What is the most important cloud security tip for SOC teams?
The most important cloud security tip for SOC teams is to enable continuous visibility across the infrastructure, whether cloud or on-prem. Without visibility, SOC cannot detect suspicious activity, understand attacker behavior, or respond effectively to incidents. Continuous visibility enables the team to identify misconfigurations, changes in cloud workloads, and detect unusual patterns before they escalate into breaches.
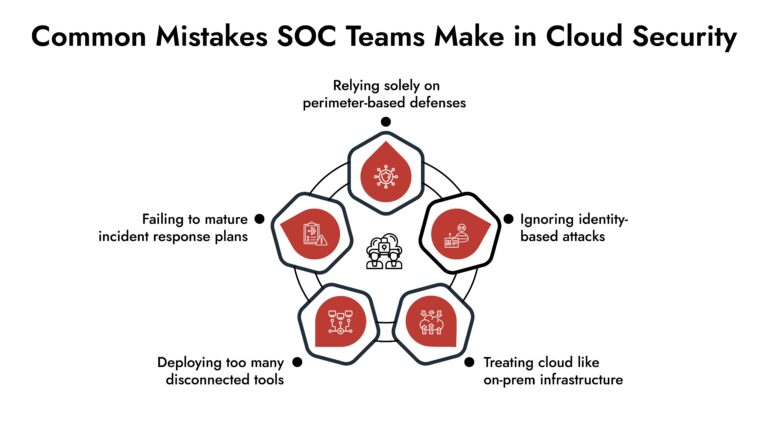
Cloud adoption is moving rapidly, and SOC teams are feeling it. They are dealing with new workloads that spin up in seconds, developers that push infrastructure changes through code, multi-cloud architecture that stretch visibility across regions and providers that each play by their own rules.
The problem is that many security operations centers are still running monitoring strategies built for a different era. Those strategies weren’t designed for environments that are dynamic, API-driven, and identity-centric by default. The cloud networking and security requirements are different from on-premise systems.
80% of organizations reported at least one cloud breach in the last 12 months (Source: Sprinto Cloud Security Statistics 2025)
Enterprises today should apply cloud security tips or else risk exposure and fatal cyberattacks. In fact, misconfigurations, identity abuse, and poor visibility across the cloud security network are handing attackers easy wins every single day. Here are 10 practical tips SOC teams can use to get ahead of the problem.
Why Are Cloud Security Tips Important For SOC Teams?
Before we discuss cloud security tips, it is also important to understand the unique challenges of cloud cybersecurity. Because if it is the same, why does it need attention?
- Ephemeral Workloads: Containers, serverless functions, and instances spin up and vanish in minutes — sometimes before your monitoring tools even register they existed. This creates visibility gaps in cloud network monitoring and forensic investigations.
- Shared Responsibility Models: Your cloud provider locks down the physical infrastructure, but configurations, identities, and data — that’s on you. A misconfigured storage bucket isn’t AWS’s problem.
- Lateral Movement: Attackers who get inside start moving across the internal network in ways that traditional perimeter tools cannot detect without cloud networking security controls.
- Multi-cloud Complexity: Different logging formats and IAM structures complicate centralized cloud SIEM monitoring.
Approximately 56% of organizations struggle to secure data across multi-cloud environments. (Source: Exabeam Cloud Security Statistics 2025)
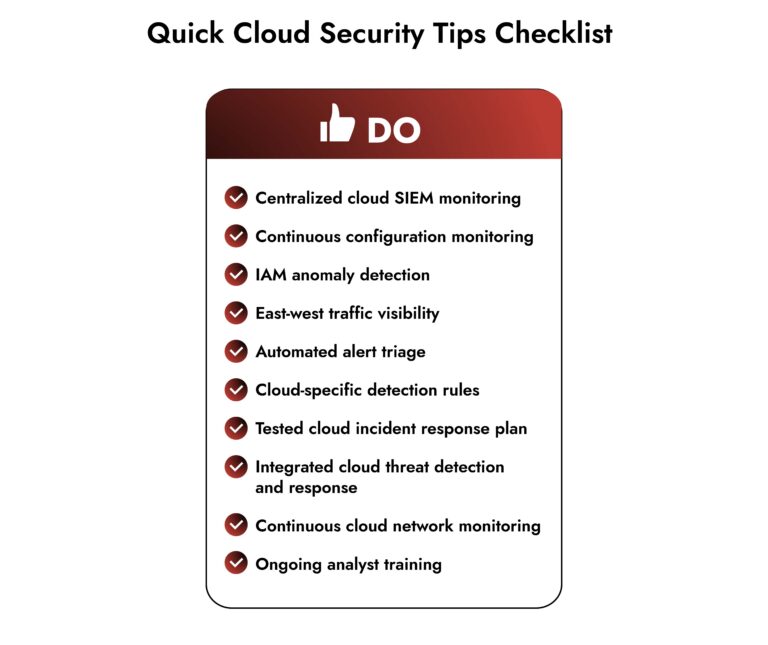
What Are the Most Effective Cloud Security Tips For 2026?
Cloud security is not a one-time activity; it needs ongoing visibility, mature cloud threat detection and response, and structured cloud incident management processes.
1. Continuous Visibility Across All Cloud Layers
Most cloud security threats don’t start with malware on an endpoint. They originate in management APIs or identity misuse, and in places that traditional monitoring tools were never designed to watch.
