Key Takeaways
- SIEM use cases outline the procedures for configuring detections, dashboards, reports, and automated workflows within your security operations center. They transform unrefined log data into straightforward, actionable security insights.
- Current SIEM implementations need to deliver thorough security oversight across cloud settings, local infrastructure, OT/IoT devices, and endpoints of remote employees.
- Integrating SIEM with SOAR, NDR, and EDR – like in the NetWitness Platform – facilitates quicker investigations, automated reactions, and detailed visibility throughout the entire attack surface.
- Organizations ought to focus on 5-10 high-value use cases that correspond with their most significant risks instead of trying to initiate them all at once.
- These 10 applications encompass real-time oversight, detection of ransomware and insider threats, cloud protection, compliance, integration of threat intelligence, proactive searching, incident management, security orchestration, and monitoring of OT/IoT systems
Introduction: Why SIEM Tools Matter More Than Ever
Many organizations are not having issues because they don’t get enough data; they’re having issues because there is simply too much.
Everything is being logged from firewalls to cloud infrastructure to endpoints. Without some sort of structured detection logic applied to all this telemetry data, it turns into noise.
In steps security information and event management (SIEM) platforms, but just because you deploy one of the top SIEM solutions doesn’t mean that your security posture will automatically improve. The thing that determines whether you’re successful with your SIEM implementation is how you have configured it for particular, high-value use cases.
Ransomware groups are getting faster and identity attacks are becoming less noisy, and cloud misconfigurations can expose sensitive data in a matter of seconds. Therefore, a modern SIEM should be and act as a detection and response engine, and not just a data dump (or log warehouse).
The following 10 use cases will help you understand what effective security SIEM tools should look like today.
Top SIEM Use-Cases
1. Real-Time Monitoring Across Hybrid Environments
Modern infrastructure is fragmented. Data centers. AWS. Azure. SaaS apps. Remote users.
A strong use case for SIEM tools is correlating:
- VPN and firewall logs
- Identity provider events
- Endpoint activity
- Cloud audit trails
Detection examples include impossible travel logins, suspicious privilege escalation, and lateral movement patterns. Without unified visibility, attackers pivot quietly between environments.
2. Ransomware and Malware Detection
Ransomware remains one of the primary drivers behind enterprise SIEM solutions adoption.
Effective detection correlates:
- Suspicious PowerShell execution
- Mass file modifications
- Lateral SMB activity
- Outbound connections to malicious domains
The difference between containment and catastrophe often comes down to minutes. Leading SIEM threat detection systems combine endpoint signals, network behavior, and threat intelligence to generate high-confidence alerts early in the kill chain.
3. Insider Threat and Privileged Account Monitoring
Not every breach starts outside the organization. Monitoring privileged users requires:
- Identity logs
- HR system data
- File access logs
- Database audit trails
Behavioral baselining is critical. The best SIEM tools don’t just flag static rule violations. They detect deviations from established user patterns, such as abnormal access times or unexpected data downloads.
4. Cloud Security Monitoring
Cloud blind spots remain a common weakness. A modern SIEM tools list must include platforms capable of ingesting:
- AWS CloudTrail
- Azure AD logs
- SaaS audit trails
- IAM changes
Use cases include detecting exposed storage buckets, unauthorized API key creation, or suspicious admin activity in Microsoft 365.
Cloud-native detection is now a baseline expectation for top SIEM tools.
5. Compliance and Regulatory Reporting
For many organizations, SIEM began as a compliance investment.
Regulations like PCI DSS, HIPAA, SOX, and NERC CIP require:
- Centralized log retention
- Tamper-proof storage
- Auditable access records
Strong reporting capabilities remain foundational in security information and event management deployments. But mature programs move beyond compliance into active threat detection.
6. Threat Intelligence Integration
Raw logs lack context. Enriching detections with threat intelligence feeds allows SIEM threat detection engines to:
- Match outbound traffic to known malicious IPs
- Identify domains tied to ransomware campaigns
- Retroactively search logs after zero-day disclosures
This dramatically improves prioritization and reduces analyst fatigue.
7. Proactive Threat Hunting
Automation catches known patterns. Threat hunting uncovers what automation misses.
Advanced SIEM for SOC teams must support:
- Long-term log retention
- Fast query performance
- Cross-source pivoting
Hunters may search for encoded PowerShell usage across months of data or rare processes executed by service accounts.
The stronger the data foundation, the more effective the hunt.
8. Incident Investigation and Forensics
When an alert escalates, the SIEM becomes the system of record.
Key capabilities include:
- Timeline reconstruction
- Patient zero identification
- Lateral movement mapping
- Evidence preservation
Leading enterprise SIEM solutions integrate network and endpoint telemetry to provide deeper investigative context.
9. Automated Response and Orchestration
Alert fatigue is real. Automation is no longer optional.
Modern security SIEM tools integrate with SOAR platforms to:
- Disable compromised accounts
- Isolate infected endpoints
- Block malicious IPs
- Open ITSM tickets with context
The goal is reducing mean time to respond without overwhelming analysts.
