A Practical Overview of Cloud Threat and Detection Response
There are three components in detecting and responding to threats in the cloud: visibility, context and speed. Visibility is full visibility into all aspects of the organization’s identity (users or devices), networks and workloads. Context is the connection of signals to create a unified narrative about an attack. Speed is the ability to take action rapidly. Gaps in threat detection typically occur because there are multiple tools that exist independently and generate alerts without context. The unified platform solution will aggregate all forms of telemetry data, use behavioral analytics as part of the analytical process and enable very fast, informed responses through a single workflow.
Introduction
Cloud security didn’t get easier with scale, it got harder to verify. You can deploy controls across every layer of your cloud stack and still miss what matters. Why? Because attackers don’t operate in isolated signals. They operate in sequences – login, pivot, escalate, exfiltrate. If your cloud threat detection and response strategy can’t connect those steps, it won’t catch the attack.
This is where most cloud cybersecurity solutions fall short. They collect data but fail to reconstruct behavior. And in cloud environments, behavior is everything.
Why Cloud Threat Detection and Response Needs a Different Approach
Cloud infrastructure changes constantly. Detection strategies can’t stay static. In traditional environments, you controlled the network. In cloud, you inherit partial control and fragmented visibility. Logs sit across providers. Traffic stays internal. Identity becomes the primary attack vector.
According to Cybersecurity and Infrastructure Security Agency, identity misuse remains the leading cause of cloud breaches in 2024.
Here’s the shift:
- Detection must track behavior, not just events
- Visibility must extend beyond logs into network-level activity
- Response must happen within the same workflow as detection
That’s the baseline for effective cloud threat detection and response.
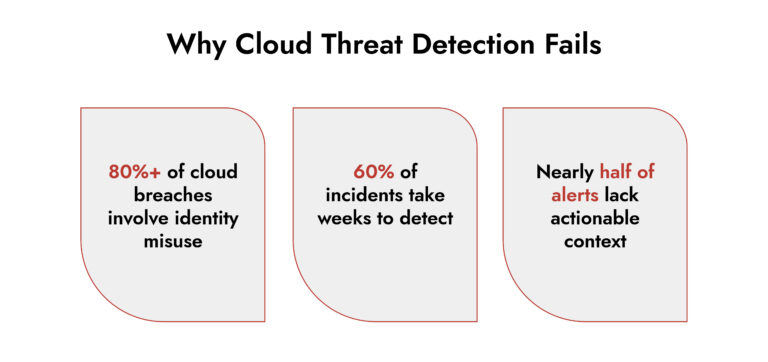
Where Most Cloud Threat Detection Strategies Break Down
Visibility Stops at the Surface
Most cloud threat detection tools rely heavily on logs. Logs tell you what was recorded, not what actually happened across the network.
Without packet-level or session-based visibility, lateral movement inside your cloud security network remains invisible.
Signals Stay Disconnected
Security teams often juggle:
- Cloud logs
- Endpoint alerts
- Identity events
- Network metadata
But without correlation, these signals don’t form a narrative. That slows down cloud incident response when speed matters most.
Alerts Lack Context
Alert volume isn’t the problem, clarity is. According to Gartner, SOC teams still struggle to prioritize alerts due to missing context and incomplete attack visibility. That’s why many cloud threat response solutions fail during real incidents, they detect symptoms, not the root cause.
360° Cybersecurity with NetWitness Platform
– Unrivaled visibility into your organization’s data
– Advanced behavioral analytics and threat intelligence
– Threat detections and response actionable with the most complete toolset
What Effective Cloud Threat Detection and Response Actually Looks Like
Strong cloud threat detection and response isn’t about stacking tools. It’s about connecting signals.
Unified Visibility Across the Cloud Security Network
You need visibility that spans:
- Cloud workloads
- East-west network traffic
- Identity and access behavior
- Endpoint interactions
This isn’t optional. Without it, detection remains partial.
Behavior-Driven Detection
Attackers don’t follow signatures. They adapt. Modern cloud cybersecurity strategies rely on:
- Behavioral baselines
- Anomaly detection
- Integrated threat intelligence cloud
This allows teams to detect subtle deviations like credential misuse or unusual API patterns.
Investigation Built into Detection
Detection without investigation delays response. Effective cloud security monitoring platforms allow analysts to:
- Reconstruct sessions
- Trace attack paths
- Validate alerts instantly
This reduces dwell time and improves decision-making.
