How Can Enterprises Implement Network Segregation in an Office Network?
Enterprises can strengthen network segregation by embedding it into governance and operations, not just infrastructure.
Focus on these five actions:
- Establish a clear segmentation policy framework for the enterprise network.
- Automate network segmentation controls to adapt to changing users and devices.
- Integrate identity-based access to improve office network security.
- Regularly test segmentation to expose hidden network security threats.
- Track risk metrics to continuously refine network security best practices.
This turns enterprise network segmentation into a living, measurable security strategy rather than a one-time configuration task.
Introduction
Enterprise office networks are no longer controlled environments. They are sprawling, hybrid ecosystems made up of employees, contractors, cloud workloads, IoT devices, guest Wi-Fi, and third-party access. That complexity is exactly why attackers thrive.
Here’s the uncomfortable truth. Most breaches don’t fail because perimeter defenses are weak. They succeed because once attackers get inside, they can move freely.
Network segregation is how enterprises stop that movement.
When implemented correctly, network segregation transforms a flat, vulnerable office network into a controlled environment where access is intentional, visibility is continuous, and damage is contained.
What Is Network Segregation in an Enterprise Context?
At its core, network segregation is the practice of dividing an enterprise network into smaller, isolated segments and strictly controlling how traffic flows between them. Each segment serves a specific purpose and has clearly defined access rules.
Think of it like designing a secure office building. Finance doesn’t sit next to the lobby. The data center doesn’t share doors with guest access. Sensitive systems are separated not for convenience, but for survival.
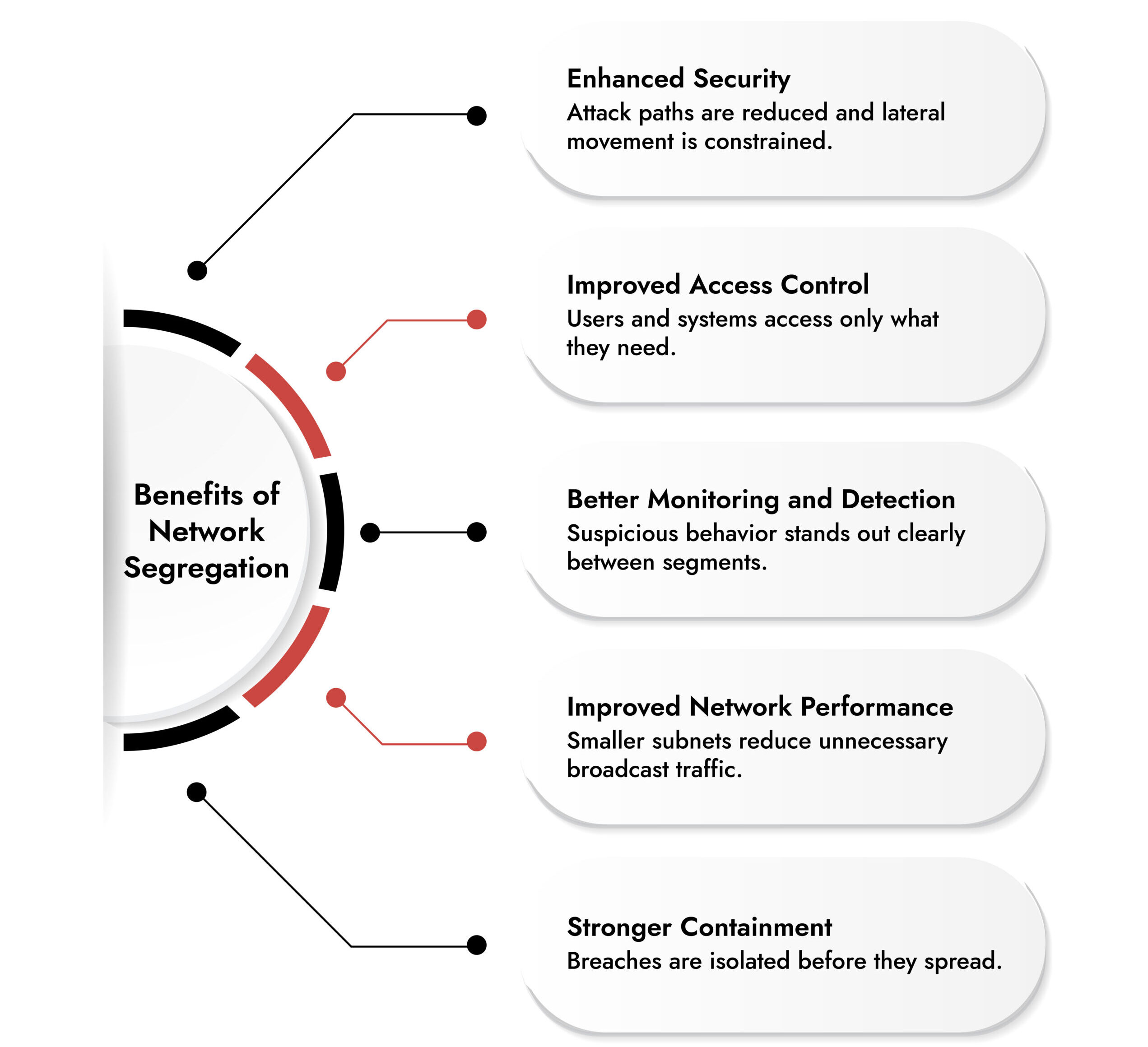
In an enterprise network, segregation ensures that:
- Users only access what they are authorized to
- Critical systems are isolated from everyday office traffic
- A compromised device cannot freely reach high-value assets
This is not theoretical security. This is how real-world attacks are contained.
Why Network Segregation Matters More Than Ever
High-profile breaches over the last decade have made one thing clear. Once attackers breach a single endpoint, their next move is lateral movement. They map the network. They probe for weak systems. They use legitimate admin tools. They pivot quietly. Flat networks make this easy. Segregated networks make it expensive, noisy, and slow.
