Key Takeaways
- Modern SOCs are replacing fragmented tools with unified cybersecurity platforms to eliminate visibility gaps.
- SIEM, NDR, and EDR integration improves detection accuracy and speeds up incident response.
- Unified security operations reduce alert fatigue by correlating alerts into meaningful threats.
- Automation built into modern SOC platforms helps teams respond faster and focus on high-impact risks.
- A single cybersecurity platform improves efficiency, reduces costs, and strengthens overall security posture.
Point Solutions Limit Unified Visibility in SOC Environments
Most SOC teams did not plan to manage dozens of security tools. It happened gradually. Each new threat introduced another tool. Endpoint protection, network monitoring, log analysis, and cloud security. Each solved a specific problem. But these tools do not work together by default.
Each generates alerts independently. Each shows only its own data. Analysts must manually switch between systems to understand what is happening. This lack of unified visibility in SOC workflows creates investigation delays. More importantly, they allow attackers to hide their moves and rely on possible blind spots (they do not create these blind spots themselves, but the lack of correlation between different platforms makes it difficult to trigger alerts).
Attackers rely on these blind spots. They move across endpoints, networks, and identities knowing most tools cannot connect activity across layers. A unified cybersecurity platform removes this fragmentation. It centralizes telemetry and gives SOC teams a complete operational view enabling correlation and increasing the confidence level of alerts.
Unified Cybersecurity Platforms Improve Threat Detection Accuracy
Threat detection improves when signals are connected. Point tools detect isolated activity. A unified threat detection platform detects attack patterns. For example, a login anomaly alone may not trigger a high-priority alert. But when combined with endpoint activity and unusual network communication, it becomes a clear indicator of compromise.
Unified cybersecurity platforms correlate:
- Endpoint behavior
- Network traffic
- Authentication events
- User activity
- System logs
This correlation improves detection precision and reduces missed threats. Instead of reacting to individual alerts, SOC teams respond to confirmed incidents.
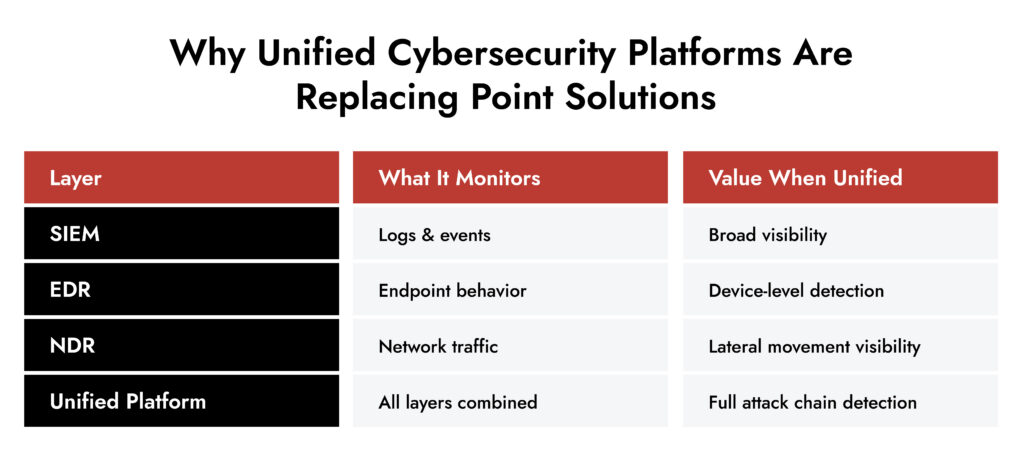
SIEM, NDR, EDR Integration Strengthens Security Analysis
SIEM, NDR, and EDR each serve different detection roles.
- SIEM analyzes logs and event data
- EDR monitors endpoint activity
- NDR analyzes network behavior
When deployed separately, each tool provides partial visibility. SIEM, NDR, EDR integration connects these layers.
This allows SOC teams to:
- Detect lateral movement across endpoints and networks
- Identify command-and-control communication
- Validate suspicious activity across multiple sources
- Investigate incidents faster
Integrated detection reduces uncertainty. Analysts no longer rely on assumptions. They rely on correlated evidence. This improves both speed and confidence in incident response.
Unified Security Operations Reduce Alert Fatigue
Alert fatigue is one of the biggest operational risks in SOC environments. Point solutions generate large volumes of alerts without context. Many alerts are duplicated, and many are low risk alerts.
Analysts waste time reviewing alerts that do not require action. Unified security operations solve this problem by grouping related alerts into single incidents. Instead of reviewing hundreds of isolated alerts, analysts see one correlated threat.
Unified platforms provide:
- Alert correlation
- Risk-based prioritization
- Incident grouping
- Investigation context
This reduces alert volume and improves analyst productivity. SOC teams focus on real threats instead of noise.
