Key Takeaways
- OT cybersecurity is core to an organization’s safety, reliability, & corporate governance functions, not just a security initiative.
- OT visibility-first cybersecurity is the most effective method in industrial automation environments and is based on passive monitoring and protocol awareness.
- Most of the value created by the OT security program comes from long-term understanding of behavioral trends versus the notification of alerts.
- Well-designed OT cybersecurity solutions do not disrupt but enhance operations.
- A unified OT visibility platform with the investigation workflow across the enterprise provides greater flexibility and scalability across multiple plants and regions.
Why OT Cybersecurity Decisions Matter in 2026
The way we engineer industrial automation is changing faster than our products, like Programmable Logic Controllers (PLCs), that help us engineer these things. Remote engineering access to the plant floor is what the plants today rely on. The industry is also looking to have centralized monitoring, cloud-based analytics, and tighter integration with their enterprise information technology systems. So, while these changes help to promote efficient production operations, they are also changing the way we see and create security risks.
Cybersecurity for operational technology is now critical to these changes, and in 2026, securing operational technology should no longer focus on securing isolated control networks but rather on how industrial control systems work with each other and their users and their suppliers and how they are connected to enterprise infrastructure to allow for continuous operation in a safe manner.
National cybersecurity advisories from agencies such as CISA and NIST emphasize that operational technology systems often operate with legacy protocols, increasing connectivity, and limited visibility, creating unintended access paths for adversaries. Reports also show that many OT incidents originate after an IT compromise and that defenders struggle with delayed detection due in part to visibility gaps in industrial environments. These insights highlight why OT cybersecurity solutions must address access control, continuous visibility, and faster threat detection in industrial automation settings.
How OT Cybersecurity has Evolved in Industrial Automation
Operational technology was designed for reliability and longevity, not constant change. Many PLCs, RTUs (Remote Terminal Unit), and industrial protocols in use today predate modern security controls. What has evolved is the environment around them.
Between 2024 and 2025, multiple government advisories highlighted a consistent trend: initial access often occurs outside the OT network, followed by movement into industrial systems through trusted connections.
Common entry points include:
- Remote access infrastructure shared with IT
- Engineering workstations used across environments
- Temporary vendor connections that persist longer than intended
This does not mean industrial systems are inherently unsafe. It means operational technology security must account for how industrial networks are actually used, not how they were originally designed.
OT Cybersecurity and the Role of Visibility
Visibility remains the foundation of effective OT security for industrial automation. Without accurate, current insight into assets and communications, even well-designed controls lose effectiveness.
Industrial environments require visibility that is:
- Passive, to avoid operational impact
- Continuous, to reflect real-world change
- Protocol-aware, to understand industrial behavior
Example from Manufacturing
In an automotive manufacturing plant, passive network monitoring revealed a group of PLCs communicating over a legacy protocol segment that was believed to be decommissioned. The communication was legitimate but undocumented. Without that visibility, a routine firewall change could have interrupted production.
This is where strong OT cybersecurity solutions create value: not by blocking traffic blindly, but by making industrial behavior visible and understandable.
