What is Cybersecurity for Telecom Industry?
Cybersecurity for Telecom Industry refers to the strategies, technologies, and operational controls used to protect telecom networks, subscriber data, signaling systems, and 5G infrastructure from cyberattacks and insider threats.
It includes:
- Advanced telecom network security architecture
- Real-time telecom threat detection
- 24/7 telecom SOC monitoring
- Telecom insider threats prevention controls
- Protection against telecom cloud security challenges
Because telecom operators manage national-scale infrastructure and millions of customer records, cybersecurity is mission-critical for service continuity and regulatory compliance.
Introduction
The telecom industry runs the digital world. Every call, transaction, authentication request, and cloud workload passes through telecom infrastructure. That makes telecom operators more than service providers. They are data custodians at national scale.
Here’s the reality. When telecom security fails, the impact is massive. Personal data leaks. Critical services go down. National infrastructure is exposed. And trust disappears overnight.
This guide breaks down Cybersecurity for Telecom Industry in practical terms. No theory. Just what telecom providers need to protect networks, subscribers, and revenue.
Why Telecom Is a Prime Target for Cyber Attacks
Telecom operators manage:
- Subscriber identity data
- Call detail records
- Location data
- Payment and billing systems
- Core network infrastructure
- 5G edge computing nodes
That combination attracts advanced attackers.
Modern telecommunications cyber threats include:
- Nation-state espionage targeting 5G infrastructure
- Ransomware attacks on billing and OSS/BSS systems
- SIM swap fraud
- Distributed denial-of-service attacks
- API exploitation
- Supply chain compromise
- Insider misuse of subscriber data
Unlike other industries, telecom networks operate at carrier-grade scale. One misconfiguration can affect millions. One breach can compromise entire regions. What this really means is simple: telecom security is national infrastructure security.
The Expanding Attack Surface in Telecom Networks
Traditional perimeter security no longer works in telecom environments.
Why? Because telecom architecture has evolved:
- Virtualized network functions
- Cloud-native 5G cores
- Multi-access edge computing
- Open RAN components
- Third-party vendor integrations
Each layer introduces new cybersecurity risks.
Key Risk Areas
- Core Network Exposure – 5G cores are software-driven. That increases flexibility but also increases attack vectors.
- Cloud and Virtualization Risks – Telecom cloud security challenges include container vulnerabilities, misconfigured APIs, and insecure orchestration layers.
- Signaling Attacks (SS7, Diameter, 5G SBA) – Attackers exploit protocol weaknesses to intercept SMS or track subscribers.
- IoT Expansion – Billions of connected devices introduce unmanaged endpoints.
- Insider Threats – Employees and contractors with privileged access create serious internal risk.
Telecom operators cannot treat cybersecurity as a compliance checklist. It must be built into network design.