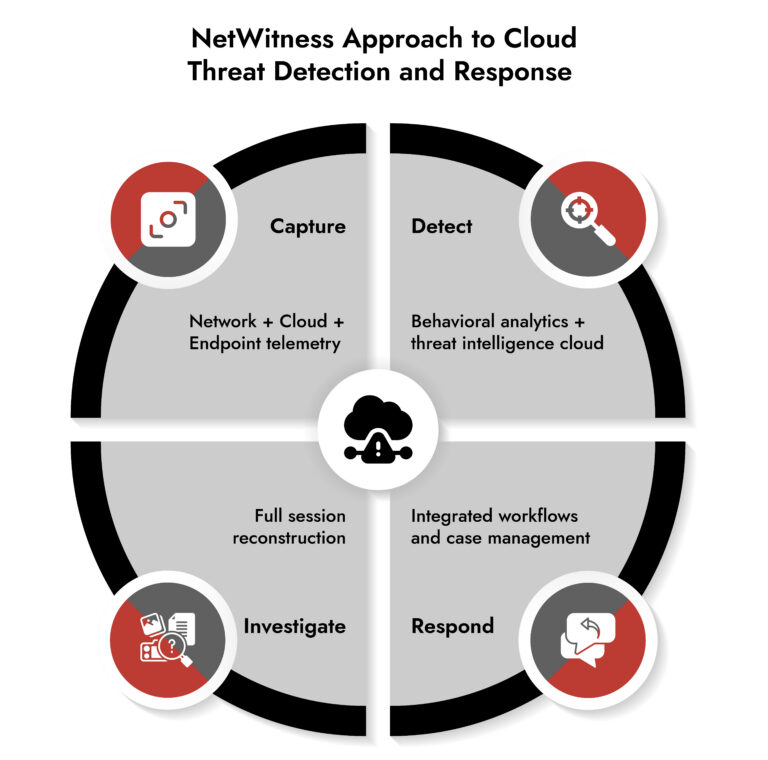
How NetWitness Strengthens Cloud Threat Detection and Response
NetWitness doesn’t treat cloud as a separate problem. It treats it as part of a broader attack surface where network, endpoint, and cloud activity intersect.
Deep, Session-Level Visibility- NetWitness captures:
- Full packet data
- NetFlow and enriched metadata
- Cloud-native telemetry
- Endpoint signals
This gives teams visibility into actual communication patterns, not just recorded events. In a cloud security network, that distinction matters.
Real-Time Behavioral Detection- NetWitness applies advanced analytics to identify:
- Lateral movement across cloud workloads
- Abnormal authentication patterns
- Suspicious data transfers
By combining behavioral models with threat intelligence cloud, it detects threats that traditional cloud threat detection tools miss.
Unified Detection, Investigation, and Response- This is where NetWitness stands out. Instead of switching between tools, analysts can:
- Investigate alerts in context
- Reconstruct full attack sessions
- Execute response actions
All within a single platform. That directly strengthens cloud threat response solutions by reducing friction and response time.
Context That Drives Action- NetWitness doesn’t just generate alerts, it builds narratives. Analysts get:
- Timeline-based attack views
- Session reconstruction
- Correlated multi-source telemetry
This turns cloud security monitoring into a proactive investigation process.
Example: Catching a Compromised Identity in the Cloud
A large enterprise observed a spike in API calls.
Individually, nothing stood out:
- Valid credentials
- Approved access patterns
- Internal traffic only
But NetWitness correlated:
- Login from an unusual geography
- Gradual increase in API activity
- Lateral movement across workloads
This revealed credential compromise early enough to stop escalation. Without unified cloud threat detection and response, this would have blended into normal operations.
Why This Matters Now
Cloud environments aren’t becoming simpler. They’re becoming more dynamic, more distributed, and more dependent on identity and APIs. That increases the attack surface and reduces tolerance for delayed detection.
Frameworks like the NIST Cybersecurity Framework emphasize continuous monitoring and rapid response. But execution depends on tooling that can actually connect the dots. That’s where most gaps exist.
Conclusion
Cloud threat detection and response aren’t about visibility alone. It’s about understanding behavior fast enough to act.
NetWitness brings that together:
- Deep visibility across the cloud security network
- Detection driven by behavior and intelligence
- Investigation and response in a single workflow
If your current stack still relies on stitching signals together manually, you’re already behind the attacker’s pace. It’s time to close that gap before it becomes an incident report.
Frequently Asked Questions
1. What are the key components of a robust cloud threat detection strategy?
A successful cloud threat detection strategy will consist of:
- Common telemetry
- Behavioral analytics
- Integrated threat intelligence
- Built-in investigation workflows across your cloud security solutions
2. What are the best practices for incident response in a hybrid cloud environment?
To efficiently handle incidents that come up in hybrid cloud environments, you should utilize central visibility, playbooks written for incident response, the ability to correlate real-time telemetry, and integrated response capabilities in your cloud solution for respond to cyber threats.
3. How can AI and machine learning enhance cloud threat detection?
Artificial Intelligence (AI) based cloud threat detection tools enhance the number of threats that can be detected through anomaly detection; reduce false positives; and utilize behavioral analysis for the identification of new/unrecognized attack types.
4. How does unified visibility help in cloud security?
By utilizing unified visibility across your cloud security network, teams are capable of tracking the entire attack path, leading to increased accuracy of attack detection and quicker response times.
5. What are the benefits of using a cloud threat detection platform?
A cloud threat detection platform helps in providing increased visibility, removing fatigue from alerts, speeding up investigations, and improving cloud cybersecurity.
6. What role does a SOC play in cloud threat detection?
Security Operations Centers (SOCs) will run cloud threat detection and response through ongoing monitoring, investigation, and response. They will use integrated cloud security monitoring and response tools.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.