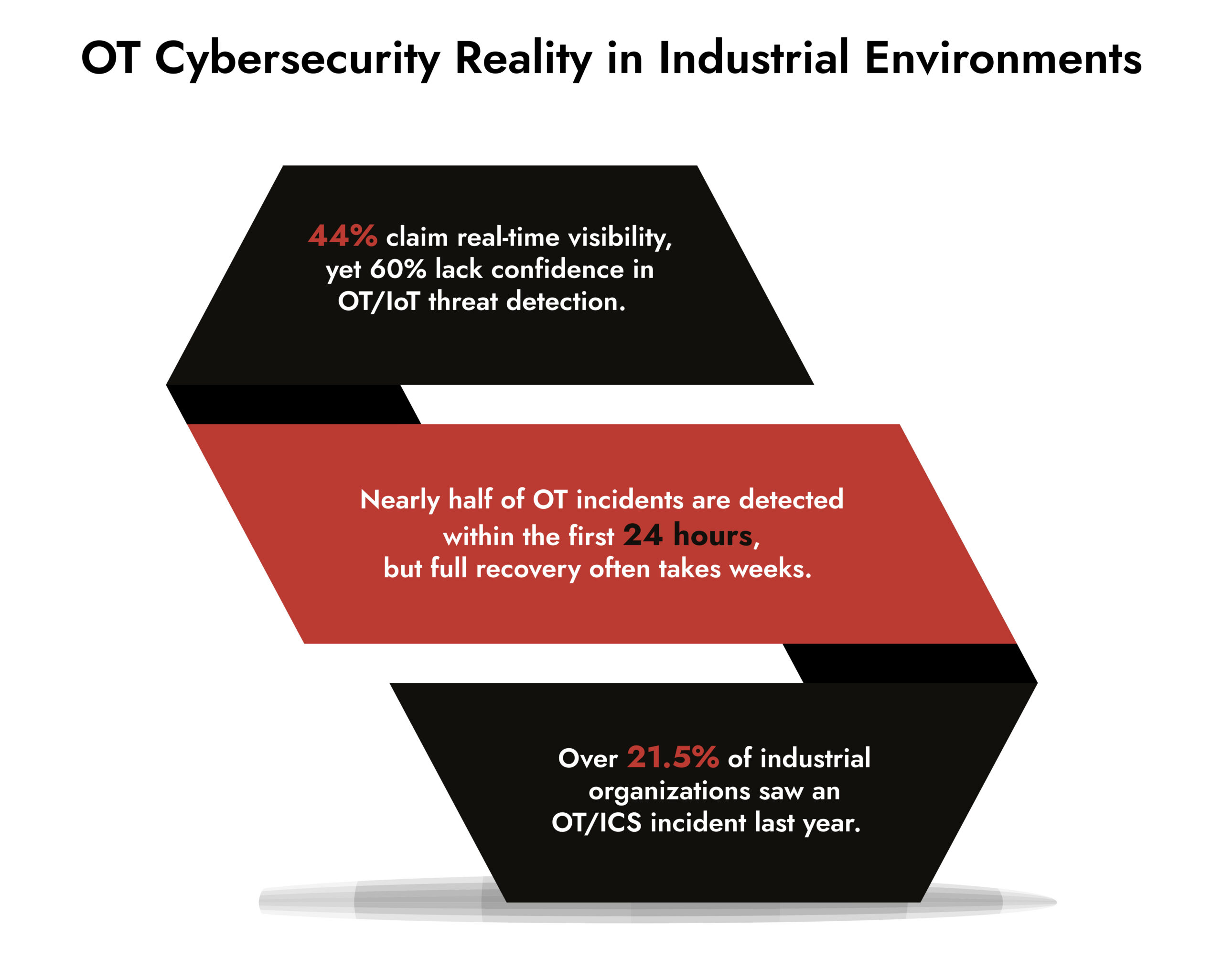
Sources- Businesswire.com, mbtmag.com, sans.org
OT Cybersecurity Solutions Must Align with Operations
In industrial automation, reliability comes first. Security controls must work quietly in the background without interrupting controllers, production lines, or safety systems. Even a well-intentioned tool can create risk if it introduces latency, scans sensitive devices, or changes network behavior. The right OT cybersecurity solutions strengthen visibility and detection while respecting uptime and operational stability.
Effective OT cybersecurity solutions typically share these characteristics:
Passive Asset Discovery
Industrial networks change quietly. New controllers appear during maintenance. Temporary laptops connect during troubleshooting. Passive monitoring detects these changes without introducing risk.
Protocol-Level Understanding
Knowing that traffic exists is not enough. OT threat detection depends on understanding what commands are being issued, how often, and from where.
Behavioral Monitoring Over Time
Industrial systems follow predictable patterns. Deviations often indicate misconfiguration, human error, or early-stage compromise.
Investigation-Ready Data
When issues arise, teams need answers quickly. Session and artifact reconstruction provide the context required to understand what happened and respond with confidence.
