What is Operational Technology (OT) security?
Operational Technology (OT) security focuses on protecting the systems that control physical processes such as manufacturing lines, power grids, and water treatment facilities. Unlike IT security, it prioritizes safety and availability, ensuring operations run without disruption while preventing threats that could cause real-world damage.
There’s a reason Operational Technology security has gone from an afterthought to a boardroom conversation in about five years flat. Industrial systems that ran quietly in isolation for decades are now networked, cloud-connected, and remotely accessible. That changed everything including the threat picture.
Operational Technology security is the practice of protecting the hardware and software that run physical processes. Not data. Physical things. Assembly lines, power generation equipment, water treatment dosing systems, oil pipelines, HVAC controllers in hospitals. When these systems fail or worse, get manipulated the consequences aren’t a data breach. They’re operational shutdowns, safety incidents, and in the worst cases, harm to people.
This blog breaks down the Operational Technology security landscape in a way that’s useful: what it is, where the risk lives, what smart enterprises are doing about it, and why the frameworks that work in IT don’t simply translate here.
Why Operational Technology Security Is a Different Problem Than IT Security
Start here, because this is where most organizations go wrong.
IT security is built around three priorities: confidentiality, integrity, and availability in that order. If you must take a server offline to patch a critical vulnerability, you do it. You schedule a maintenance window, and you do it.
OT doesn’t work that way. A blast furnace doesn’t have a maintenance window for an emergency patch. A water treatment facility can’t go offline because a security team found a vulnerable HMI. The priority order in OT flips: safety first, then availability, then integrity, and confidentiality comes last. That’s not a flaw in the design philosophy; it’s the correct set of priorities for systems where a misconfiguration can physically injure someone.
This shapes every single decision in OT cybersecurity. It shapes which tools you can use. It shapes your patching strategy, your incident response playbooks, and your architecture choices. Industrial cybersecurity that doesn’t account for this isn’t industrial cybersecurity. It’s IT security applied badly to a different problem.
The IT/OT Convergence and What It Actually Did to the Attack Surface
For most of the last four decades, industrial control systems were air gapped. Physically isolated. The only way to interact with them was to be standing in front of them or connected to a dedicated, closed network. That isolation was a security feature, even if nobody called it that.That isolation is largely gone now.
Remote monitoring, predictive maintenance, cloud-based analytics, ERP integration with production scheduling all of these require connectivity between the business network and the plant floor. There are real operational benefits. There are also real consequences for security.
When your corporate IT network connects to your OT network, every vulnerability that exists on the IT side becomes a potential entry point to your industrial environment. A phishing email on a corporate laptop. Stolen VPN credentials. A compromised vendor laptop plugging into your network during a maintenance visit. These are all realistic paths that attackers have actually used.
IT/OT convergence is not going in reverse. The efficiency gains are too significant. Which means enterprises have to get serious about managing the risk that comes with it, rather than pretending the boundary still exists.
The Threat Vectors Specific to OT Environments
OT environments face some threats common to IT ransomware, credential theft, insider threats and some purpose-built for industrial systems. Knowing the difference matters for how you prioritize.
ICS-targeted ransomware. Some ransomware is engineered specifically to identify and kill industrial control system processes before encrypting. That’s a different threat category than generic ransomware that stumbles into an OT network.
Nation-state actors. Critical infrastructure has been a documented nation-state target for over a decade. The intent often goes beyond disruption attackers have specifically targeted safety systems, the layer designed to prevent physical harm.
Supply chain attacks. Compromising a trusted industrial software vendor’s update mechanism is one of the cleanest ways into multiple OT environments at once. Vendor trust is a real attack surface.
Insider threats with physical access. OT has a physical dimension IT doesn’t. Someone with legitimate access to a control room or substation can cause damage that no network control fully prevents.
IT-side entry, OT-side impact. Many OT incidents don’t start in OT. Attackers breach the IT network, find the connection points, and either pivot directly into OT or force an operational shutdown by taking IT systems offline. The OT environment never needed to be the initial target.
Legacy Systems: The Problem That Doesn’t Have a Clean Answer
Walk through the control systems of a 30-year-old manufacturing facility or a regional utility and you’ll find equipment running Windows XP embedded, proprietary real-time operating systems, and protocols like Modbus RTU that were designed when network connectivity meant a serial cable.
These systems cannot be patched in the conventional sense. The vendor may no longer exist. The original engineers may be retired. A patch may require recertification of the entire system, which takes months and costs more than the equipment is worth. And the equipment itself may be mechanically and functionally fine there’s no operational reason to replace it.
The answer in OT security for legacy systems is compensating controls. You can’t patch the system, so you protect it by controlling everything around it. Network monitoring that detects anomalous behavior. Tight network segmentation that limits what the system can communicate with. Physical access controls. Application whitelisting on adjacent systems where possible. Removal of unnecessary network paths.
