Key Takeaways
- A contemporary approach to security risk assessment must look beyond compliance-style lists and focus instead on actual vulnerabilities in identity, cloud, OT, and organizational networks.
- Assessing the attack surface and threat risks shows where attackers are most likely to succeed. It does more than just list where vulnerabilities exist.
- Continuous monitoring, data collection, and oversight of cyber threats aid in minimizing the impact of breaches and improving decision-making capabilities.
- Organizations that incorporate detection depth, business impact analysis, and quantifiable prioritization excel compared to those that depend on occasional evaluations.
- Risk accumulates in areas of unawareness. Successful enterprise cybersecurity relies on identifying them before attackers can.
Introduction
Most breaches do not begin with a sophisticated zero-day. They begin with something overlooked. An exposed API. A forgotten service account. A misconfigured cloud workload. A remote access tool inside the enterprise network that nobody reviewed in months.
That is why a disciplined cybersecurity risk assessment matters. Not as a compliance checkbox. Not an annual report. However, as a dynamic structure that addresses a more challenging query: Where is your organizational cybersecurity risk currently focused?
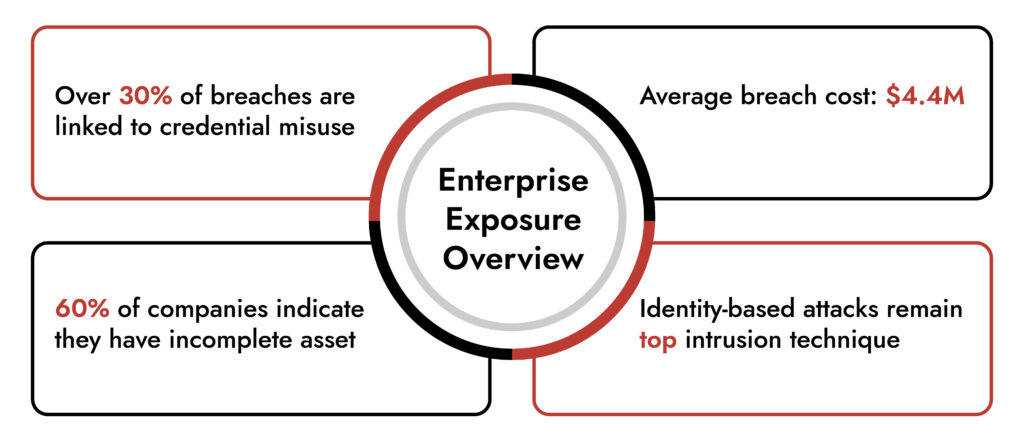
In 2024, IBM’s Cost of a Data Breach Report estimated the worldwide average cost of a breach at $4.45 million. CISA persists in alerting identity exploitation and lateral movement as primary intrusion methods. NIST’s revised Cybersecurity Framework 2.0 highlights governance and ongoing risk awareness. The message is evident. The nature of risk has changed. Your evaluation model must adapt accordingly.
Let’s analyze it step by step.
Why Traditional Cybersecurity Risk Assessment Models Miss Real Risk
Most organizations perform a cybersecurity risk assessment through periodic reviews, vulnerability scans, and policy audits. That approach surfaces weaknesses. It does not always surface exposure.
Here’s the problem:
- Vulnerabilities do not equal risk.
- Asset inventories are rarely complete.
- Threat models lag real adversary behavior.
- Operational technology and cloud environments sit outside traditional visibility.
A modern cybersecurity risk assessment must integrate:
- Attack surface analysis
- Identity and privilege mapping
- Enterprise threat risk analysis
- Network telemetry
- Business impact modeling
Without these, enterprise cyber risk management becomes theoretical.
Where Cybersecurity Risk Actually Hides in 2026
Cybersecurity risk concentrates in specific domains. Leaders who understand these domains gain control.
1. Identity and Privilege Sprawl
Compromised credentials remain a primary breach vector. According to Verizon’s 2024 DBIR, credential abuse accounts for nearly one-third of confirmed breaches. Key exposure areas:
- Stale admin accounts
- Excessive service permissions
- Poor MFA enforcement
- Token misuse in cloud environments
A serious cybersecurity risk assessment must map privileges across the enterprise network and cloud control planes.
2. The Expanding Enterprise Attack Surface
Hybrid infrastructure increases exposure. Attack surface analysis now requires visibility into:
- Public-facing applications
- Cloud workloads
- Remote endpoints
- Third-party integrations
- OT environments
If you cannot enumerate it, you cannot secure it
3. East-West Traffic Inside the Enterprise Network
Perimeter thinking fails inside modern enterprise cybersecurity architectures. Lateral movement happens quietly. Attackers exploit:
- Unsegmented network zones
- Insecure service accounts
- Weak internal authentication
- Legacy protocols
A mature cybersecurity risk assessment evaluates east-west traffic visibility, not just ingress points.