Strong office network security depends on forcing attackers to cross monitored, controlled boundaries. Every boundary is a chance to detect, block, or contain malicious activity before it reaches the core of the business. This is why network segregation is now considered a foundational network security best practice, not an advanced one.
Network Segregation vs Network Segmentation
These terms are often used interchangeably, but at the enterprise level, the distinction matters.
Network segmentation refers to the technical act of dividing a network using VLANs, subnets, or logical boundaries.
Network segregation is the security-driven strategy applied on top of segmentation. It combines segmentation with access control, policy enforcement, and network security monitoring.
Segmentation creates structure.
Segregation creates protection.
Enterprises that stop at basic segmentation leave gaps attackers know how to exploit.
How Network Segregation Stops Modern Attacks
Once an endpoint is compromised, attackers typically attempt to:
- Establish remote connections to servers
- Map internal resources
- Abuse legitimate administrative tools
- Access shared file systems
A segregated network disrupts these steps. If a user workstation cannot communicate directly with a financial server, the attack stalls. If management networks are isolated, credential abuse becomes far harder. If east-west traffic is monitored, malicious behavior stands out quickly.
This is how segregation turns breaches into incidents instead of catastrophes.
“I often tell customers/prospects: Segregation without monitoring is just ‘blind security.’ You can build the thickest walls in the world, but if you aren’t watching the corridors between them, you won’t know when someone has climbed over. The goal isn’t just to stop movement, it’s to make that movement so noisy and expensive that the attacker is caught long before they reach your crown jewels.”
— Clemens Muller, Sales Engineer, NetWitness
Core Principles for Enterprise Network Segregation
Before implementation, enterprises need to align on a few non-negotiables.
- Assume Breach – Design the network as if compromise is inevitable. This mindset aligns closely with zero networks and zero trust approaches.
- Enforce Least Privilege Everywhere –If a system or user does not need access, it should not have it. Period.
- Visibility Is Mandatory –Segregation without monitoring is blind security. Continuous network security monitoring across segments is essential.
- Policy Over Convenience –Access rules should be driven by business need, not ease of implementation.
Step-by-Step: Implementing Network Segregation in an Office Network
Step 1: Understand Your Network First
You cannot secure what you do not understand.
