Why are organizations shifting to unified threat detection and response?
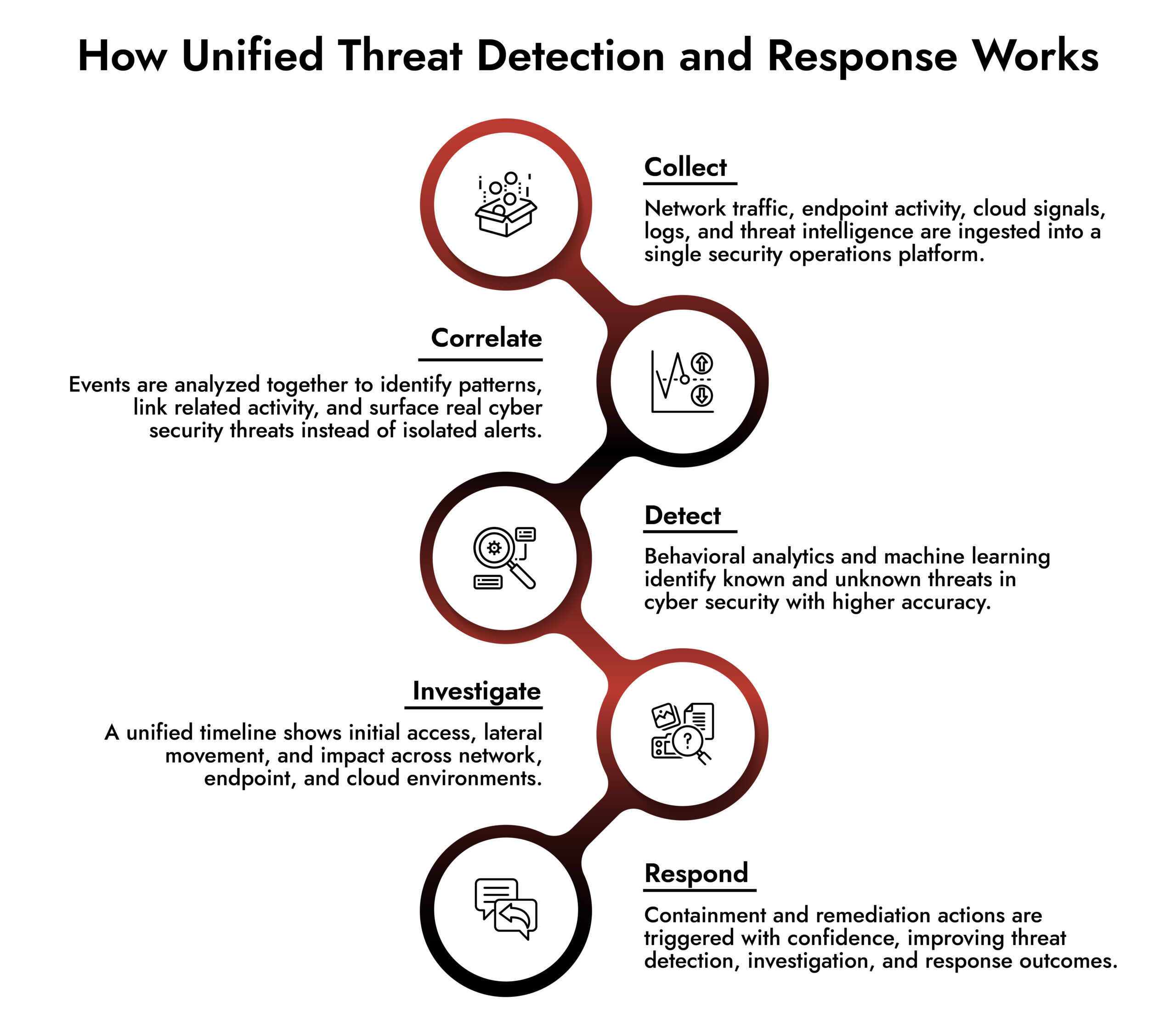
Organizations move to unified threat detection and response because modern cyber security threats span network, endpoint, cloud, and identity environments, while traditional threat detection solutions operate in silos. A unified approach brings threat detection, investigation, and response into one security operations platform, improving cyber threat monitoring, reducing investigation time, and enabling faster, more accurate response to advanced and AI-driven threats in cyber security.
Introduction
Here’s the thing most SOC leaders already know but rarely say out loud. Your biggest security problem is not a lack of tools. It’s too many of them. SIEM for logs. NDR for packets. EDR for endpoints. SOAR for response. Cloud-native tools for everything else. Each does one thing reasonably well. None of them work together the way your analysts actually investigate threats.
The result is predictable. Slower investigations. Missed context. Alert fatigue. And a growing gap between how attacks happen and how your security operations platform responds.
That gap is exactly why organizations are moving away from disconnected threat detection solutions and toward unified threat detection and response. And when teams migrate to NetWitness Unified TDR, the impact shows up fast. This guide breaks down what changes immediately and why those changes matter at a bottom-line, operational level.
