Key Takeaways
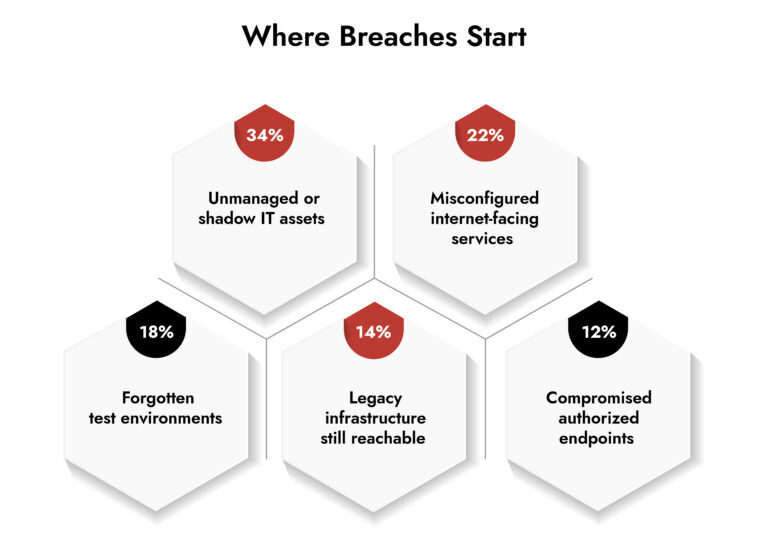
- Enterprises cannot secure assets they cannot see. Most breaches still begin with unmanaged or forgotten devices.
- A mature network inventory management process directly reduces attack surfaces and accelerates incident response.
- Zero trust depends on accurate asset identity, not assumptions about the network.
- Continuous discovery, classification, and monitoring outperform periodic audits.
- Security operations platforms become significantly more effective when enriched with real asset context.
Introduction
Security teams rarely care about known servers. They lie awake at night worrying about the unknown ones.
A vulnerable dev VM, an ancient VPN box, an abandoned cloud machine, a contractor laptop left on the network. These assets rarely appear in charts until attackers discover them for the first time. This lag explains why network inventory management is now at the forefront of enterprise security rather than being a part of IT documentation.
Every modern breach analysis leads to the same conclusion: the attacker didn’t break into a fortress; they entered through an unguarded side door.
Organizations devote considerable resources to detection, analysis, and response activities. But these capabilities are predicated on one simple tenet: accurate asset knowledge. Without it, alerts become meaningless, risk assessments become speculative, and response teams waste interminable hours wondering what exactly they are trying to protect.
Network Inventory Management Defines the Real Attack Surface
Security visibility starts with asset awareness. Attack surface visibility depends on knowing every device, identity, workload, and service communicating on the network. Anything missing becomes an unmonitored entry point.
A strong network inventory management program answers three critical questions at all times:
- What exists?
- Who owns it?
- Why is it communicating?
According to CISA’s 2024 Known Exploited Vulnerabilities guidance, more than 60% of exploited vulnerabilities affect systems that organizations did not realize were internet exposed. NIST SP 800-53 Rev.5 also elevates asset identification as a foundational control for risk management.
This changes how we define security maturity. Mature environments don’t just detect attacks faster. They reduce uncertainty before detection ever matters.
Why Traditional Asset Lists Fail Enterprise Security
Spreadsheets and CMDB snapshots provide historical truth. Security requires real-time truth. Legacy inventory processes operate on change of tickets and human reporting. Modern environments operate on APIs, automation, containers, and ephemeral workloads. A server can exist for 20 minutes and still leak credentials.
A modern network inventory management approach must be:
- Continuous, not scheduled
- Behavior-aware, not hostname-based
- Integrated with detection systems
- Automatically classified
Organizations relying on manual reconciliation struggle with three operational problems:
- Alerts lack business context
- Vulnerability prioritization becomes inaccurate
- Incident response slows dramatically
Gartner’s 2025 security operations research highlights that organizations with automated asset intelligence reduce mean time to respond by over 35%. That improvement comes from clarity, not speed.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
Network Inventory Management Enables Zero Trust Networking
Zero trust requires identity-based decisions. Identity requires reliable asset attribution. Without inventory accuracy, zero trust becomes policy theater.
A functioning network inventory management capability provides the data zero trust actually consumes:
- Device identity
- Behavioral baseline
- Ownership and criticality
- Communication intent
This directly supports zero trust networking controls such as:
- Conditional access decisions
- Microsegmentation
- Anomaly detection
- Risk-based authentication
Security teams often deploy zero trust networking policies first and discover later they lack reliable asset classification. The result: excessive blocking or excessive exceptions. Inventory maturity prevents both.