Modern SOC Platforms Use Automation to Improve Response Speed
Manual workflows slow down incident responses. Analysts must gather data from multiple tools, analyze evidence, and take action. This process takes time. During that time, attackers continue moving inside the environment.
Modern SOC platforms use automation to accelerate this process. Automation enables:
- Identifying patterns and connections between multiple alerts
- Incident enrichment with contextual data
- Automated investigation workflows
- Immediate response actions such as isolating endpoints
This reduces detection and response time significantly. Automation allows SOC teams to act faster without increasing workload.
Unified Cybersecurity Platforms Simplify Security Operations
Managing multiple cybersecurity solutions increases operational overhead. Each tool requires maintenance, integration, and training. This increases complexity and operational costs. A unified cybersecurity platform simplifies operations by consolidating capabilities.
SOC teams benefit from:
- Centralized monitoring
- Single interface for investigations
- Integrated detection and response
- Reduced tool management
This improves efficiency and reduces operational friction. Security teams spend more time on defense and less time managing tools.
Unified Cybersecurity Platform Improves Cybersecurity Awareness and Monitoring
Cybersecurity awareness depends on visibility. Fragmented tools limit awareness because each tool shows only part of the environment. A unified cybersecurity platform provides centralized monitoring across:
- Endpoints
- Networks
- Users
- Cloud environments
- Authentication systems
This improves cybersecurity awareness at the operational level. SOC teams can identify suspicious patterns earlier and respond faster. Better visibility leads to better security outcomes.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.
Modern SOC Platforms Provide Scalable Cybersecurity Solutions
Threat environments are constantly expanding. Organizations operate across cloud, hybrid, and on-premise systems. Point solutions struggle to scale across these environments. Modern SOC platforms are designed for scalability. They support:
- Multi-environment visibility
- High-volume telemetry processing
- Integrated detection across infrastructure
- Centralized security operations
This makes unified cybersecurity platforms suitable for enterprise environments. They provide long-term cybersecurity solutions instead of short-term fixes.
Unified Cybersecurity Platforms Strengthen Cybersecurity Services and SOC Efficiency
Unified platforms improve both detection capability and operational performance. SOC teams gain:
- Faster incident detection
- Faster response times
- Reduced alert volume
- Improved investigation workflows
- Better operational efficiency
Unified cybersecurity services enable SOC teams to operate more effectively with fewer tools. This improves overall security posture.
| Capability | Point Solutions | Unified Cybersecurity Platform |
| Investigation speed | Slow | Fast |
| Visibility | Fragmented | Unified |
| Alert correlation | Manual | Automated |
| Analyst workload | High | Reduced |
| Threat response | Delayed | Immediate |
NetWitness and Unified Cybersecurity Platforms
NetWitness enables unified cybersecurity by bringing network, endpoint, log, and cloud visibility into a single platform. This eliminates blind spots caused by disconnected tools and gives SOC teams complete operational visibility.
With built-in SIEM, network visibility, and endpoint monitoring, NetWitness helps analysts detect, investigate, and respond to threats faster. Automated alert correlation and centralized investigations reduce alert fatigue and improve response efficiency.
NetWitness allows organizations to replace fragmented cybersecurity solutions with a scalable unified cybersecurity platform built for modern SOC operations.
Conclusion: Unified Cybersecurity Platforms Are the Foundation of Modern SOC Platforms
Point solutions cannot provide the visibility, speed, or integration required in modern environments. They create operational gaps and slow down threat detection. Unified cybersecurity platforms solve these problems by integrating detection, visibility, and response into a single system.
They enable unified security operations, improve threat detection accuracy, reduce alert fatigue, and simplify SOC workflows. Modern SOC platforms are built on unified cybersecurity architecture. Organizations that adopt unified cybersecurity platforms gain stronger protection, better visibility, and more efficient security operations.
Frequently Asked Questions
1. Why are modern SOCs moving away from point solutions?
Point solutions operate independently and create visibility gaps. Modern SOCs require unified cybersecurity platforms that integrate data across systems to detect threats more effectively.
2. How does a unified cybersecurity platform improve threat detection?
Unified platforms correlate signals from endpoints, networks, and logs. This provides full attack context and improves detection accuracy.
3. How do unified platforms reduce alert fatigue?
Unified platforms group related alerts into incidents and prioritize threats. This reduces alert volume and improves analyst efficiency.
4. What role does automation play in unified security platforms?
Automation accelerates detection and response by correlating alerts, enriching incidents, and triggering response actions automatically.
5. What should enterprises look for in a unified cybersecurity platform?
Enterprises should look for unified visibility, SIEM NDR EDR integration, automation, scalability, and centralized security operations capabilities.
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.