Key Takeaways:
- Advanced Persistent Threats (APTs) blend into normal activity without raising strong signals, making them difficult to detect.
- Endpoints are favored by APTs as they offer direct access to user credentials and lateral movement.
- Losing endpoint visibility directly impacts investigations into initial access, credential abuse, and attacker spread.
- Endpoint solutions should offer deep process and memory visibility, behavioral analysis, lateral movement detection, zero-day detection, and contextual alerts to help stop APTs.
- To safeguard from APTs, organizations should focus on visibility, rapid investigation, and continuous tuning.
Advanced Persistent Threats (APTs) don’t announce themselves. By the time you realize something’s wrong, they’ve already been in your environment longer than you’d like to admit. They use credentials that appear legitimate and move stealthily. They exploit the gap between what your tools can see and what your analysts take time to investigate.
One thing is clear: if you lose visibility at the endpoint, Advanced Persistent Threats have already won.
What are Advanced Persistent Threats?
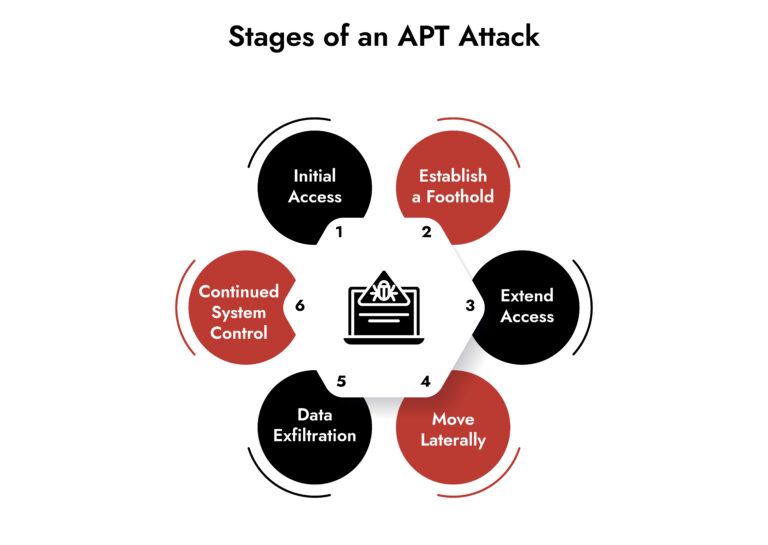
Advanced Persistent Threats are targeted campaigns designed to maintain access while staying below your detection threshold. The objectives vary from espionage and IP theft to long-term access to critical systems.
There are a lot of similarities in Advanced Persistent Threats as well:
- Persistence: They stay in the system for weeks, months, sometimes years.
- Adaptability: They keep adapting to the security measures. If you block one technique, they pivot to another.
- Stealth: They use PowerShell, WMI, PsExec that your system admins use every day. They steal valid credentials instead of exploiting CVEs. They move laterally using protocols you can’t block without breaking the business.
- Human operators: The difference between an APT and commodity malware is that someone is making tactical decisions, watching your response, and adjusting with malicious intent and persistence.
APT activity rarely triggers a high-severity alert on day one. It starts with something ambiguous. A weird PowerShell execution that doesn’t quite fit the user’s normal behavior. A child process that seems slightly off. An endpoint beaconing to an external IP at irregular intervals. Often, analysts close those alerts dozens of times because they didn’t have enough context to justify escalation. And those same alerts become the opening move in an investigation six months later when something finally broke loudly enough to get attention.
Why are Endpoints a Primary Target for Advanced Persistent Threat Attacks?
Endpoints are where attackers establish their foothold and where they do the damage. Endpoints are valuable to adversaries because:
- They give direct access to credentials such as LSASS dumps, browser password stores, and cached Kerberos tickets. With just local admin rights, an attacker can extract what they need without ever touching the network and triggering your SIEM.
- They enable privilege escalation through misconfigurations or vulnerable drivers. APT groups exploit the same local vulns for months because patching endpoints at scale is organizationally hard, and attackers know it.
- Endpoints are the platform for lateral movement. RDP, SMB, WMI—these aren’t attacker tools. They’re enterprise tools. Your network might log the traffic, but only endpoint telemetry tells you what was actually executed and why it matters.
- From a SOC perspective, endpoints are also where visibility gaps hurt the most. Your firewall sees the connection. Your proxy might log the domain. But if you can’t see what process made the connection, what spawned that process, and whether it injected into something else first, you’re investigating blind.
What Endpoint Security Capabilities are Critical for Stopping Advanced Persistent Threats?
