or paper records thrown in a general waste bin rather than shredded. Healthcare data security threats are not confined to the network and never have been.
What keeps this category persistent is that it is embedded in how clinical work actually happens. Staff move between sites, carry devices, print documentation. The fixes are not complicated but they require consistent enforcement: full-disk encryption on every device, remote wipe capability, formal record disposal protocols, and controlled physical access to server rooms and restricted areas. Physical security in healthcare tends to get treated as a facilities problem rather than a cybersecurity one. That framing is part of why it keeps producing breaches.
Break down silos and accelerate investigations by connecting SIEM, NDR, and EDR into a single, intelligent workflow.
- Unified visibility across logs, endpoints, and network traffic
- Correlated insights to uncover multi-stage attacks faster
- Reduced alert fatigue with prioritized, high-fidelity alerts
- Seamless analyst workflows from detection to response
Emerging Threats: IoT Devices and AI-Driven Attacks
Modern hospitals are full of networked clinical devices that were never designed with security in mind. Infusion pumps, patient monitors, imaging equipment many run outdated operating systems, receive patches infrequently if at all, and connect directly to clinical networks. Standard network health monitoring tools often cannot see them. From an attacker’s perspective, they are an entry point that carries almost no detection risk.
AI-driven attacks are compounding the problem. Automated tools can now probe healthcare networks at scale, identify unpatched vulnerabilities faster than security teams can respond, and generate phishing content convincing enough to fool staff who have had training. Healthcare cybersecurity risks in this space are evolving in ways that outpace the response capacity of most organizations, particularly smaller health systems operating without dedicated security teams.
What Healthcare Cybersecurity Solutions Actually Need to Address
The reason generic security frameworks struggle in healthcare is that the environment does not behave like other industries. Care cannot stop for an incident response. The workforce is large, distributed, and under constant time pressure. Vendor relationships are numerous and deeply embedded. Regulatory requirements add a layer of complexity that shapes every security decision made.
Effective cybersecurity for healthcare has to account for all of this simultaneously. Continuous network health monitoring across both clinical and administrative infrastructure. Vendor risk programs with genuine review processes rather than checkbox questionnaires. Least-privilege access with regular audits that actually remove unnecessary permissions. Encryption covering data at rest and in transit, including on mobile and remote devices. Incident response plans built around care continuity, not just IT recovery timelines. And an IoT device inventory that treats networked medical equipment as the security exposure it represents, not just clinical hardware managed by biomedical engineering.
The Honest Assessment for Healthcare Data Breaches
The danger from healthcare data security threats in part stems from the fact that the targets most often attacked are most often under-resourced. Small community hospitals, rural health systems, and specialist groups handle the same types of data and attract the same sorts of attacks as large academic medical institutions, but have less to protect them.
The 279-day detection time is symptomatic not just of a technological deficit. It reflects an industry that has historically seen security as an administrative, rather than an operational, cost. Things are getting better, but so are cyber attacks in healthcare. The fastest to close this gap are those who stop thinking about cybersecurity for healthcare as just an IT matter and begin thinking about it the way they think about patient safety as a clinical and operational matter that is resourced and governed accordingly.
Bottom Line
Healthcare data breaches occur for understandable reasons: hackers know the value of medical data; healthcare systems aren’t built with security in mind; and business pressures encourage speed over suspicion and trust in vendor partner networks. The shift is simple but non-negotiable: treat cybersecurity with the same urgency as patient care, because in practice, they are inseparable.
Frequently Asked Questions
1. How do phishing attacks lead to healthcare data breaches?
Phishing attacks in healthcare trick staff into sharing credentials or downloading malware, giving attackers access to systems and leading to healthcare data breaches.
2. Why is the healthcare industry a major target for cyberattacks?
Healthcare cybersecurity risks are high because medical records are valuable, systems are often outdated, and operations can’t afford downtime, making them easy targets for healthcare cyber attacks.
3. What role do insider threats play in healthcare breaches?
Insider threats in healthcare arise when employees or partners misuse access or make mistakes, exposing sensitive data and increasing healthcare data security threats.
4. How does ransomware impact healthcare organizations?
Ransomware in the healthcare industry locks critical systems, disrupts care, and causes financial and operational damage, making it one of the most severe healthcare cyber attacks.
5. How can healthcare organizations prevent data breaches?
Strong healthcare cybersecurity solutions, network health monitoring, access controls, and staff training help reduce healthcare cybersecurity risks and prevent data breaches.
Threat Intelligence: The Key to Higher Security Operation Performance
Unlock the full potential of your Security Operations Center with deeper visibility, faster detection, and smarter response. This whitepaper explores how modern threat intelligence elevates SOC maturity and helps organizations stay ahead of evolving adversaries.