10. OT and IoT Monitoring
Critical infrastructure introduces unique risk.
Industrial environments often include:
- SCADA systems
- ICS controllers
- Legacy OT devices
Many lack traditional logging. Network-based monitoring becomes essential. Advanced SIEM tools must support passive data ingestion and protocol awareness to protect high-value operational environments.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.

10 SIEM Use Cases Mapped to Security Goals
| Security Goal | SIEM Use Case |
| Visibility | Real-time monitoring |
| Ransomware Protection | Malware detection |
| Data Protection | Insider threat monitoring |
| Cloud Security | Cloud activity monitoring |
| Governance | Compliance reporting |
| Threat Awareness | Threat intelligence correlation |
| Proactive Defense | Threat hunting |
| Investigation | Incident forensics |
| Speed | Automated response |
| Operational Safety | OT/IoT monitoring |
How to Prioritize SIEM Use Cases
Trying to deploy everything at once rarely works. A practical rollout approach:
Phase 1: Log ingestion and compliance reporting
Phase 2: Core detection (ransomware, identity abuse)
Phase 3: Cloud and OT visibility
Phase 4: Automation and threat hunting maturity
Success metrics include:
- Mean time to detect
- Mean time to respond
- False positive rates
- Coverage across critical systems
The best SIEM tools evolve alongside business risk.
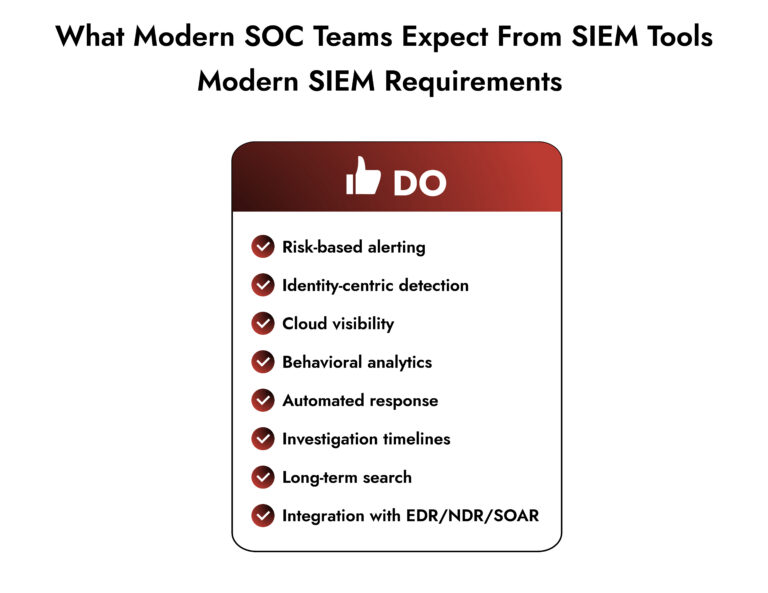
What Defines the Best SIEM Tools Today
When evaluating the best SIEM tools, look beyond marketing claims.
Key differentiators include:
- Hybrid cloud visibility
- Scalable log ingestion
- Behavioral analytics
- Threat intelligence enrichment
- Automation support
- Forensic investigation depth
Strong enterprise SIEM solutions balance detection accuracy with operational usability. The goal is empowering SOC teams, not overwhelming them.
Conclusion
The conversation around SIEM tools has shifted. It is no longer about collecting logs. It is about converting data into confident action. The organizations that succeed are not those with the most alerts. They are the ones with the clearest use cases, the right automation strategy, and a platform that supports how their SOC actually operates. That is what modern security information and event management is meant to deliver.
Frequently Asked Questions
1. What defines a top SIEM tool in 2026?
A leading SIEM in 2026 cuts through noise. It connects cloud, identity, and endpoint data, prioritizes real risks, and helps teams respond fast. It’s not about collecting more logs. It’s about acting on the right ones.
2. What are the key capabilities expected from leading SIEM tools?
Real-time detection, behavior analysis, useful log retention, compliance reporting, threat intel context, and the ability to trigger response actions automatically.
3. What are the top SIEM tools for enterprise security?
Enterprises typically evaluate platforms based on scale, automation, and investigation depth. Leading vendors provide integrated detection, response, and analytics rather than standalone logging.
4. What are the best SIEM tools available for small businesses right now?
Cloud-hosted platforms with ready-made rules and simple management. Small teams need less tuning and more guidance from the system.
5. Which SIEM tools integrate well with cloud security services?
Modern solutions integrate directly with AWS, Azure, Google Cloud, and SaaS audit logs. Native API ingestion and identity monitoring are essential requirements today.
6. How can I find SIEM tools that specialize in automated incident response?
Look for platforms offering built-in playbooks or native SOAR capabilities. If the product requires manual triage for most alerts, automation maturity is low regardless of marketing claims.
Choose the Right SIEM with Confidence