What are NDR solutions and how do they help with threat detection?
NDR solutions (Network Detection and Response) use advanced network traffic analysis, behavioral analytics, and threat intelligence to detect, investigate, and respond to cyber threats in real time. Unlike traditional tools, NDR cybersecurity platforms provide deep network visibility, reduce false positives, and deliver actionable insights that help SOC teams accelerate threat detection and response across on-prem, cloud, and hybrid environments.
Introduction
If there’s one thing every SOC team struggles with, it’s not a lack of tools. It’s too many alerts with too little meaning.
Thousands of notifications flood dashboards daily across network security monitoring, SIEMs, and endpoint tools. But here’s the problem: most alerts lack context, and that slows down real threat detection and response.
What this really means is analysts spend more time sorting noise than stopping threats. That’s where NDR solutions step in.
Why Alert Fatigue Happens in the First Place
Most SOC teams rely on a combination of endpoint detection, firewall logs, and SIEM alerts to monitor threats. These tools generate thousands of alerts daily. Many are duplicates or low priority, some lack context, and others are outright false positives.
The result? Analysts waste hours triaging non-critical events. The real problem is twofold:
- Lack of Context:Alerts without network contextfail to show the full kill chain or lateral movement.
- Limited Visibility:Endpoint or log-only monitoringmisses threats that move across unmanaged assets or encrypted traffic.
What this really means is traditional detection approaches force analysts to piece together fragmented information to understand what’s happening. That’s a recipe for burnout.
Enter NDR Solutions: Moving Beyond Detection to Real Insight
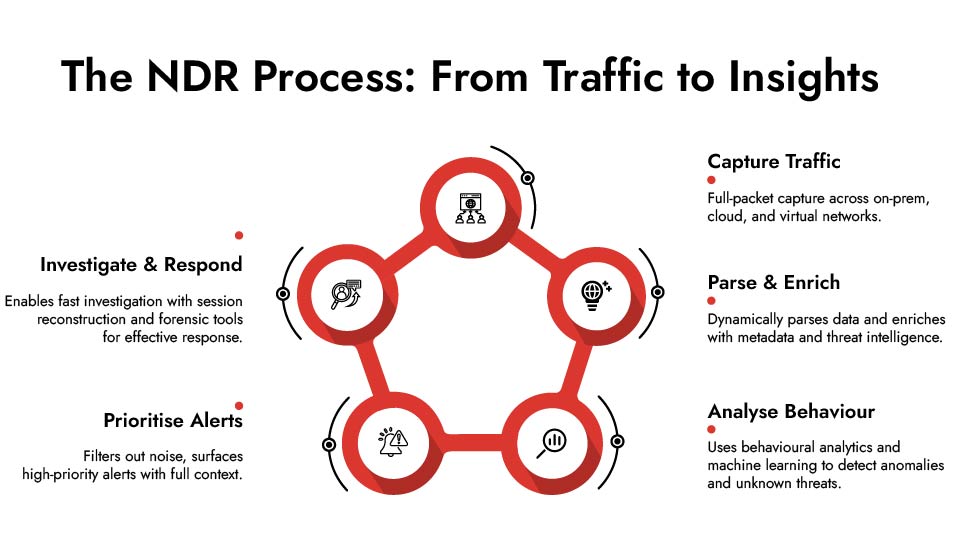
Network Detection and Response (NDR) solutions provide deep visibility into network traffic, turning it into actionable intelligence. Instead of simply flagging suspicious IPs, NDR tools like NetWitness NDR solutions reconstruct entire network sessions, decode hundreds of protocols, and enrich data with threat intelligence in real time.
Here’s how that delivers insights, not noise.
1. Comprehensive Network Traffic Analysis:
NetWitness NDR starts with full-packet capture and advanced network traffic analysis. It dynamically parses and enriches packet data at the time of capture, generating rich metadata for every interaction on your network.
Why does this matter? Because metadata accelerates analysis. Instead of sifting through gigabytes of raw packet data, analysts see summarised, contextual information instantly – like application type, SSL cert details, DNS queries, and user-agent strings.
This enables:
- Quick filtering of benign traffic.
- Focus on suspicious sessions.
- Faster pivoting during investigations.
No more guesswork. You see exactly who connected to what, when, and how.
2. Reducing False Positives with Behavioural Analytics:
Traditional signature-based detection has a major weakness – it only flags known threats. NetWitness combines behavioural analytics, machine learning, and threat intelligence to detect anomalies and unknown attacks in real time.
For example, it learns what “normal” looks like on your network and flags deviations – like an HR employee suddenly initiating RDP sessions across finance servers at 2 AM. This cuts down noise and surfaces genuine threats that traditional tools miss.
The impact? Fewer irrelevant alerts, more high-fidelity detections, and analysts who can focus on stopping threats instead of triaging endless noise.
