How Attackers Exploit Network Protocols and What Actually Stops Them
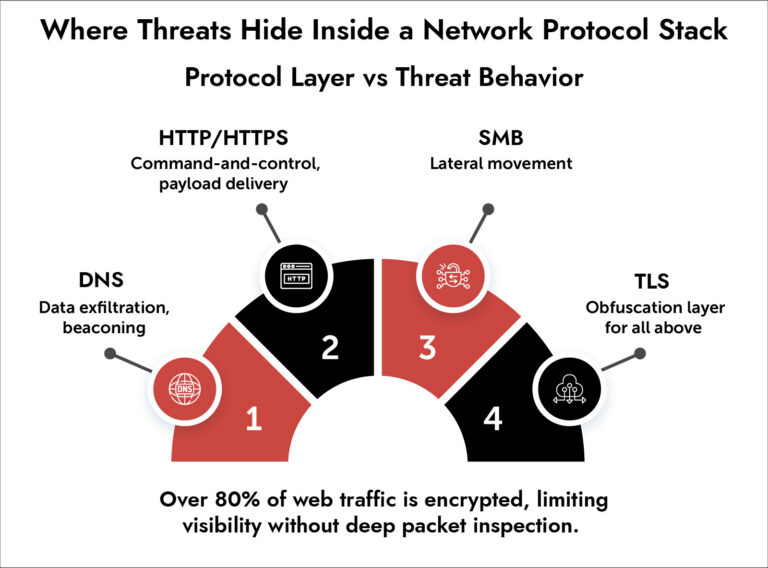
Today’s cybercriminals do not have to compromise a network protocol as they can work within its context. Today, DNS, HTTP, and TLS act as the secret tunnels through which command and control communications and lateral movement take place. Traditional security controls would be unable to detect such attacks since they would appear benign on the surface. An effective defense would require an understanding of all network protocols.
Introduction
There is one unpleasant reality, attackers no longer require zero-days because your network protocol stack will provide them with all the necessary coverage. They will exploit HTTP requests to transfer data via DNS and communicate laterally via SMB, and nobody will even suspect anything.
It means that today’s network security threats cannot be tackled through traditional means such as IP blocking. What we must do is understand the attacker’s intentions among legitimate network traffic.
Modern environments generate massive volumes of network traffic analysis data. But without the right depth and context, it becomes noise. Attackers know this. They design campaigns specifically to exploit blind spots inside everyday network protocol behavior.
Let’s break down how this works and what actually stops it.
Why Attackers Exploit the Network Protocol Layer
Attackers prefer targeting the network protocol layer due to its trustworthiness, consistency, and lack of scrutiny.
HTTP, DNS, and TLS, among other protocols, form the bedrock of enterprise communications. They cannot be taken down, thus making for ideal cover.
What this enables:
- Blending malicious traffic with legitimate user activity.
- Evading perimeter-based threat detection systems.
- Maintaining persistence without triggering alerts.
- Moving laterally using approved communication paths.
In accordance with NIST guidelines on network visibility, cybercriminals are now using protocol misuse along with exploitation. Moreover, CISA warnings in 2024 stress that DNS and HTTPS are the most common means used by cybercriminals to conduct their activities in secret.
This is not a tooling gap. It’s a visibility gap within the network protocol layer.
Common Network Protocol Threats Hiding in Plain Sight
Most network protocol threats don’t look malicious at first glance. That’s the point.
1. DNS tunneling- Attackers encode data inside DNS queries and responses. Since DNS traffic is rarely inspected deeply, exfiltration goes unnoticed. Example: Malware sends encoded data in subdomain queries like data.exfiltration.attacker.com.
2. HTTP/S command-and-control – Attackers use standard web traffic to communicate with control servers. These requests mimic legitimate browsing behavior. What it looks like:
- Normal GET/POST requests
- Valid headers
- Encrypted payloads
3. SMB-based lateral movement – Once inside, attackers pivot across systems using SMB. This often blends with routine file-sharing activity.
4. TLS encryption abuse – Encryption protects users but also hides attackers. Without visibility into encrypted traffic, network threat detection becomes guesswork.
Why Traditional Network Monitoring Fails
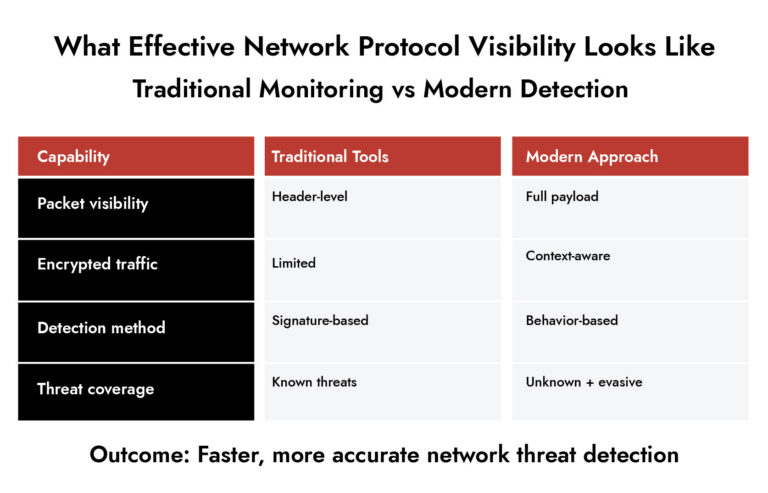
Most network monitoring tools operate at a surface level. They track traffic volume, endpoints, and known signatures. That’s no longer enough.