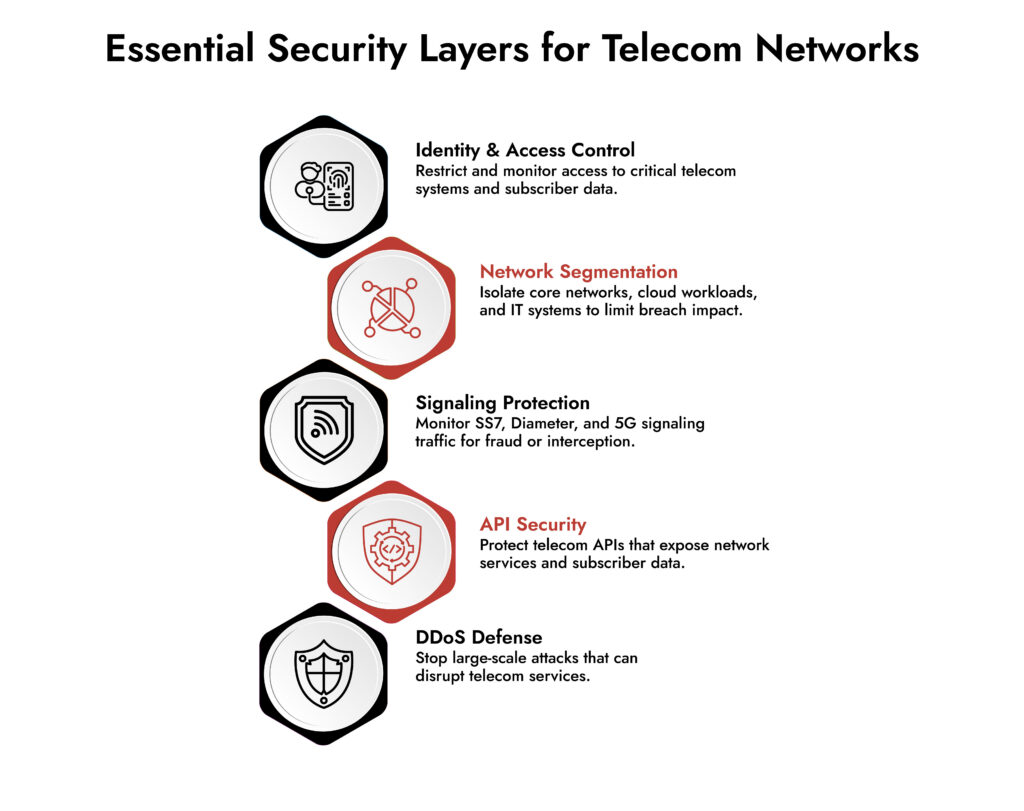
Core Pillars of Cybersecurity for Telecom Industry
A strong cybersecurity strategy for telecom providers rests on five pillars.
1. Telecom Network Security by Design
Security must be embedded in:
- Core network functions
- Access networks
- Transport layers
- Cloud environments
Zero trust segmentation is essential. Every function should authenticate and authorize before communication. Encryption must cover signaling, subscriber data, and interconnect traffic.
2. Continuous Telecom Threat Detection
Static defenses fail. Detection is where telecom wins or loses. Effective telecom threat detection includes:
- Real-time packet inspection
- Behavioral anomaly detection
- Signaling monitoring
- Lateral movement tracking
- API activity monitoring
The goal is visibility across core, edge, and cloud. Not partial logs. Full context.
3. Telecom SOC Monitoring
A dedicated telecom-focused SOC is critical. Telecom SOC monitoring should include:
- 24/7 network telemetry analysis
- Signaling anomaly alerts
- Subscriber data access monitoring
- Insider activity tracking
- Threat intelligence integration
Telecom environments generate massive data. A SOC must correlate events across RAN, core, and IT systems to avoid alert fatigue.
4. Telecom Insider Threats Prevention
Insider risk is often underestimated. Effective telecom insider threats prevention requires:
- Role-based access controls
- Privileged session monitoring
- Strict vendor access governance
- Behavioral analytics
- Data access auditing
No engineer should have unrestricted access without traceability.
5. Resilience and Incident Response
Telecom cannot afford prolonged downtime. Incident response must include:
- Network isolation capabilities
- Automated containment
- Rapid patch deployment
- Subscriber notification protocols
- Regulatory reporting workflows
Speed matters more than perfection during an incident.
Telecom Cloud Security Challenges in 5G
5G is software-defined and cloud-native. That changes everything.
How 5G Expands Risk
- Service-based architecture exposes APIs
- Network slicing increases segmentation complexity
- Edge nodes multiply distributed attack surfaces
- Virtualized cores rely on cloud orchestration
These telecom cloud security challenges demand:
- Container runtime protection
- API security gateways
- Micro-segmentation
- Continuous vulnerability scanning
- Secure DevOps for network functions
Without strong cloud controls, 5G becomes an attacker playground.
Unify Security Across Hybrid Environments
- Gain complete visibility across cloud, on-prem, and endpoints.
- Detect threats faster with correlated insights across all layers.
- Reduce complexity with a single, integrated security platform.