OT Cybersecurity Architecture for Industrial Scale
Industrial organizations rarely operate a single plant. Security architectures must support multiple sites, regions, and operational models.
A strong OT security architecture:
- Centralizes visibility across plants
- Preserves local operational control
- Supports enterprise-level investigation
- Integrates with existing SOC workflows
Example from Utilities
A regional utility used centralized OT monitoring to identify similar anomalous behavior across two geographically separated substations. The issue traced back to a shared engineering configuration, not malicious activity. Early visibility prevented unnecessary shutdowns.
This kind of insight only emerges when OT cybersecurity operates as part of a broader security ecosystem.
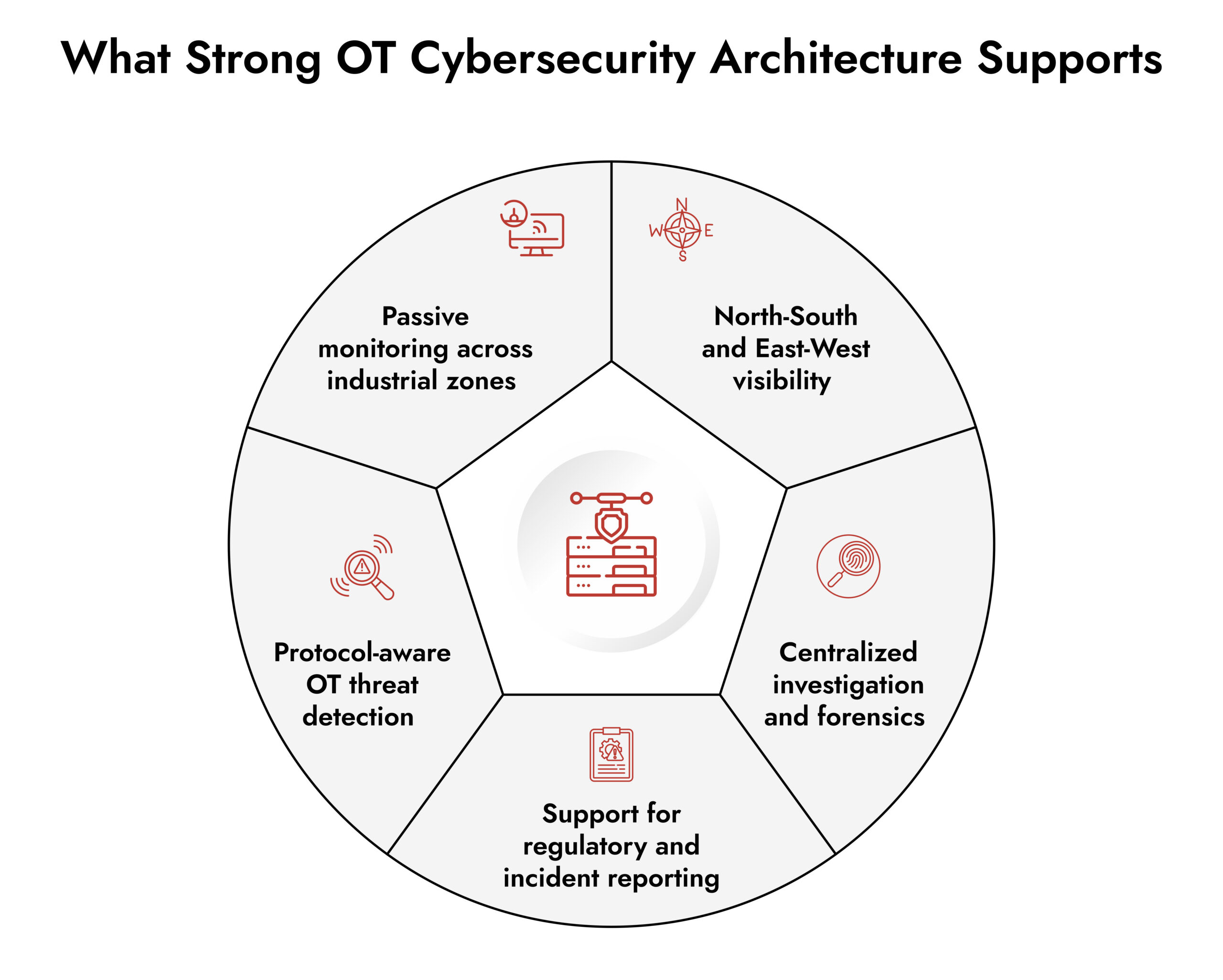
Evaluating OT Cybersecurity Platforms Without Overcomplication
Choosing among leading OT security companies for industrial systems does not require chasing every feature. It requires asking the right questions.
