What Modern Threat Detection Tools Must Deliver in 2026 ?
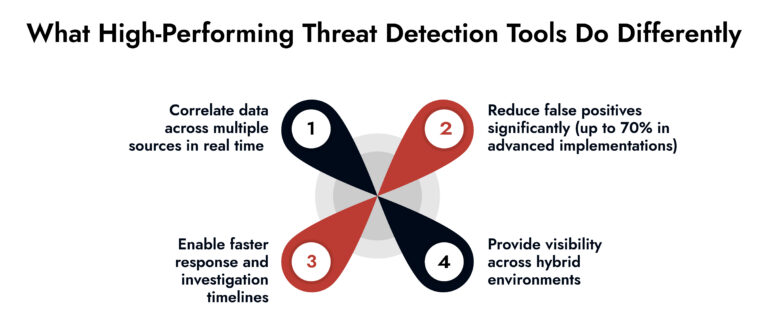
- Threat detection tools must move from alerting to real-time investigation and response orchestration.
- Unified visibility across network, endpoint, and cloud is now non-negotiable.
- Behavioral analytics and AI-driven correlation reduce alert fatigue and improve detection accuracy.
- Scalability and data retention directly impact forensic depth and compliance readiness.
- Integrated response capabilities separate modern platforms from legacy monitoring tools.
Introduction
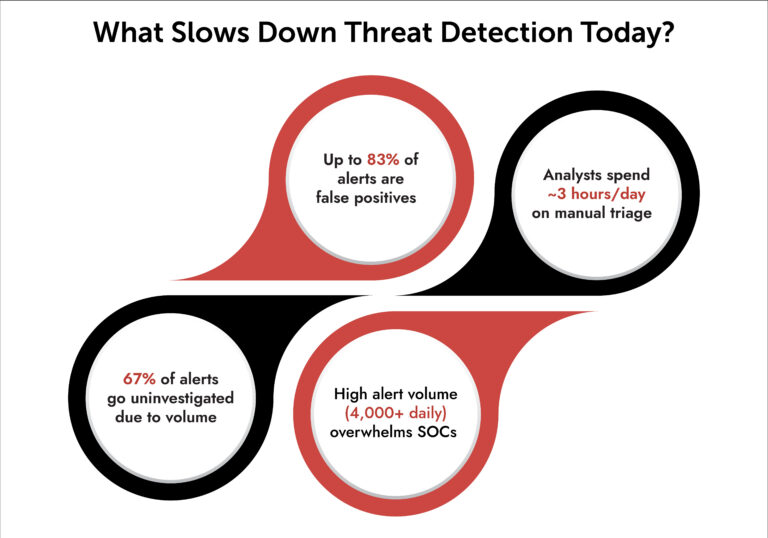
The purpose of threat detection tools has evolved past simply identifying potentially malicious activities. There is an expectation for these solutions to also provide an explanation of why those activities are concerning, to prioritize them, and to enable an organization to take action as soon as possible. The quickening of this trend can be attributed to the increasing speed of adversaries and the increasing complexity of hybrid environments.
For large enterprises, however, the reality is that many still deploy threat detection solutions as a series of fragmented, disparate stack of applications. Employees analyze logs stored in one location, network telemetry stored in another separate location, and cloud visibility stored in yet another distinct location. As a result, organizations are experiencing delays in identifying threats, missing threat signals, and having analysts overwhelmed with noise.
What is the implication of this? In simple terms, if your threat detection tools cannot merge, analyze, and address identified threats from one application, you are lagging in the threat detection competition.
Now let’s examine the foremost 10 features that will distinguish cutting-edge threat detection tools from others in 2026.
10 Capabilities That Define High-Performing Threat Detection Tools
1. Unified Threat Detection across all Environments
Modern threat detection tools must deliver unified visibility across network, endpoint, and cloud. Anything less creates blind spots attackers exploit.
A strong cybersecurity threat detection platform should:
- Ingest logs, packets, endpoint data, and cloud telemetry in one place
- Correlate activity across environments in real time
- Provide a single investigation view instead of siloed dashboards
According to National Institute of Standards and Technology (NIST), incomplete visibility remains one of the top reasons incidents go undetected. Example: A credential misuse attempt might look harmless in endpoint logs. Combine it with unusual lateral movement in network traffic, and it becomes a high-risk signal.
2. Real-Time Detection with Deep Context
Speed without context is noise. Context without speed is useless. Advanced threat detection tools must:
- Detect anomalies in real time
- Enrich alerts with user, asset, and behavioral context
- Map activity to frameworks like MITRE ATT&CK
Without context, analysts waste time validating alerts. With it, they move directly to action.
3. Advanced Behavioral Analytics (UEBA)
Signature-based detection is no longer enough. Attackers don’t reuse obvious patterns.
Behavioral analytics in threat detection tools should:
- Establish baselines for users and systems
- Detect subtle deviations
- Identify insider threats and compromised accounts
The shift toward User and Entity Behavior Analytics (UEBA) is backed by Gartner, which highlights behavioral detection as a core capability for modern SOCs.