The Real Cost of Disconnected Threat Detection and Response
Most security teams don’t experience breaches because they failed to buy the right product. They experience breaches because no single system sees the whole attack. Disconnected tools create four structural problems:
Fragmented visibility
Network traffic lives in one console. Endpoint telemetry in another. Cloud signals somewhere else. Threat detection investigation and response turns into manual stitching.
Delayed detection
AI cybersecurity threats rarely trip one rule. They move laterally, blend into normal traffic, and exploit gaps between tools.
Shallow investigations
Analysts chase alerts instead of understanding attacker behavior. Timelines are partial. Context is missing.
Inconsistent response
By the time teams agree on what happened, the attacker has already moved on.
These are not tooling issues. They are architecture issues.
Why Unified Threat Detection and Response Changes the Equation
Unified threat detection and response is not about consolidation for its own sake. It’s about changing how cyber threat monitoring actually works.
Instead of asking analysts to pivot between tools, unified TDR brings detection, investigation, and response into one continuous workflow.
What this really means is:
- One data model instead of siloed telemetry
- One investigation timeline instead of fragmented alerts
- One response path instead of handoffs between teams
NetWitness Unified TDR is built specifically for this model, especially in large, complex enterprise environments where threats in cybersecurity don’t respect tool boundaries.
What Teams Gain Immediately After Migrating to NetWitness Unified TDR
1. Full-Spectrum Visibility Without Tool Hopping
NetWitness collects and analyzes telemetry from network traffic, endpoints, cloud workloads, and threat intelligence sources in a single platform. Not stitched together after the fact. Not normalized weeks later. Unified at ingestion.
This gives teams immediate visibility into:
- East-west and north-south traffic
- Endpoint behavior tied to network sessions
- Cloud activity mapped to on-prem events
- Threat intelligence contextualized against real activity
For teams dealing with modern cyber security threats and solutions, this eliminates blind spots that attackers actively exploit.
2. High-Fidelity Detection That Cuts Through Noise
Most threat detection solutions drown analysts in alerts because they rely on isolated indicators. NetWitness uses behavioral analytics and machine learning to correlate activity across data sources. That correlation is the difference between noise and signal. Instead of asking “Did this trigger a rule?” the platform asks “Does this behavior match an attack pattern?”
The immediate impact:
- Fewer false positives
- Earlier detection of stealthy techniques
- Better coverage against AI-driven and evasive threats
This is critical as threats in cyber security increasingly rely on living-off-the-land tactics that evade single-layer detection.
Autonomous AI Defenders for a Smarter SOC
3. Investigation Timelines That Actually Tell the Story
This is where most SOC workflows break down.
In disconnected environments, investigations look like this:
Alert → Pivot → Export → Pivot again → Guess.
NetWitness Unified TDR automatically reconstructs full attack timelines. Analysts see:
- Initial access
- Lateral movement
- Privilege escalation
- Command-and-control
- Data exfiltration
All in one view. Across network, endpoint, and cloud. That unified system impact analysis removes guesswork and dramatically improves investigation quality.
4. Faster, More Confident Response Actions
Response quality improves when teams trust what they see. Because NetWitness ties detections directly to validated attack behavior, response actions are based on evidence, not assumptions.
With built-in orchestration and response automation, teams can:
- Contain compromised endpoints
- Block malicious traffic
- Enrich incidents automatically
- Maintain complete audit trails
This matters in regulated environments where cyber threat monitoring must support both security and compliance outcomes.
5. A Security Operations Platform That Scales With Reality
Many SOC tools work well at small scale and collapse under enterprise complexity. NetWitness is designed for large, distributed environments where data volumes are high and architectures are hybrid by default.
Immediate operational benefits include:
- Rapid scale without re-architecting pipelines
- Lightweight agent processing
- Unified data platform for correlation and analytics
- Centralized management without centralized bottlenecks
This allows teams to mature their threat detection investigation and response without constantly adding new tools.
Why Unified Threat Detection and Response Matters Now
Cybersecurity threat detection is no longer about catching malware. It’s about understanding behavior across environments that attackers intentionally fragment.
AI cybersecurity threats, cloud-native attacks, and identity-based techniques all exploit tool gaps. Unified TDR closes those gaps by design. What teams gain immediately is not just speed. It’s clarity. And clarity is what allows security operations to move from reactive firefighting to controlled, confident response.
Frequently Asked Questions
1. Why should organizations move to a unified TDR platform?
Because disconnected tools cannot reliably detect or respond to modern attacks that span network, endpoint, and cloud environments. Unified TDR provides end-to-end visibility and context in a single workflow.
2. What immediate benefits do teams see after migrating to NetWitness Unified TDR?
Teams see faster detection, fewer false positives, complete investigation timelines, and more consistent response actions almost immediately after deployment.
3. How does Unified TDR improve response quality?
By correlating behavior across data sources, Unified TDR ensures response actions are based on validated attack activity rather than isolated alerts.
4. How does unified TDR improve investigation workflows?
It eliminates manual pivoting between tools and automatically reconstructs attack timelines, allowing analysts to focus on understanding and stopping threats.
5. How quickly can SOC teams realize value after migration?
Most teams experience measurable improvements in detection accuracy, investigation speed, and analyst efficiency within weeks, not months.