Key evaluation criteria include:
- Can the platform observe industrial traffic without scanning or agents?
- Does it understand industrial protocols at the command level?
- Can teams reconstruct activity during investigations?
- Does it scale across multiple plants and regions?
- Can it integrate with existing cybersecurity operations?
The best cybersecurity company for OT security supports clear decision-making under operational pressure, not just detection metrics.
Unify IT and OT Threat Detection with NetWitness® and DeepInspect
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
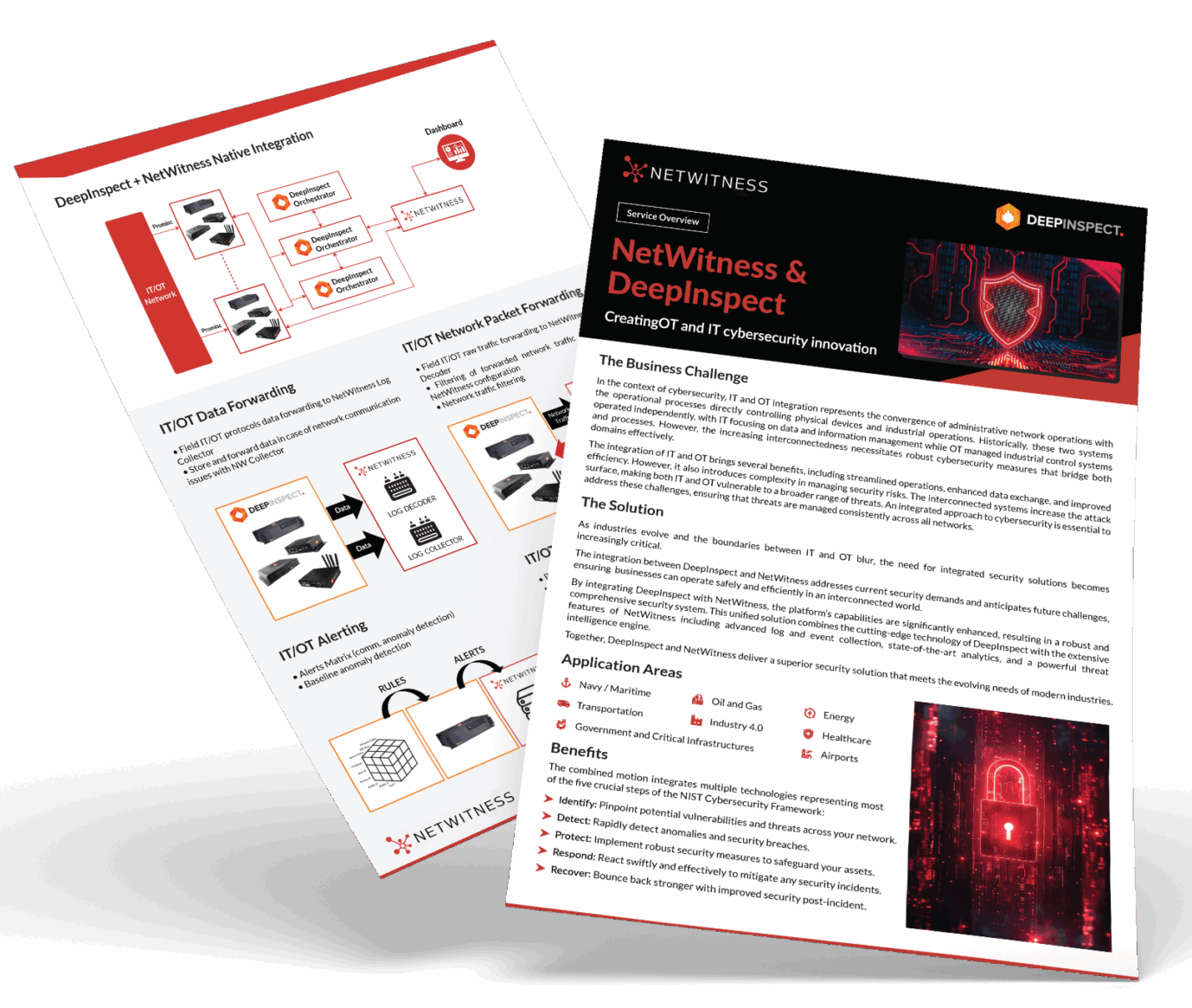
NetWitness and OT Cybersecurity for Industrial Automation
NetWitness supports OT cybersecurity through a visibility-first, investigation-driven approach that aligns with industrial realities.
By extending deep network visibility into operational environments, NetWitness enables:
- Passive monitoring of industrial traffic
- Protocol-aware analysis without disrupting systems
- Correlation of OT activity with enterprise security data
- Session reconstruction for investigation and response
This approach helps organizations manage OT security for industrial automation while maintaining operational stability and investigative depth.
Securing OT environments isn’t only a cybersecurity exercise. It’s an engineering decision. Every device introduced into an industrial setting, including monitoring sensors or network equipment, must meet environmental and safety standards specific to that facility. Whether it’s temperature tolerance in a steel plant, explosion-proof certification in oil and gas, humidity resistance in food processing, or pressure and vibration standards in manufacturing, security hardware must align with operational realities. In OT, deployment is not just about functionality, it’s about compliance with industrial safety, reliability, and environmental requirements.
— JooYeong Ang, NetWitness
How do you Choose the Right OT Cybersecurity Solution?
Choosing the right OT cybersecurity solution starts with understanding your operational environment.
Look for solutions that:
- Respect uptime and safety requirements
- Provide continuous, passive visibility