Not all endpoint tools are built the same, and plenty of platforms that work fine against opportunistic malware fall apart when a skilled adversary starts testing your defenses. Enterprise endpoint security for APTs helps defend as follows:
Deep Process and Memory Visibility:
Advanced Persistent Threats leverage PowerShell, rundll32, mshta, and regsvr32 because they’re trusted binaries. Therefore, your endpoint solution needs to log full command-line arguments. The malicious behavior is in the arguments, the modules loaded, or what’s happening in memory. Without that visibility, these executions look completely benign.
Your Endpoint Detection and Response solution should provide full script execution details, including obfuscated commands, in-memory payload indicators before they touch disk, process injection attempts, and hollowing techniques.
Behavioral Analysis:
Signature-based detection does not work against Advanced Persistent Threats. It needs behavioral models that flag abnormal process trees, unusual parent-child relationships, and execution patterns that deviate from baseline.
The drawback is the large volume of alerts, which can drown a SOC. But if an Endpoint Detection and Response solution enriches alerts with context, it makes the job easier for analysts.
Lateral Movement Detection:
Network-based lateral movement detection can’t distinguish between legitimate admin activity and an attacker using stolen credentials. Endpoint telemetry can. It shows you credential reuse patterns, which accounts are executing remote commands, and what services are being created across hosts.
This matters because stopping Advanced Persistent Threats is about catching them before they achieve domain dominance. Once they control your domain controllers, you’re in full incident response mode, and the damage is already done.
Zero-Day Threat Detection:
The best endpoint solutions identify exploit-like behavior, abnormal privilege escalation, and post-exploitation techniques regardless of whether the specific malware is known. The detection strategy should not depend on knowing what malware looks like.
Contextual Alerts:
Advanced Persistent Threats generate weak signals over long periods. Therefore, analysts need information about timelines, entity relationships, and cross-host correlation to connect the dots.
Though alert fatigue is real, it’s the lack of context that is a bigger problem.
For instance, an alert that says “suspicious process execution” is very vague. But if it shows the process tree, the user’s recent activity, related alerts on other endpoints, and a timeline of what happened before and after? Then the analyst can decide whether to raise an alarm.
What Actually Works Against Advanced Persistent Threats
Advanced Persistent Threats are sophisticated, patient, and purpose-built to evade the controls most organizations deploy. But they’re not unstoppable.
The organizations that successfully defend against Advanced Persistent Threats share a few traits:
- They prioritize visibility over prevention-only strategies and assume that attackers will get in. The focus, therefore, is on reducing dwell time, not pretending the perimeter is impenetrable.
- They invest in their SOC endpoint visibility. They treat endpoint security for APTs as an ongoing improvement. Tuning detections, reducing false positives, and closing visibility gaps is continuous activity.
- If you take one thing from this, let it be this: With the right visibility, detection, and response, Advanced Persistent Threats don’t have to turn into long-running breaches. They can be identified early and stopped before they take hold.
Frequently Asked Questions
1. Why are Endpoints the Primary Target for APT Attacks?
Endpoints have a lot of data: users’ credentials, application data, etc., making them the highest-value target for persistent attackers. Endpoints give Advanced Persistent Threats what they need: direct access to credentials through LSASS, browser stores, or token theft; execution of native tools without dropping obvious malware; privilege escalation through misconfigurations or vulnerable drivers; and stealthy lateral movement using tools like RDP, SMB, WMI, or PsExec. From a SOC perspective, endpoints are also where detection gaps hurt most. Network controls show you traffic.
Modern ransomware attacks are faster, stealthier, and more automated, making early detection critical.
2. How does EDR Help Defend Against APT Attacks?
EDR works against Advanced Persistent Threats because it shifts the question from “Is this file malicious?” to “Does this activity make sense given this endpoint, user, and context?” Advanced Persistent Threats avoid detection by blending into normal system behavior. They use legitimate tools, stolen credentials, and custom malware that rarely match known signatures. Endpoint Detection and Response is effective because it focuses on behavior over time, zero-day detection, lateral movement, and not just static indicators.
By the time encryption starts, the attacker may already have domain-level access. That is why detecting pre-encryption behaviors is essential.
3. What Role Does Automation Play in Stopping APT Attacks?
Automation helps analysts by buying them time, which is critical when you’re dealing with a patient’s adversary. Effective automation includes automated triage, enriching alerts with process ancestry, user and asset criticality, and historical behavior to reduce time-to-understand from hours to minutes.
Rolling the Dice: Ransomware in the Gaming Industry
Discover how ransomware attacks hit gaming companies, how attackers moved laterally, and why network visibility is key. Learn real-world lessons and strategies to detect, respond, and protect critical systems.






