How Do I Choose a Network Detection and Response Platform?
If you’re asking, how do I choose a network detection and response platform, focus on five essentials:
- Deep packet-level visibility across hybrid environments
- Behavioral analytics and advanced threat detection
- Integration with SIEM, SOAR, and EDR tools
- Built-in investigation and response capabilities
- Ongoing expert support from experienced NDR vendors
The right network detection response platform should not just detect threats but help your team investigate and act quickly.
Introduction
Modern enterprises can’t afford blind spots. Attackers are getting smarter, networks are expanding across cloud and hybrid infrastructures, and security teams are stretched thin. That’s why more organizations are turning to a network detection and response partner to strengthen their defenses.
But here’s the challenge: not all NDR vendors are created equal. Some focus only on surface-level visibility. Others drown analysts in alerts without context. If you’re evaluating network detection and response services, you need to know what separates a solid vendor from one that’s going to leave you exposed.
Before we get into the five must-have qualities, let’s answer the obvious question.
Why is Network Detection and Response So Valuable?
If you’ve ever asked yourself why network detection and response is so valuable, the answer comes down to one thing: visibility.
Endpoints can be compromised. Logs can be incomplete. But the network doesn’t lie. Every interaction, legitimate or malicious, leaves a trace of network activity and traffic. That’s why enterprise network detection and response have become such a critical part of the security stack.
Here’s what it brings to the table:
- Pervasive visibility into east-west traffic, not just north-south perimeter flows
- Faster detection of sophisticated threats that bypass endpoint and email security
- Rich forensic data for investigating incidents and understanding root causes
- Context that reduces alert fatigue and helps SOC teams focus on real risks
In short, NDR closes blind spots. But only if you choose the right network detection and response partner.
1. Comprehensive Network Visibility:
The foundation of any network detection response platform is visibility. If your provider can’t see what’s happening across your environment, they can’t detect or respond effectively.
Network visibility means more than a few NetFlow logs. Look for top network detection response vendors that capture full packets, generate rich metadata, and integrate across hybrid or multi-cloud environments. Integrating multiple log sources, including security detections and threat intelligence, improves correlation and investigation accuracy across your organization’s infrastructure.
The goal is simple: monitor traffic everywhere. On-premises. Virtual environments. Public clouds.
Ask yourself:
- Can this provider inspect encrypted traffic?
- Can they reconstruct entire sessions for forensic review?
A strong network detection and response partner should be able to answer yes to both.
2. Advanced Threat Detection and Analytics:
Seeing traffic is step one. Interpreting it is where the real value shows up.
A mature network detection and response solution should help your team cut through noise and focus on what matters. Attackers don’t reuse the same techniques forever. Signature-based detection alone is not enough.
The best NDR vendors combine:
- Behavioral analytics to flag unusual activity and deviations from normal patterns
- Machine learning to adapt to emerging attack techniques
- Threat intelligence integration to prioritize alerts
- User and entity behavior analytics (UEBA) to detect insider risk
Advanced analytics and meaningful data retention reduce false positives. That matters. Because fewer false alerts mean more time investigating real threats.
A strong network detection response platform should not just say something that looks suspicious. It should explain why it matters and what to do next.
3. Integration and Scalability Across Your Security Stack
Your security environment is already layered. Adding another tool should not create friction.
That’s why leading network detection and response vendors build integration into the core of their platform.
Ask:
- Does the platform integrate with SIEM, SOAR, and EDR?
- Can it feed enriched network data into existing workflows?
- Will it scale as traffic grows across cloud, edge, and remote environments?
Effective event management is critical. Alerts and telemetry must correlate cleanly across systems, so analysts can see the full attack chain.
The right network detection and response partner acts as a force multiplier. Not another silo.
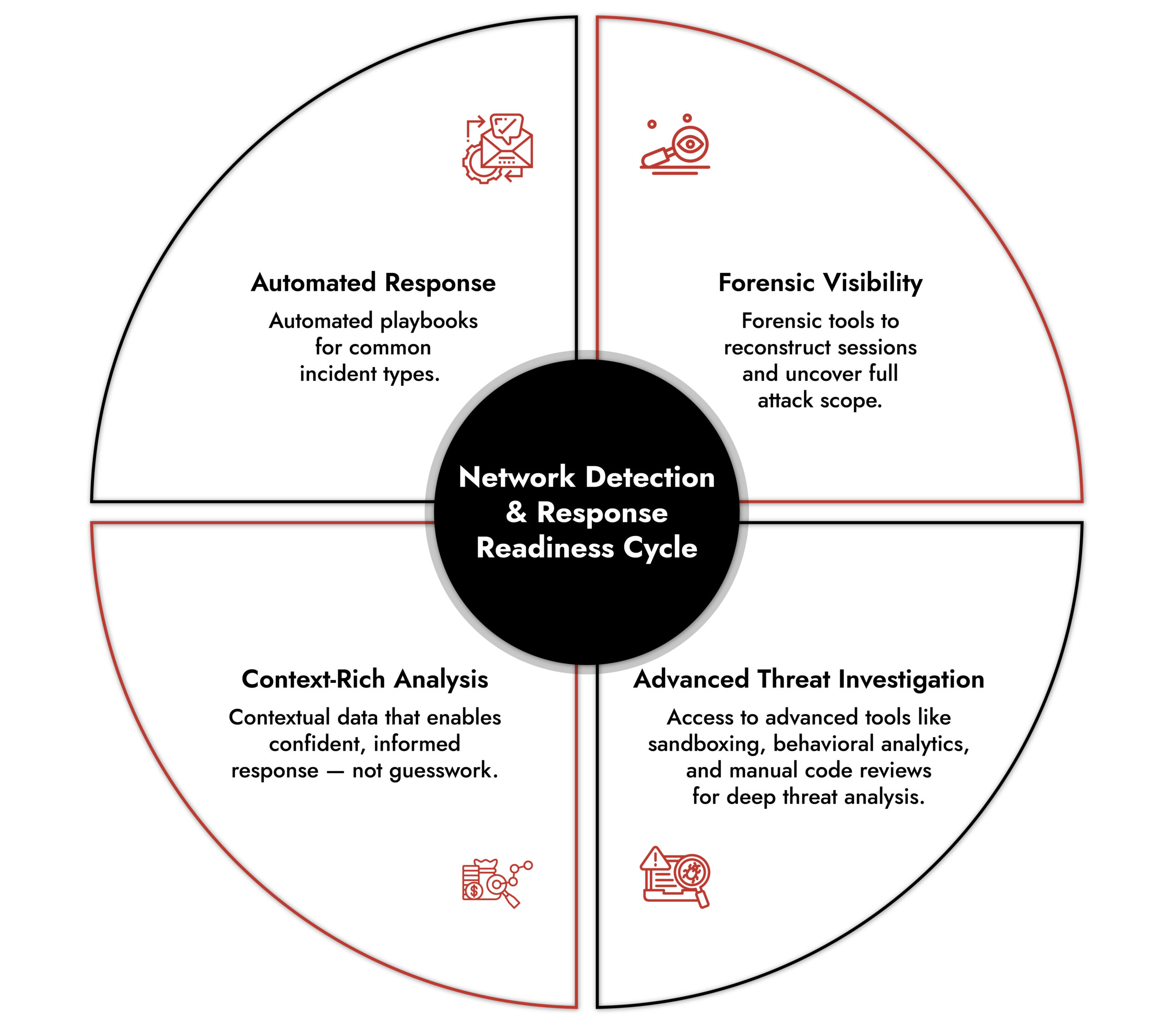
4. Built-in Response and Investigation Capabilities
Detection without action creates backlog. A valuable network detection and response partner must support investigation and response, not just alerting.