Start by mapping:
- Users and roles
- Endpoints and device types
- Applications and servers
- Data sensitivity
- Actual traffic flows
This process often reveals unnecessary connections that have existed for years without justification.
Step 2: Classify Assets by Business Criticality
Not all assets are equal.
Group systems based on:
- Sensitivity of the data
- Business impact if compromised
- Regulatory requirements
- Exposure level
Typical classifications include:
- User workstations
- Core business applications
- Finance and HR systems
- Management infrastructure
- Guest and third-party access
This classification is the backbone of enterprise network segmentation.
Step 3: Design Logical Security Zones
Using your classifications, define clear network zones.
Common zones include:
- User access zone
- Server and data zone
- Management zone
- Guest and BYOD zone
- Third-party access zone
Each zone should have explicitly defined communication rules. No implicit trust. No default access. This is where segmenting the network becomes meaningful.
Step 4: Enforce Controls Across Multiple Layers
Effective network segregation does not rely on a single layer.
Enterprises should apply controls across:
- Network layer (firewalls, ACLs)
- Host layer (endpoint controls)
- Application layer (authentication and authorization)
In highly sensitive environments, physical isolation may still be appropriate. The key is layered enforcement with centralized visibility.
Step 5: Apply Least Privilege Communication Rules
If a system needs to communicate on one protocol, allow only that protocol. Nothing else. This approach dramatically reduces attack surface and aligns segregation with broader identity and access management strategies. Least privilege is not just for users. It applies to networks, services, and machines.
Step 6: Monitor Inter-Segment Traffic Continuously
Segregation without monitoring is a false sense of security.
Strong network security monitoring enables teams to:
- Detect unusual lateral movement
- Identify policy violations
- Spot compromised hosts early
- Validate segmentation effectiveness
East-west traffic visibility is especially critical in enterprise environments.
Step 7: Align Segregation with Zero Trust
Modern enterprises are increasingly adopting zero trust models. Zero networks depend on segmentation and segregation to function effectively.
Segregation supports zero trust by:
- Eliminating implicit trust
- Enforcing identity-aware access
- Limiting blast radius
- Making malicious behavior visible
These approaches are complementary, not competing.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.
Network Segregation Best Practices for Enterprises
To build segregation that actually holds up, follow these network segregation best practices:
- Segment based on business function, not just technology
- Separate management and administrative networks
- Isolate high-risk devices like IoT and printers
- Whitelist legitimate traffic instead of blacklisting bad traffic
- Centralize monitoring and policy enforcement
- Test segmentation regularly using attack simulations
The more segmented the network, the harder it is for attackers to move. The tradeoff is operational complexity, which must be managed deliberately.
Key Takeaways for Enterprise Leaders
The more segregated your network is:
- The harder it becomes for attackers to reach sensitive systems
- The more planning and governance it requires
- The more resilient your organization becomes to modern threats
Segregation is not about perfection. It is about making attacks expensive, slow, and visible.
Conclusion
Enterprise office networks are no longer protected by simple perimeters. They are dynamic, interconnected, and constantly exposed. Network segregation provides the structure enterprises need to control that complexity. By combining thoughtful network segmentation, strict access control, continuous network security monitoring, and alignment with zero trust principles, organizations can dramatically reduce risk without sacrificing functionality. This is how modern enterprises build networks that can withstand real-world attacks.
Frequently Asked Questions
1. What is network segregation?
Network segregation is the practice of isolating network segments to control access, reduce lateral movement, and protect sensitive systems.
2. What are the best network segregation solutions for small businesses?
Small businesses often start with VLAN-based segmentation, internal firewalls, and basic monitoring, focusing on simplicity and visibility.
3. What is the difference between network segregation and segmentation?
Segmentation divides the network structurally. Segregation enforces security policies and monitoring across those segments.
4. How to segregate a network?
Map assets, classify risk, design zones, enforce least privilege access, and monitor traffic between segments.
5. How to segregate networks to best manage a security network?
Use business-driven segmentation, strict authorization, traffic whitelisting, and continuous monitoring.
6. Why is network segregation important for enterprises?
It limits breach impact, reduces lateral movement, improves visibility, and supports modern zero trust security models.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.