This approach works. It’s not as clean as patching, but it’s real risk reduction. The key is being systematic about it documenting the compensating controls for each legacy asset and reassessing as the environment changes.
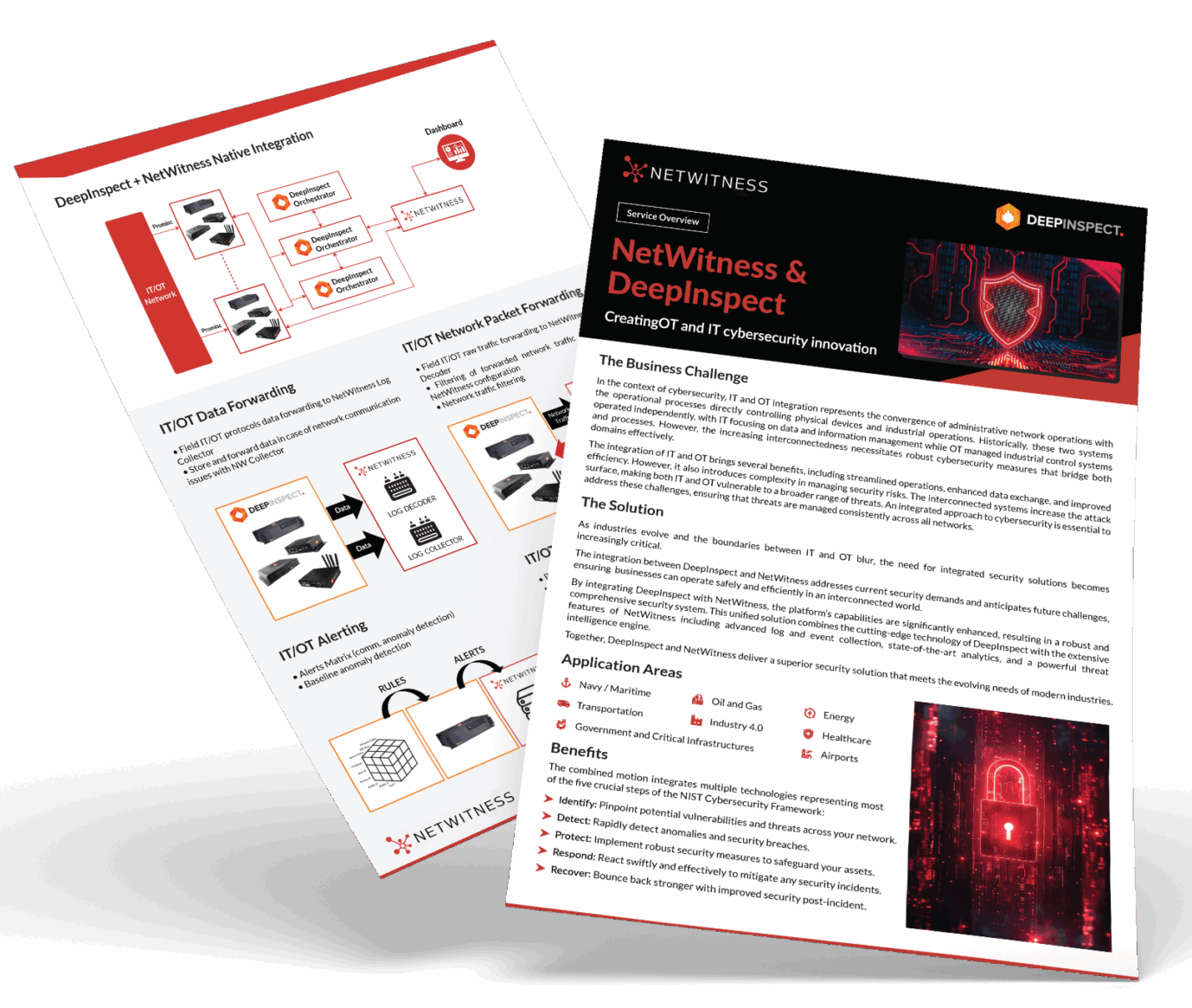
Unify IT and OT Threat Detection with NetWitness®
-Correlate IT and OT telemetry for end-to-end operational visibility.
-Detect advanced threats across industrial and enterprise networks with protocol-level intelligence.
-Accelerate investigations using enriched OT context and unified analytics.
-Reduce blind spots and strengthen response across converged IT/OT environments.
OT Asset Visibility: The Foundational Problem
Here’s something that surprises people outside the industrial security world: most enterprises don’t have an accurate, current inventory of what’s on their OT network.
This isn’t carelessness. OT environments grow organically over decades. Equipment gets added during plant expansions. Vendors install monitoring devices during maintenance. A technician adds a wireless access point for convenience. Nobody updates the asset register for any of it.