4. Integrated Threat Detection and Response Tools
Detection without response creates operational gaps. Threat detection and response tools must:
- Enable automated containment actions
- Integrate with SOAR workflows
- Support guided response playbooks
This reduces dwell time, which remains a critical issue. Industry reports show attackers still operate undetected for days or weeks in many environments.
5. Full Packet Capture for Deep Forensics
Logs tell you what happened. Packets tell you how. High-performing network threat detection software should:
- Capture full packet data
- Allow retrospective analysis
- Reconstruct sessions for investigation
This capability becomes critical during incident response. When logs fail, packets provide ground truth.
6. Scalable Data Ingestion and Retention
Threat detection tools must scale with data growth.
Enterprises now process:
- Petabytes of logs
- High-volume network telemetry
- Continuous cloud activity
A strong platform should:
- Handle high ingestion rates without performance drop
- Support long-term data retention
- Enable fast search across historical data
This directly impacts forensic capability and compliance readiness.
Unify Security Across Hybrid Environments
- Gain complete visibility across cloud, on-prem, and endpoints.
- Detect threats faster with correlated insights across all layers.
- Reduce complexity with a single, integrated security platform.
- Strengthen your defenses with NetWitness unified security
7. Cloud-Native Detection Capabilities
Cloud environments introduce new attack surfaces. Cloud threat detection and response capabilities must:
- Monitor APIs, workloads, and identities
- Detect misconfigurations and abuse
- Correlate cloud activity with on-prem signals
According to Cybersecurity and Infrastructure Security Agency (CISA), misconfigurations remain a leading cause of cloud breaches.
8. AI-Driven Alert Prioritization
Let’s be honest. Alert fatigue is still killing SOC efficiency. Advanced threat detection tools should:
- Use AI to prioritize high-risk alerts
- Reduce duplicate signals
- Highlight attack chains instead of isolated events
The goal is not more alerts. It’s better decisions.
9. Open Integration and Ecosystem Compatibility
No enterprise runs a single tool. Your cybersecurity threat detection platform must:
- Integrate with SIEM, SOAR, EDR, and NDR systems
- Support APIs for customization
- Fit into existing workflows
Closed systems create friction. Open architectures create efficiency.
10. Investigation-First Design
Most tools focus on detection. The best ones focus on investigation. Threat detection tools should:
- Provide intuitive investigation workflows
- Link related events automatically
- Offer visual timelines of attacks
This reduces analyst effort and speeds up resolution.
Where NetWitness Fits In
A modern cybersecurity threat detection platform must go beyond alerting. It must unify detection, investigation, and response. That’s where platforms like NetWitness stand out.
NetWitness delivers:
- Unified threat detection across network, endpoint, and logs
- Deep visibility with full packet capture
- Integrated threat detection and response tools
- AI-driven analytics and behavioral detection
- Scalable architecture for enterprise environments
Instead of stitching together multiple tools, it provides a cohesive system designed for real-world SOC operations.
Conclusion
In 2026 the sole benchmark for threat detection will be speed; how quickly can teams transition from detection to decision. All other metrics will be inconsequential.
The transformation is evident:
- Will become from isolated tools to integrated platforms
- Will become from alerts to actionable intelligence.
- Will become from manual processes to automated responses.
Organizations that are able to transition will see a decline in risk exposure; organizations that don’t will continue to react and not get ahead. If your current stack still appears disconnected, you should reevaluate your foundation.
Frequently Asked Questions
1. What are threat detection tools in cybersecurity?
Threat detection tools are cybersecurity resources that help detect and identify suspected malicious activity across all network types (i.e., endpoints, data centre, public/private cloud, etc.). More recent versions of the threat detection tool also support providing a mechanism for management to investigate and respond to incidents in addition to merely notifying management about incidents.
2. Why do threat detection tools need advanced features in 2026?
The reason that these types of tools will require advanced capabilities in the year 2026 is because of the increase in stealthy, multi-staged attacks being deployed by perpetrators. Detection techniques based on standard detection criteria cannot identify patterns that exhibit the characteristics described above without utilizing behavioral analytics capabilities, AI correlation, and unified visibility.
3. How should enterprises evaluate threat detection tools for 2026?
Enterprises should evaluate threat detection tools based on:
- Unified visibility
- Detection accuracy
- Investigation capabilities
- Response integration
- Scalability
A strong cybersecurity threat detection platform must support all five.
4. What is the most important feature of a modern threat detection tool?
The most important feature is unified threat detection. Without it, organizations cannot correlate signals across environments, leading to missed threats and delayed responses.
5. Why is scalability critical for enterprise threat detection tools?
Enterprise environments generate massive volumes of data. Threat detection tools must scale to process and retain this data without performance issues, enabling effective detection and forensic analysis.
360° Cybersecurity with NetWitness Platform
– Unrivaled visibility into your organization’s data
– Advanced behavioral analytics and threat intelligence
– Threat detections and response actionable with the most complete toolset