4. Operational Technology and Industrial Systems
Manufacturing, energy, and utilities environments carry unique exposure. OT systems often lack modern monitoring controls. Risk concentrates in:
- Legacy PLC systems
- Flat network architectures
- Insecure remote access
- Lack of continuous inspection
Organizations adopting enterprise cybersecurity solutions must unify IT and OT visibility to avoid blind spots.
Make Way for the Intelligent SOC with NetWitness®
-Turn data overload into actionable intelligence.
-Accelerate detection with AI-driven insights.
-Empower analysts with enriched, contextual decision-making.
-Build a smarter, faster, more resilient SOC.
A Practical Cybersecurity Risk Assessment Framework
Here is a structured framework built for real-world enterprise cyber risk management.
Step 1: Establish Business-Centric Risk Context
Define critical assets:
- Revenue-generating systems
- Sensitive data repositories
- Industrial control systems
- Customer-facing platforms
Map impact scenarios. Align with board-level priorities. Without business alignment, a cybersecurity risk assessment becomes technical noise.
Step 2: Conduct Attack Surface Analysis
Enumerate internal and external assets. Validate inventory accuracy. Include:
- Cloud-native workloads
- Containers
- APIs
- Remote workforce devices
- Third-party exposure
Attack surface analysis should integrate asset discovery with exposure scoring.
Step 3: Perform Enterprise Threat Risk Analysis
Overlay intelligence. Ask:
- Which threat actors target your sector?
- What TTPs align with your environment?
- Where do current controls fail detection?
Use frameworks such as MITRE ATT&CK to evaluate coverage gaps. Enterprise threat risk analysis ensures that your cybersecurity risk assessment reflects adversary behavior, not hypothetical scenarios.
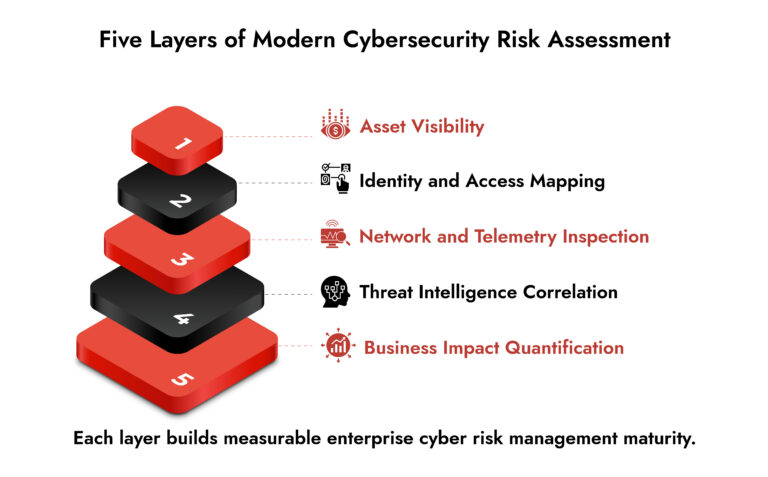
Step 4: Evaluate Detection and Response Depth
You cannot reduce risk you cannot detect. Assess:
- Log coverage across enterprise network segments
- Packet capture capabilities
- Endpoint telemetry depth
- Cloud monitoring integration
- Incident response readiness
According to NIST guidance, detection and response capability directly reduce breach impact cost.
Step 5: Quantify and Prioritize Risk
Translate findings into decision-grade metrics. Prioritize:
- High exposure + high business impact
- Low detectability + high exploit likelihood
- Identity pathways enabling privilege escalation
An effective cybersecurity risk assessment produces an action roadmap, not a static report.
Aligning Enterprise Cyber Risk Management with Continuous Monitoring
Risk assessment must evolve from periodic audits to continuous evaluation. Modern enterprise cybersecurity demands:
- Unified data across network, endpoint, cloud, and OT
- Automated correlation and analytics
- Integrated cybersecurity services support
- Incident simulation and tabletop exercises
- Ongoing cybersecurity awareness programs
Cybersecurity awareness strengthens human defense layers. But technical telemetry drives measurable control.
How NetWitness Supports Deep Enterprise Risk Visibility
Reducing organizational exposure requires visibility at scale. NetWitness delivers:
- Unified data ingestion across enterprise network, endpoint, cloud, and operational technology environments
- Deep packet inspection for forensic replay
- Advanced analytics aligned to MITRE ATT&CK
- Integrated threat detection and response capabilities
For organizations operating industrial systems, NetWitness OT security modules provide specialized monitoring tailored to operational technology protocols and segmentation models.