Attackers now rely on:
- Legitimate ports (80, 443, 53)
- Valid certificates
- Normal traffic timing patterns
This creates a dangerous illusion of normalcy.
What’s missing:
- Contextual analysis of network protocol behavior
- Payload-level inspection
- Behavioral baselines across sessions
Make Smarter Security Investments—Faster
- Standardize vendor evaluation with a comprehensive RFI checklist.
- Compare platforms based on real-world detection, visibility, and response capabilities.
- Reduce risk by identifying gaps before deployment.
- Empower security leaders with actionable insights from NetWitness.
The Role of Deep Packet Inspection in Exposing Hidden Threats
If attackers hide inside protocols, you need visibility inside those protocols.
That’s where deep packet inspection (DPI) becomes essential.
DPI doesn’t just look at headers. It inspects the full payload and context of each network protocol interaction.
What DPI reveals:
- Hidden data within DNS queries
- Suspicious patterns inside HTTP payloads
- Anomalous SMB behavior
- Indicators inside encrypted sessions (via metadata and decryption where applicable)
But DPI alone isn’t enough.
You need:
- Behavioral analytics
- Session reconstruction
- Correlation across network and endpoint data
That combination transforms raw network traffic analysis into actionable threat detection.
How Modern Threat Detection Actually Works
Effective network threat detection today relies on layering intelligence across the network protocol stack.
It’s not one technique. It’s a combination.
Core components:
- Behavioral Analysis – Establishes a baseline of normal network protocol activity and flags deviations.
- Session reconstruction – Rebuilds entire sessions across packets to understand attacker intent.
- Metadata analysis – Extracts patterns even from encrypted traffic.
- Threat intelligence correlation – Connects activity to known attacker infrastructure and tactics.
This approach aligns with frameworks from MITRE, which emphasize behavior over signatures.
Where NetWitness Fits in
Most tools stop at detection signals. They don’t provide enough depth to investigate.
NetWitness approaches this differently by focusing on full-spectrum visibility across the network protocol layer.
What stands out:
- Full packet capture for deep forensic analysis.
- Real-time network traffic analysis with session reconstruction.
- Integrated threat detection across network, endpoint, and logs.
- Visibility into encrypted traffic (via 3rd-party integration) and analysis of decrypted or enriched metadata.
This matters because identifying network protocol threats is only half the job. You also need to understand how the attack unfolded and what it touched.
That’s where investigation speed improves and response becomes precise.
The Operational Reality: What Teams Should Prioritize
If your detection strategy still treats protocols as trusted, it’s outdated.
Focus areas that actually move the needle:
- Inspect every critical network protocol, not just endpoints.
- Invest in deep packet inspection with behavioral context.
- Correlate network data with endpoint and identity signals.
- Monitor DNS and encrypted traffic as primary threat vectors.
- Build detection logic around behavior, not signatures.
This is not about adding more alerts. It’s about making your existing visibility smarter.
Conclusion
Attackers aren’t forcing their way into networks anymore. They’re walking in through trusted network protocol channels and staying invisible. That changes how you think about defense.
It’s no longer about blocking threats at the edge. It’s about understanding behavior inside the traffic you already allow. Organizations that invest in deep network traffic analysis, context-aware threat detection and protocol-level visibility will catch what others miss.
The rest will keep chasing alerts that never tell the full story.
Frequently Asked Questions
1. What are network protocols in cybersecurity?
A network protocol defines how data is transmitted across systems. In cybersecurity, it forms the foundation of communication but also becomes a channel for network security threats when abused.
2. How do modern threats hide in network protocols?
Attackers embed malicious activity within normal network protocol behavior – using DNS for exfiltration, HTTP for command-and-control, and TLS to encrypt everything. This makes cyber threats in network protocols difficult to detect without deep analysis.
3. What are the most widely used network protocols in enterprise environments?
Some examples include HTTP/HTTPS, DNS, SMB, FTP, and TLS. These are extremely important, as each can be used for network protocol threats if not monitored carefully.
4. Which companies offer network protocol analyzer tools for troubleshooting?
There are different cybersecurity firms that develop such network protocol analysis and inspection software. One example is NetWitness, which is known for its emphasis on comprehensive network monitoring.
5. How to configure secure network protocols for remote work solutions?
It is necessary to establish encrypted protocols, such as TLS 1.3, and to have proper authentication and monitoring of the network with behavioral analysis. This is not all that can be done.
6. Why is deep packet inspection important for network threat detection?
By using deep packet inspection, one gets access to what really goes through the network protocol communication because one sees its content and not only its header.
What to Look for in a Unified Security Platform
- Cut through tool sprawl with a practical evaluation framework.
- Compare platforms based on visibility, detection accuracy, and automation.
- Validate real-world performance across hybrid and cloud environments.
- Make confident, risk-aligned security decisions.