- Strengthen your defenses with NetWitness unified security
Building a Practical Cybersecurity Strategy for Telecom Providers
Let’s make this practical. A strong cybersecurity strategy for telecom providers follows these steps:
Step 1: Map Critical Assets
Identify:
- Subscriber databases
- Core network functions
- Billing systems
- Signaling gateways
- Cloud workloads
Know what must never go down.
Step 2: Establish Unified Visibility
Break down silos between:
- IT security
- Network engineering
- Cloud operations
Centralize telemetry across environments.
Step 3: Implement Layered Telecom Network Security
Deploy:
- Network firewalls
- Intrusion detection systems
- Signaling firewalls
- DDoS mitigation
- Endpoint detection
- Cloud workload protection
Defense in depth is non-negotiable.
Step 4: Strengthen Telecom SOC Monitoring
Integrate:
- Threat intelligence feeds
- Automated alert correlation
- Real-time anomaly detection
- Incident playbooks
A SOC without automation will drown in data.
Step 5: Regular Red Team Testing
Simulate:
- Signaling attacks
- Insider misuse
- API abuse
- Ransomware in OSS systems
Test before attackers do.
Common Telecommunications Cyber Threats in 2026
The threat landscape keeps evolving. Expect more:
- AI-driven network reconnaissance
- Automated SIM swap fraud
- Targeted ransomware on 5G cores
- Cloud-native malware
- Supply chain compromise of telecom vendors
Telecom operators must move from reactive defense to predictive detection. Prevention alone is not enough. Early detection and fast containment are the new baseline.
NetWitness for Telecom Cybersecurity
Telecom environments generate enormous volumes of network and cloud telemetry. Fragmented tools create blind spots. NetWitness supports Cybersecurity for Telecom Industry with:
- Unified visibility across network, endpoint, and cloud
- Advanced telecom threat detection powered by analytics
- Real-time packet inspection for deeper telecom network security
- Automated incident response workflows
- Integrated threat intelligence for smarter telecom SOC monitoring
For telecom operators managing millions of subscribers, resilience depends on visibility, speed, and coordinated response. NetWitness helps bring those capabilities together within a unified security operations platform.
The Cost of Ignoring Telecom Cybersecurity
Ignoring Cybersecurity for Telecom Industry leads to:
- Regulatory penalties
- Subscriber churn
- National security scrutiny
- Multi-million-dollar recovery costs
- Permanent brand damage
Telecom is infrastructure. Infrastructure must be resilient by design.
Conclusion
Telecom providers are no longer just connectivity companies. They are guardians of digital identity and national infrastructure. Modern telecom network security requires visibility across core, cloud, and edge. It demands advanced telecom threat detection, continuous telecom SOC monitoring, insider risk controls, and a cloud-first defense strategy.
The operators that win will be those who treat cybersecurity as a foundational capability, not an add-on. Because when telecom security fails, everything connected to it fails too.
Frequently Asked Questions
1. What is telecom cyber security?
Telecom cyber security refers to the protection of telecom networks, subscriber data, signaling systems, and cloud-based infrastructure from cyberattacks, data breaches, and service disruptions.
2. Why is cybersecurity especially critical for the telecom industry?
Telecom providers manage massive volumes of sensitive customer data and operate national infrastructure. A single breach can impact millions of users and critical services.
3. How does 5G increase cybersecurity risks for telecom operators?
5G introduces cloud-native architectures, API-driven communication, network slicing, and distributed edge computing. These expand the attack surface and increase telecom cloud security challenges.
4. What role does a Security Operations Center (SOC) play in telecom cybersecurity?
A SOC monitors network activity 24/7, detects anomalies, correlates alerts across telecom systems, and coordinates rapid incident response to minimize damage.
5. What cybersecurity controls are essential for telecom networks?
Essential controls include network segmentation, encryption, signaling firewalls, real-time threat detection, privileged access monitoring, DDoS protection, cloud workload security, and continuous SOC monitoring.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.