That means your monitoring needs to cover the control plane, workloads, identities, storage, and networking layers simultaneously. Missing even one of those creates a blind spot that attackers will find before you do.
Strategic Priority: Enable native logging (audit logs, activity logs) across your cloud environment and pipe everything into a centralized SIEM.
2. Monitor Cloud Configurations
Configuration drift is one of the quietest, most damaging things that can happen in a cloud security network posture. A storage bucket that becomes publicly accessible during a routine deployment update can sit exposed for weeks if no one is actively watching for it.
Automated, continuous configuration monitoring is one of the most impactful things a SOC team can do.
Strategic Priority: Track open security groups, risky permissions, and exposed storage as a part of continuous cloud network monitoring. Additionally, the alerts should be constantly reviewed
3. Enable Cross-Environment Log Correlation
When cloud logs are centralized alongside endpoint alerts in cloud SIEM monitoring, detection becomes stronger, and investigations move faster. Unified monitoring enables meaningful correlation across environments, helping SOC teams respond with greater speed and confidence.
Strategic Priority: Normalize and correlate logs centrally to strengthen cloud threat detection and response workflows.
4. Focus on Identity and Access Monitoring
Identity abuse is one of the most dangerous cloud security threats. For instance, an attacker can just log in with a compromised developer credential and quietly escalate their privileges through a misconfigured IAM role.
Strategic Priority: Continuously monitor privilege escalation attempts and anomalous login patterns to strengthen both cloud incident management and proactive cloud threat detection and response.
5. Detect East-West Traffic Inside the Cloud
Once an attacker is inside your environment, they start moving. For example, a compromised container scans adjacent subnets for open databases. It is something that perimeter-based tools completely miss because the traffic looks like normal internal communication.
Strategic Priority: Virtual network flow logs and behavioral analytics are your best tools here. You need internal telemetry to catch lateral movement before a minor compromise becomes a major incident.
6. Automate Alert Triage Where You Can
Cloud environments generate enormous volumes of telemetry. If you rely on manual triage, you will be dealing with analyst fatigue that translates into missed detections.
Using automation to enrich alerts with context helps prioritize what actually needs SOC attention. Repeated failed login attempts from a known scanning IP, for example, should be automatically categorized and deprioritized, so your analysts can focus on the signals that matter.
Strategic Priority: Implement risk-based alert prioritization.
7. Build Detection Rules Around Cloud-Native Threats
Cloud attacks look different than on-prem attacks. Detection rules built around legacy signatures and endpoint behaviors fail to address cloud-native attack techniques.
Strategic Priority: Update your detection content to reflect cloud-specific attack patterns: suspicious API calls, privilege escalation via role assumption, unauthorized snapshot creation, and unusual cross-region activity.
8. Test Your Security Controls Regularly
Assumed visibility is not actual visibility. Testing is the only honest way to know whether your monitoring is operational or just theoretical.
Strategic Priority: Regular simulation exercises and red team engagements surface gaps that would otherwise stay hidden until an actual attacker finds them. If simulated credential misuse fails to trigger your alerts, you want to find that out in a drill — not during a real incident.
9. Build a Cloud-Specific Incident Response Plan
The playbook that worked for an on-prem incident won’t translate directly to a cloud environment — and trying to improvise in the middle of a breach is a bad strategy.
Strategic Priority: Develop a dedicated cloud incident response plan with defined containment procedures. Automated playbooks that isolate compromised instances, snapshot volumes, and revoke credentials are worth their weight. They compress response time and reduce the surface area of damage while the team gets organized.
10. Keep Your SOC Team Educated on Cloud Environments
The skills gap in cloud cybersecurity is real, and it has real consequences. Analysts who aren’t familiar with cloud networking and service architecture will misread benign automation as malicious activity — or worse, miss actual threats because they don’t know what they’re looking at.
Strategic Priority: Continuous education on cloud architectures, services, and threat models strengthens cloud network security, detection engineering, and overall resilience.
Final Thoughts
Security is an ongoing process, especially in cloud environments. The attack surface shifts, new services get adopted, teams change — and the threat landscape keeps pace with all of it, whether you’re ready or not.
Cloud security, just like anything else, needs to start with small steps. The SOC team fixes the logging gaps in one quarter, tightens IAM policies in the second, and so on. Consistency is what separates teams that catch incidents early from teams that find out about them from their customers.
Frequently Asked Questions
1. What are the biggest cloud security challenges SOC teams face?
Cloud environments are dynamic and identity-driven, which creates new challenges for SOC teams, such as:
- Limited visibility across multi-cloud environments
- They generate massive telemetry, leading to alert fatigue
- They are an easy target for IAM misuse and privilege escalation
- They have east-west traffic blind spots
- Adapting legacy detection rules to cloud-native attack patterns
2. How can SOC teams improve cloud threat detection?
SOC teams can improve detection by centralizing cloud logs into existing SOC workflows, aligning detection rules with cloud-native attack techniques, continuously monitoring IAM activity, and regularly validating security controls to ensure alerts function as expected.
3. How can automation help SOC teams secure the cloud?
Automation helps by enriching alerts with context, prioritizing high-risk events, reducing repetitive noise, and accelerating response actions such as isolating workloads or revoking compromised credentials. It enables scalable cloud threat detection without overwhelming analysts.
Autonomous AI Defenders for a Smarter SOC