Look for:
- Automated playbooks for common incident types
- Forensic tools that reconstruct sessions and attack timelines
- Context-rich alerts that reduce guesswork
- Advanced investigation capabilities such as sandboxing, behavioral analytics, and deep traffic inspection
When comparing top network detection response vendors, look closely at what happens after detection. Do they help you contain threats? Or just notify you?
A strong network detection response platform shortens the path from detection to remediation.
5. Expertise and Ongoing Support from Proven NDR Vendors
Technology alone won’t solve the problem.
The best network detection and response services come with experienced professionals who understand security operations and threat detection.
A true network detection and response partner will:
- Help fine-tune detections over time
- Provide industry-specific guidance
- Support investigations when incidents occur
- Offer access to threat hunters who proactively analyze suspicious behavior
Threat hunters add depth that automation alone cannot. They bring judgment, context, and experience.
When evaluating NDR vendors, ask whether they work alongside your team or simply hand off software.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.
NDR Solution Evaluation: How to Compare and Choose the Right Fit
Selecting the right network detection and response (NDR) solution requires more than reviewing a feature grid.
If you’re wondering again, how do I choose a network detection and response platform, focus on alignment:
- Does it fit your environment?
- Does it scale with growth?
- Does it integrate with your workflows?
- Does the vendor provide meaningful support?
The ideal network detection and response solution delivers deep visibility across on-premises, cloud, and hybrid environments. It integrates cleanly with existing security tools and scales as traffic expands.
Vendor expertise matters just as much as technology.
Key Evaluation Criteria
- Visibility: Deep packet-level monitoring of all network traffic
- Threat Detection: Support for both known and unknown threat detection
- Scalability: Ability to handle growth in data and infrastructure
- Expert Support: Ongoing training, intelligence, and operational guidance
When comparing top network detection response vendors, use these criteria as your baseline.
Final Word: Choosing the Right Network Detection and Response Partner
Choosing a network detection and response partner isn’t about flashy features. It’s about making sure no essential capability is missing.
At a minimum, your network detection response platform should provide:
- Full visibility and anomaly detection across infrastructures
- Historical access to traffic and threat events
- Customizable detections aligned to your strategy
- The ability to detect lateral movement and uncover emerging threats
This is where NetWitness NDR stands out. It delivers real-time visibility with rich metadata, patented parsing and analytics, and deep forensic tools. With support for hundreds of protocols and built-in behavioral analytics, it gives enterprises both speed and depth in threat detection.
Don’t settle for surface-level network detection and response.
Explore the NDR Solutions datasheet or contact NetWitness to learn how to eliminate blind spots in your network. Meet NetWitness experts to see how network detection and response helps combat advanced persistent threats.
Frequently Asked Questions
1. What is a network detection and response partner?
A network detection and response partner is a provider that helps organizations monitor, detect, and respond to threats across their network using advanced NDR services and tools. These services enable organizations to identify and mitigate malicious activities from threat actors.
2. Why is choosing the right NDR specialist important?
The right NDR specialist ensures comprehensive visibility, advanced threat detection, and effective response, reducing blind spots and protecting enterprise networks from sophisticated attacks.
3. What services do network detection and response vendors offer?
Top NDR vendors provide full-packet capture, behavioral analytics, threat intelligence integration, incident response tools, and ongoing support to help security teams detect and respond to threats efficiently. In addition, leading NDR vendors leverage third-party tools to gather intelligence from external sources, further enhancing their threat detection and investigation capabilities.
4. Why is network detection and response so valuable for enterprises?
Network detection and response is valuable because it provides deep visibility into network traffic, identifies threats that bypass other security tools, and equips teams with context and analytics for faster, informed responses. NDR also enables proactively searching for hidden or undetected threats, allowing security teams to identify and mitigate risks before they cause harm.