3. Delivering Real Network Threat Visibility:
The reality of today’s IT environment is that it’s distributed, hybrid, and dynamic. With remote work, cloud apps, and containerised workloads, you can’t rely on endpoint agents alone.
NDR in cybersecurity provide deep network threat visibility across:
- On-premises data centres.
- Public and private cloud environments.
- Virtualised and containerised infrastructures.
- VPN tunnels and SD-WAN traffic.
By deploying lightweight collection components wherever your workloads run, NetWitness ensures pervasive coverage. You see threats moving laterally across environments, even if endpoints are unmanaged or unmonitored.
4. Powerful Network Forensics Capabilities:
Detection is only half the battle. Once an alert is raised, analysts need to investigate quickly and contain the threat before damage spreads.
Here’s where NetWitness excels. Its network forensics capabilities allow full reconstruction of network sessions. Analysts can replay a compromised user’s exact activity, decode application protocols, and examine file transfers in detail.
Think of it as CCTV footage for your network. You’re not just told something suspicious happened – you can see precisely what it was.
This accelerates:
- Root cause analysis.
- Impact assessment.
- Incident scoping.
- Threat eradication.
And ultimately, it shortens your mean time to respond (MTTR) drastically.
5. Native Decoding and Encrypted Traffic Visibility:
Attackers hide behind encryption, and many detection tools struggle here. NetWitness provides native decoding for hundreds of protocols and integrates with third-party decryption solutions where needed.
The result? Encrypted traffic isn’t a blind spot anymore. Whether it’s TLS, SMB, or proprietary protocols, NetWitness decodes and analyses them without performance bottlenecks, ensuring no part of your network is invisible.
6. Simplified Investigation with Intuitive Visualisations:
All these capabilities are powerful, but what makes NDR stand out is how it presents data. Its intuitive dashboards, nodal diagrams, and automated correlation give analysts an immediate understanding of what’s happening.
For example:
- Threat timelines show how an attack unfolded step by step.
- Nodal diagrams map infected hosts, lateral movement, and external connections.
- Automated incident enrichment pulls in threat intelligence and asset context.
This simplification means even junior analysts can contribute effectively to investigations without relying solely on senior team members.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.

Why NDR Solutions is Essential for Modern Security Operations
Here’s the bottom line. Firewalls and endpoint security remain important, but they can’t see everything. Attackers exploit blind spots in cloud traffic, encrypted sessions, unmanaged devices, and east-west movements.
NDR solutions close these gaps by delivering:
- Real-time network threat monitoring.
- Deep, contextual insights instead of shallow alerts.
- Forensic capabilities for rapid incident response.
- Actionable intelligence that empowers teams.
In a world where adversaries operate stealthily and patiently, relying on fragmented visibility is risky.
Why NetWitness NDR Solutions Stands Out
Modern environments require continuous network security monitoring.
NDR cybersecurity strengthens security by delivering
- Continuous network threat detection
- Deep network traffic analysis
- Faster threat detection and response
- Improved SOC threat visibility
This makes NDR solutions essential for effective network security.
Moving From Alert Fatigue to Proactive Security
The days of reacting to endless alarms are over. With NetWitness NDR, you get:
- Fewer but more meaningful alerts.
- End-to-end visibility for confident decisions.
- Faster detection, investigation, and response cycles.
- Stronger defence against both known and unknown threats.
So if your team is drowning in noise, it’s time to move beyond alert fatigue and harness true network threat visibility with NDR solutions that deliver insights you can act on.
Final Thoughts
Security teams don’t need more alerts. They need clarity. NDR solutions combine network traffic analysis and visibility to improve threat detection and response across complex environments.
With better network security monitoring, teams can detect threats earlier and respond with confidence.
Frequently Asked Questions
1. What are NDR solutions in cybersecurity?
NDR solutions analyze network traffic using behavioral analytics and threat intelligence to detect and respond to cyber threats in real time, improving overall network security visibility.
2. How do NDR solutions provide actionable insights?
They correlate network data, enrich it with context, and present clear attack timelines and patterns, helping analysts quickly understand and act on threats.
3. Does NDR work in cloud and hybrid environments?
Yes, modern NDR cybersecurity platforms are designed to monitor on-prem, cloud, and hybrid infrastructures with consistent visibility.
4. What types of threats can NDR solutions detect?
NDR detects malware, insider threats, lateral movement, data exfiltration, and unknown or zero-day attacks through behavioral analysis.
5. How do NDR solutions help SOC analysts investigate incidents faster?
They provide full network visibility, session reconstruction, and automated context, reducing investigation time and improving response accuracy.
6. What industries benefit most from NDR solutions?
Industries with complex networks like finance, healthcare, manufacturing, and critical infrastructure benefit the most due to their need for continuous network security monitoring.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.