Network Inventory Tools Transform Detection Quality
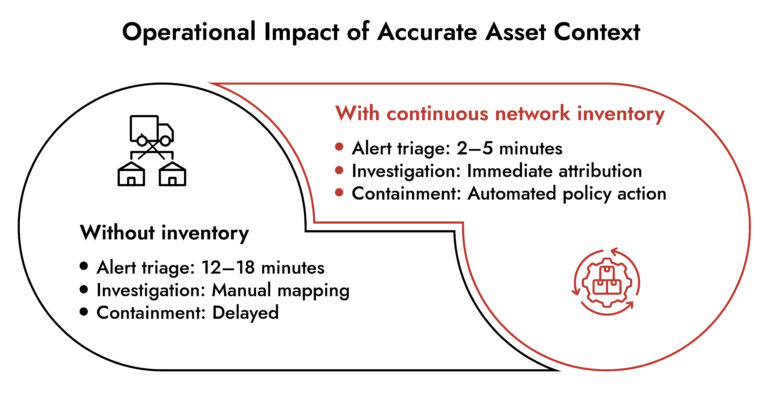
Detection platforms generate alerts. Context determines whether alerts matter. Modern network inventory tools enrich telemetry with asset intelligence. Instead of “suspicious SMB traffic,” analysts see: The finance database server communicates with an unmanaged device in the contractor VLAN. That single improvement changes the triage time from minutes to seconds.
Effective network inventory security integration improves:
- Threat prioritization
- Investigation speed
- False positive reduction
- Automated response accuracy
Security operations platforms rely heavily on enriched metadata. Enterprise cybersecurity programs without this enrichment spend time validating alerts rather than resolving them.
Enterprise Security Management Depends on Continuous Discovery
The network no longer has edges. It has relationships. Cloud, SaaS, remote users, APIs, and partner integrations mean the concept of “inside vs outside” no longer applies. Enterprise security management now focuses on communication behavior rather than location.
Continuous network inventory management enables:
- Identification of unmanaged endpoints
- Tracking of ephemeral cloud assets
- Detection of unauthorized services
- Monitoring of lateral movement paths
This becomes particularly critical during incident responses. Attackers rarely compromise their intended target first. They pivot through overlooked infrastructure. The organizations that detect lateral movement fastest already know the normal communication map.
How Network Inventory Management Improves Incident Response
Incident response speed depends on knowing what you are isolating. When responders encounter an unknown device during an investigation, they pause containment to identify it. That pause often allows attackers to persist.
A mature network inventory program reduces response friction:
- Ownership lookup becomes immediate
- Criticality classification exists
- Dependencies are known
- Safe containment becomes possible
This matters operationally. Containing the wrong server can halt production. Not containing the right one can extend a breach. Security leadership increasingly measures readiness by how quickly teams answer: “Can we isolate this device safely right now?”
Role in Enterprise Cybersecurity Strategy
Enterprise cybersecurity strategies increasingly align around three pillars:
- Visibility
- Detection
- Response
Network inventory management strengthens all three simultaneously.
- Visibility: defines the environment
- Detection: provides context
- Response: enables precision
Organizations often invest in network security solutions, expecting improved protection, but overlook that analytics accuracy scales with asset awareness. Better tools amplify bad assumptions. Better data amplifies good tools.
Where NetWitness Fits
Security analytics platforms become most effective when they understand the environment they monitor. Platforms like NetWitness analyze full network activity and enrich it with asset context, allowing teams to investigate behavior rather than raw events.
When continuous asset awareness feeds telemetry analysis, investigations shift from log searching to attack reconstruction. Analysts no longer ask what happened; they confirm how and why.
This alignment between network visibility and contextual detection enables more reliable threat detection, especially for lateral movement and insider threats. The takeaway is simple: analytics without asset intelligence produce noise. Analytics with asset intelligence produces understanding.
Building a Practical Network Inventory Management Process
Start with discovery before classification. Then automate enrichment and monitoring.
A working network inventory management framework follows five stages:
- Continuous discovery across network and cloud
- Automatic fingerprinting and role classification
- Ownership mapping
- Behavioral baseline monitoring
- Integration with detection and response
Security teams that skip ownership mapping struggle during incidents. Security teams that skip behavior monitoring struggle with false positives. Both stem from incomplete inventory thinking.
Conclusion
Security failures rarely originate from advanced malware. They originate from unknown infrastructure. Network inventory management shifts security from reactive investigation to controlled defense. It defines the environment, reduces uncertainty, and enables precise response.
Organizations don’t need more alerts. They need fewer unknowns. Strengthening asset awareness often improves security outcomes faster than deploying another standalone control. When every device has an identity and context, detection tools finally operate with clarity.
If security programs aim to reduce attacker opportunity rather than only detect attacker behavior, inventory maturity becomes the logical starting point.
Frequently Asked Questions
1. What is network inventory management?
Network inventory management involves the ongoing process of locating, recognizing, categorizing, and overseeing all devices, workloads, and services interacting within an environment to enhance network security and operational oversight.
2. Why is network inventory management critical for enterprise security?
It reduces attack surface visibility gaps, improves incident response speed, and enables zero trust networking decisions based on verified asset identity rather than assumptions.
3. What is the first step of inventory management networking?
Continuous automated discovery across on-premises and cloud environments. Without accurate discovery, classification and protection fail.
4. How to create a network inventory management plan?
Start with automated discovery, map ownership, classify criticality, monitor behavior, and integrate inventory with enterprise security management and detection platforms.
5. What security risks come from poor network inventory management?
Unmonitored assets, delayed breach detection, incorrect containment actions, and inaccurate vulnerability prioritization.
6. How do network inventory tools support network security solutions?
They enrich alerts with asset context, improve prioritization accuracy, and enable faster investigation within enterprise cybersecurity operations.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.