Without accurate asset visibility, every other security function is degraded. You can’t prioritize vulnerabilities you don’t know exist. You can’t build segmentation around assets you haven’t mapped. You can’t detect anomalies if you don’t know what normal looks like for every device.
OT-specific asset discovery tools solve this using passive monitoring they sit on the network, watch traffic, and fingerprint devices by how they communicate without sending active probes that could disrupt sensitive equipment. Over days and weeks, you build a living inventory that reflects what’s actually on the network.
This is typically where an Operational Technology security assessment starts. Everything downstream depends on it.
OT Threat Detection: Why Industrial Protocols Matter
Standard security monitoring doesn’t understand industrial protocols. Your SIEM knows what an HTTP request looks like. It doesn’t inherently know what a normal Modbus read looks like versus a Modbus write command that shouldn’t be coming from that source.
OT threat detection works by establishing behavioral baselines for industrial communication patterns. Which devices talk to which other devices. What commands appear in normal operations. What traffic volume is expected at different points in a production cycle. When the process is in normal operation versus startup or shutdown.
Deviations from baseline are the signal. A controller sending a command type it’s never sent before. An engineering workstation initiating connections to production controllers at 3am when no engineers are scheduled. A device that’s been silent for months suddenly generating network traffic. These anomalies aren’t definitive proof of attack but they’re where investigations start.

Strategic Priorities: What Enterprises Should Actually Be Doing
The gap between knowing Operational Technology security matters and executing a coherent program is where most enterprises are stuck. The strategic imperatives are actually pretty clear:
Visibility first. Deploy OT-specific asset discovery and passive network monitoring before you do anything else. You cannot make good risk decisions without an accurate picture of your environment.
Segment based on reality, not diagrams. Conduct an architecture review that maps actual communication flows. Build segmentation zones around what you find, not what your network diagram says should be there. Implement industrial firewalls and data diodes at zone boundaries based on criticality.
Apply Zero Trust principles to OT access. Remote access to Operational Technology security for employees and vendors needs to go through privileged access management. No shared credentials. No persistent connectivity. Session-level access with full logging. Multi-factor authentication everywhere it can be supported.
Build OT-specific incident response playbooks. A generic IR playbook that says “isolate the affected system” is dangerous in an OT context. Isolating a PLC mid-process can have immediate physical consequences. Playbooks need to account for safety implications, involve OT engineers in decisions, and define escalation paths that include operational leadership.
Why NetWitness OT
Most security platforms were built for IT and retrofitted for OT. NetWitness OT is designed the other way around purpose-built for industrial environments, from production floors to critical infrastructure.
It centralizes OT visibility, automates threat detection, and runs asset discovery simultaneously solving the two problems that leave most industrial environments exposed. Type-approved hardware, unified IT/OT security, custom protocol dissection, and dedicated forensic storage mean you’re not piecing together an incomplete picture when something goes wrong.
Conclusion
The Operational Technology security problem is not going to simplify. Industrial environments are getting more connected, threat actors are getting more capable, and the consequences of getting this wrong are severe enough that regulators in multiple sectors are starting to mandate specific controls rather than suggesting them.
The enterprises that handle this well are the ones treating Operational Technology security as its own discipline not a subset of IT security, not a compliance checkbox. A different problem requires a different approach. The good news is that the frameworks, tools, and expertise exist to do this right. What’s required now is the organizational commitment to actually use them.
Frequently Asked Questions
1. What makes OT security fundamentally different from IT security?
The priority order flips. IT puts confidentiality first; OT puts safety and availability first. That means standard IT moves aggressive patching, active scanning, isolating systems mid–incident can be damaging or outright dangerous in an industrial environment.
2. What are the most common OT security vulnerabilities enterprises face?
Flat unsegmented networks, legacy systems that can’t be patched, default credentials on industrial devices, and poorly controlled vendor access. Most industrial environments also have zero visibility into what’s actually happening on their control system networks which is its own serious problem.
3. Which industries carry the highest OT security risk?
Energy, oil and gas, water and wastewater, manufacturing, and pharmaceuticals. These sectors combine aging infrastructure, high operational consequence, and growing nation–state interest a difficult combination to defend against.
4. How does OT threat detection work in practice?
It’s network–based and behavioral. You baseline normal industrial communication patterns, then monitor for deviations unexpected commands, unknown devices, lateral movement from the IT side. The tools that do this well are deployed passively so they don’t touch or disrupt sensitive equipment.
5. What is the Purdue Model and is it still relevant?
It’s a hierarchical framework that organizes industrial systems into levels from physical processes up to enterprise IT. Still useful as a mental model for segmentation and trust levels, even if the 1990s architecture doesn’t map perfectly to today’s cloud-connected environments.
6. What should an OT security assessment cover?
Asset inventory, network architecture review, vulnerability identification with OT–specific prioritization, access control evaluation, and incident response readiness. The output that matters is a risk register ranked by operational impact not just technical severity scores.
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.