This level of telemetry strengthens enterprise cyber risk management by converting assumptions into evidence. A meaningful cybersecurity risk assessment becomes possible when visibility matches enterprise complexity.
Measuring Success: What Strong Risk Governance Looks Like
High-performing security programs demonstrate:
- Continuous attack surface analysis
- Documented reduction in high-impact risk scenarios
- Measurable mean time to detect and respond
- Executive-level risk reporting tied to financial impact
- Integrated cybersecurity services across business units
They do not chase compliance scores. They pursue measurable exposure reduction.
The Cost of Getting it Wrong
A weak cybersecurity risk assessment produces three predictable failures:
- Overinvestment in low-impact controls
- Underinvestment in detection and identity governance
- Executive misalignment on risk tolerance
Gartner research consistently shows that organizations that integrate risk governance into business strategy experience lower breach impact and faster recovery. Risk misjudgment costs more than tools ever will.
Conclusion
Cybersecurity risk does not distribute evenly. It clusters in identity pathways, unmanaged assets, and blind network segments. A modern cybersecurity risk assessment demands continuous attack surface analysis, enterprise threat risk analysis, and business-aligned prioritization. It requires visibility deep inside the enterprise network and across operational environments.
Organizations that treat risk as a living, measurable discipline build resilience others only report on. If your current framework cannot pinpoint where exposure concentrates today, it may be time to recalibrate how you assess risk.
If you want to test the maturity of your current risk framework or explore deeper visibility across IT and OT environments, start by evaluating where your monitoring truly begins and where it silently ends.
Frequently Asked Questions
1. What is organizational cybersecurity risk assessment?
An organizational cybersecurity risk evaluation involves pinpointing essential assets, comprehending potential attack methods, and assessing the business ramifications if these assets are breached. It goes beyond listing vulnerabilities. It connects real threats to real weaknesses and measures the consequences. The goal is simple: make clear, informed decisions about where to reduce risk first.
2. What are the 5 steps of security risk assessment?
A practical cybersecurity risk assessment usually follows five core steps:
- Define your most critical systems and data
- Map your full attack surface across cloud, endpoint, OT, and the enterprise network
- Analyze relevant threats and attacker techniques
- Assess how well you detect and respond
- Prioritize risks based on impact and likelihood
Simple structure. Serious discipline. That’s what makes it effective.
3. Why do companies conduct cybersecurity risk assessments?
Many organizations conduct cybersecurity risk assessments because guessing is costly; it costs millions of dollars to recover from a breach, disrupts normal business operations and erodes customer trust. The benefit of conducting a structured assessment allows organizations to focus the organization’s resources in the areas that actually reduce their risk of exposure; they also support compliance reporting to the organization’s board of directors as well as support long-term cyber risk management efforts of the organization. In short, conducting an assessment is the first step toward shifting your organization’s focus to becoming a proactive and strategic approach to security.
4. How to perform a cybersecurity risk assessment?
To perform a successful cybersecurity risk evaluation, start with a comprehensive grasp of your organization’s assets and the methods of their access. Subsequently, you will identify your organization’s attack surfaces, encompassing external (cloud-based) and internal (enterprise) pathways. This information can then be utilized to incorporate further threat intelligence regarding potential attackers of your assets and their possible methods for doing so. Ultimately, you can evaluate the potential consequences of an attack occurring and prioritize actions according to the likelihood of it happening. Travel ought to be guided by events; thus, after finishing the initial risk evaluations on your assets, it’s essential to conduct them regularly, at least once.
5. What is the purpose of a risk assessment in cybersecurity?
The goal of conducting a cybersecurity risk assessment is to achieve clarity. An organization must understand the level of threat facing them, the level of risk (acceptable or unacceptable), and whether the risk is within management’s ability to manage. Cybersecurity risk assessments must also provide a basis by which decisions regarding technical solutions are made based on their business value. Without having clarity on the risks being taken by an organization, it becomes all too easy to waste valuable time and resources trying to address low-impact issues.
6. Where does cybersecurity risk typically originate?
Cybersecurity risks are usually created where visibility ends (for example: unused credentials, unsegmented network zones, exposed cloud services and/or third parties). Cybersecurity risks frequently exist inside of the enterprise network rather than at the perimeter of the enterprise. The enterprise’s limited monitoring ability and lack of awareness of cybersecurity issues compound these risks. Most areas of risk will go unnoticed until someone is willing to invest their time to identify them.
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.