- Explain behavior, not just generate alerts
- Support investigation across IT and OT security
- Scale as industrial operations grow
When security teams can clearly see and understand industrial activity, they can protect it without slowing it down.
Conclusion
Industrial automation is an area of continuous evolution. Cybersecurity must follow that same continuum and therefore evolve responsibly and thoughtfully as well.
As 2026 begins, OT (operational technology) cybersecurity should not create fear or a sense of restriction. Instead, it should offer clarity, confidence, and control. When choosing and using the right OT cybersecurity solutions, an organization should operate safely. It should also respond quickly when needed and continue to grow without facing extra risks. This balance is what modern industrial security is all about.
If you are re-evaluating the role of OT cybersecurity within your industrial automation plan, this is the perfect moment to assess if your existing visibility, detection, and investigation tools are designed to meet the needs of contemporary plants.
Frequently Asked Questions
1. What is OT cybersecurity?
OT cybersecurity focuses on protecting industrial systems that control physical processes, ensuring availability, safety, and integrity while accounting for operational constraints.
2. How do you choose OT cybersecurity solutions?
Choose solutions that provide passive visibility, protocol-aware monitoring, behavioral detection, and investigation capabilities aligned with industrial operations.
3. What are the common challenges in asset visibility for industrial networks?
Legacy systems, undocumented changes, vendor access, flat network designs, and temporary engineering assets limit visibility.
4. What are the key features to look for in an OT cybersecurity solution?
Passive monitoring, continuous asset discovery, OT threat detection, session reconstruction, and strong architectural integration.
5. What are the best tools for OT visibility in industrial environments?
Tools that deliver deep network visibility, industrial protocol awareness, and forensic-ready data without disrupting operations.
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.