What Should Organizations Focus on in 2026?
- Improve awareness of cybersecurity threats caused by social engineering based on artificial intelligence.
- Regularly conduct assessments of potential risks associated with any supply chain exposure.
- Implement cutting-edge technologies to provide visibility, integrity monitoring, and automatic monitoring.
- Use an integrated approach between your existing network, endpoints, logs/telemetry.
- Ensure that all elements of your business strategy will be compliant with regulatory requirements, resilient economically and operationally, and able to maintain their continuity after experiencing disruption.
Introduction
Another year on the calendar, another guarantee that the technology on which we are so reliant will demonstrate new and largely unanticipated consequences. Perhaps nowhere is this clearer than in the world of cybersecurity.
As we look at these predictions in 2026, the themes of autonomy, software supply chain exposure, and crime-as-a-service are not fading. They are evolving. Let’s take a brief look at three themes shaping modern cybersecurity solutions.
3 Cybersecurity Predictions Shaping for Business in 2026
A is for Autonomy: AI, Automation and Attacker Innovation
The automobile industry is the very first thing we think of when we hear autonomy, and there is no denying the promise of fully automated smart vehicles and how they can improve logistics, personal transport, and last-mile delivery.
Through a darker looking glass, while we’ve seen proofs-of-concept in the past demonstrating unauthorized control of a moving vehicle, look for exploits relating to vehicular data: deliberate obfuscation of real-time geolocation coordinates and tampering of previously recorded data will surface as new areas of mischief for researchers and criminals alike.
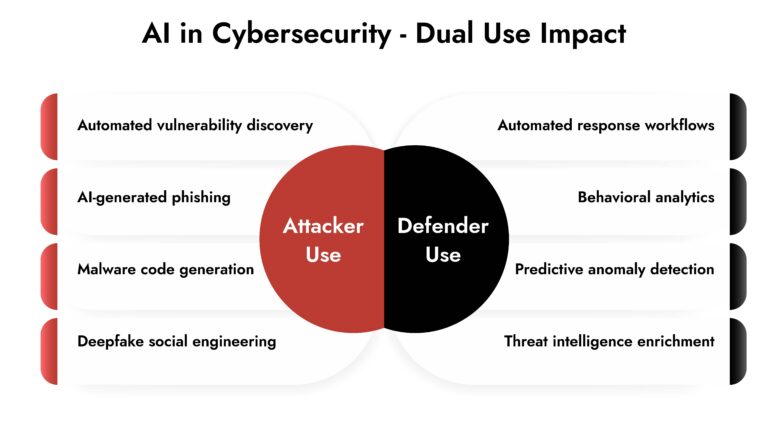
But autonomy lives well beyond one industry. Expect to see dramatic developments leveraging artificial intelligence, where natural language processing tools are used to create malware, identify weaknesses in system design, craft harder-to-detect phishing emails, and script recommended interactions that amplify social engineering attacks.
For security teams, this shifts the conversation from reactive defense to structured cybersecurity awareness and continuous cybersecurity risk assessment.
Tools designed to simplify the SOC’s responsibilities through automation, including SOAR platforms and numerous cybersecurity tools, will remain significant targets for attackers. In 2026, unconfirmed automation becomes a threat.
Organizations adopting advanced cybersecurity protocols must create protections for AI-powered operations, verification systems for automated activities, and thorough telemetry data across all environments.
B is for BOMs: Supply Chain, Integrity and Visibility
Software bills of material will continue to play an essential role in securing supply chains for governments and businesses. But reliance on SBOMs depends on a comprehensive understanding of the volume of open-source code running in every organization today.
Being able to point to the provenance of a piece of code is useless if you haven’t identified it in the first place. We will see SBOM-reliant organizations announce incidents rooted in incomplete inventories.
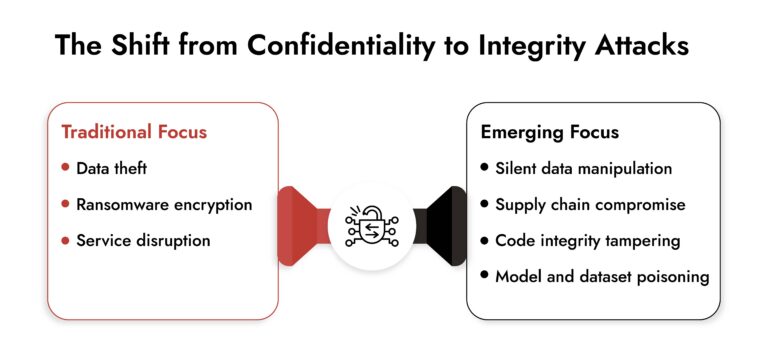
Historically, breaches focused on confidentiality and availability. In 2026, integrity becomes a quiet battlefield.
Instead of stealing data, attackers may silently modify it. Financial records. Configuration files. Algorithmic parameters. Training data sets. The impact is subtle but strategic.
This is where visibility becomes foundational. Observability in development environments, runtime environments, and production infrastructure is no longer optional.
Defenders monitoring network traffic, logs, and endpoints through an integrated cybersecurity platform have the best chance of detecting integrity-focused attacks in motion.
For leadership, this reinforces a key shift: cybersecurity services must extend beyond perimeter defense into code transparency, asset discovery, and third-party risk governance.
C is for CaaS: The Economics of Cybercrime
Crime-as-a-service lowers the barrier to entry for criminals and nation-states alike. Lack of technical expertise is easily addressed with payment. Capabilities increase while prices decrease.
Cybercrime operates under a business model. Healthy businesses innovate. CaaS providers refine their tooling to bypass improved defenses.
Expect continued waves of malicious mobile applications designed to eavesdrop on communications, access photos and files, or act as stepping stones into broader environments. Old techniques persist because they still generate returns.
To counter this economic asymmetry, organizations increasingly combine internal capabilities with managed detection and response providers. This hybrid approach aligns technology with human expertise and layered cybersecurity solutions.
In practical terms, cybersecurity for business must be treated as a revenue protection function. Security investment now directly correlates to operational uptime, regulatory posture, and brand integrity.
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.

Closing Perspective
Autonomy introduces efficiency and new attack surfaces. BOMs highlight the limits of incomplete visibility. CaaS reminds us that adversaries operate with market logic.
What this truly signifies is straightforward: security maturity in 2026 relies less on standalone tools and more on cohesive cybersecurity systems, organized governance, and strategy aligned with business objectives.
Organizations that view cybersecurity for business as a fundamental operational component instead of a mere technical consideration will be more adept at handling disruptions and adjusting to whatever the upcoming changes entail
Frequently Asked Questions
1. How should security teams respond to AI-augmented attacks?
Security teams should improve cybersecurity awareness, confirm automated processes, and implement multi-layered advanced cybersecurity solutions that leverage AI analytics and human analysis. Continuous testing and red teaming are essential.
2. What role does visibility play in detecting integrity-focused attacks?
Visibility is key. Without integrated telemetry from networks, endpoints, logs, and code repositories, silent data manipulation can remain hidden. A single, integrated cybersecurity platform facilitates correlation and quicker identification of integrity breaches.
3. Why is supply chain security a top priority for 2026?
Modern organizations depend heavily on third-party code, SaaS providers, and open-source components. Incomplete inventories undermine defense strategies. Comprehensive asset discovery and continuous cybersecurity risk assessment reduce exposure.
4. Do past cybersecurity predictions still apply in 2026?
Yes, but they evolve. Autonomy expands beyond vehicles into AI-driven operations. Supply chain threats grow more subtle. Crime-as-a-service is becoming more efficient. What changes are scale, speed, and economic accessibility.