What is network cybersecurity?
Network cybersecurity encompasses tools and strategies that monitor network traffic, control access, detect threats, and respond to incidents affecting network infrastructure. The goal is to protect a computer network and its data from unauthorized access, misuse, or attack.
For years, enterprises relied on on-premises systems, then moved to the cloud with great reluctance. Today, modern enterprises want the best of both worlds. And therefore, their infrastructure now spans on-prem data centers, public cloud environments, SaaS applications, and remote endpoints. And since the infrastructure is becoming increasingly complex, it is creating new challenges for network cybersecurity.
However, Security Operations Center (SOC) teams are still relying on disconnected tools such as standalone firewalls, separate endpoint detection platforms, and independent SIEM systems. Though each tool serves its purpose, in isolation, they are the main cause of delayed investigations and responses.
A unified security platform that connects telemetry, detection, and response in one can help close those gaps.
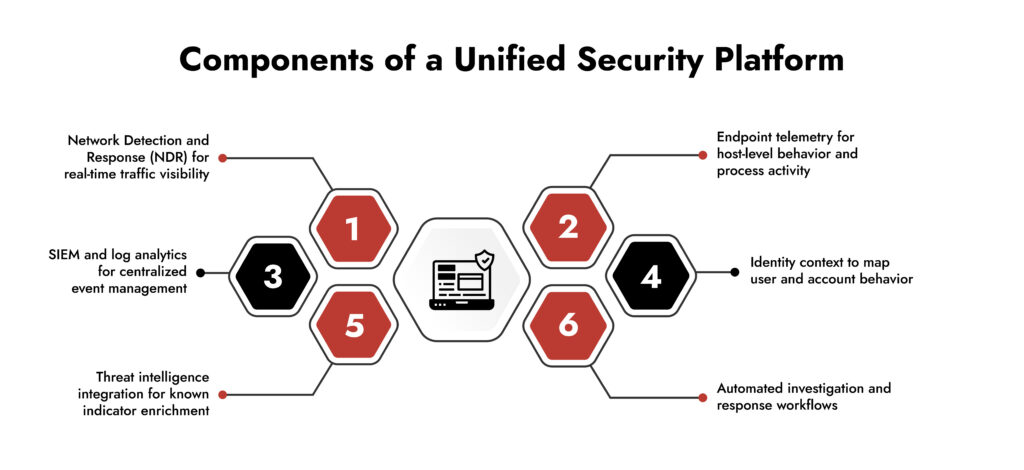
What is a Unified Security Platform?
A unified security platform is one place where telemetry, analytics, and response all live together. Instead of sitting in separate tools, network data, endpoint activity, logs, and identity signals are fed into a single environment where analysts work with them.
The practical difference is straightforward. When a threat needs investigating, the data is already there. No switching between systems, no manually pulling context from three different places before the real work can start. Detection, investigation, and containment happen in one workflow rather than across a fragmented stack that was never designed to work as a whole.
Why Network Cybersecurity Needs Unified Visibility
Every piece of communication between hosts, users, and external systems uses the network. Network often sees activities that don’t even surface on an endpoint. To complicate matters further, according to Google’s Transparency Report, on average, 95% of web traffic is encrypted.
Attackers moving between systems after gaining initial access is another challenge that traditional solutions or even endpoint tools miss. Additionally, organizations working across on-prem environments, cloud providers, and remote access solutions face multiple blind spots if network monitoring does not extend across these platforms.
Signature-based detection had its time, but attackers figured out how to work around it a long time ago. Matching known patterns only catches known threats, and the more dangerous ones tend to look perfectly normal until they do not.
Behavioral analysis and metadata are what fill that gap. Not inspecting every payload but watching how traffic actually moves. Full packet capture and NetFlow analysis are particularly useful here because they surface patterns that endpoint events alone will miss, even when nothing on the host looks obviously wrong.
The cost of not having that visibility shows up in dwell time. Threats that go undetected at the network level tend to stay undetected for a while, and by the time they surface somewhere else, the attacker has usually already done what they came to do.
What are the Core Capabilities of Unified Security Platforms
Unified Security Platforms give a definite edge over disconnected tools by enabling comprehensive visibility across multiple platforms. But there’s more that they should do, let’s look at the core capabilities it should offer:
1. Centralized Telemetry Collection
When SOC agents are asked what slows them down during an investigation, invariably, the answer points to fragmented data. They have to dabble between different tools and work on correlating the data generated.
A unified platform centralizes the data – be it logs, full pack data, NetFlow records, endpoint events, or identity signals. SOC teams can easily access this single source of truth for their investigation. As a result, the investigation is accelerated.
2. Behavioral Threat Detection
Signature-based detection can only detect those threats whose attack pattern is known to the system. But the modern threat landscape hardly works predictably. The unified platform tackles this by applying behavioral analytics across user activity, host behavior, and network traffic patterns.
By baselining normal behavior, these systems efficiently identify deviations that indicate compromise.
3. Cross-Layer Threat Correlation
A single anomalous event rarely triggers an alert. However, the problem starts when the real attacks leave low-confidence signals across different layers of a system. Unified platforms through their centralized database allow correlating cross-layer signals to uncover a high-confidence indicator of compromise. Cross-layer correlation thus minimizes the number of false positives.
4. Faster Investigation and Threat Hunting
The back-and-forth between tools during an investigation is genuinely expensive, not just in time, but in cognitive load. Every context switch is a chance to lose the thread of what happened and when. Having packet data, logs, and endpoint activity accessible in one place means analysts can follow the attacker’s trail without constantly reorienting themselves. It also changes how threat hunting works. Instead of waiting for something to surface, analysts can go looking, working through the data techniques or patterns that automated detection did not flag.
5. Coordinated Incident Response
Confirming a threat is one thing. Containing it across a hybrid environment is another. When those actions have to be carried out manually across separate tools, things get missed, and response slows down. A unified platform handles this through a single workflow. Block the IP, isolate the endpoint, revoke the credentials; these happen together, not sequentially across three different consoles. The difference in response time is real, and so is the reduction in gaps that an attacker could still exploit while containment is in progress.
Unify Security Across Hybrid Environments
- Gain complete visibility across cloud, on-prem, and endpoints.
- Detect threats faster with correlated insights across all layers.
- Reduce complexity with a single, integrated security platform.
- Strengthen your defenses with NetWitness unified security
What are the Benefits of Unified Platform for SOC Teams
The practical impact of unified platforms on SOC operations is:
1. Minimized Alert Fatigue
Any senior analyst who has worked a busy SOC shift knows the real productivity killer is chasing alerts that go nowhere, pulling context from four different systems, writing up an incident with half the data missing.
Correlated, multi-layer alerting addresses the noise problem directly. When an alert requires signals from the network, the endpoint, and the identity layer to fire, the low-context notifications that eat up most of a queue start to thin out. Analysts are not spending the first 40 minutes of every investigation just figuring out whether something is worth investigating.
2. Faster Mean Time to Respond (MTTR)
The speed difference in actual investigations is harder to quantify but very real to anyone who has lived it. Having packet data, logs, and endpoint telemetry in one place means the pivot from “what triggered this?” to “here is what the attacker did” happens in one interface instead of three.
3. Better Threat Context
Context also changes the quality of the decisions being made under pressure. Incomplete containment is a genuine risk when analysts are working from partial information; isolating an endpoint without knowing the attacker has already moved laterally, or blocking a single IP without seeing the broader command-and-control pattern. A full picture of the attacker’s path, built from correlated data across layers, reduces the chance of closing an incident that is not actually closed.
4. Improved Security Posture
The longer-term shift is in posture. Behavioral analytics and structured threat hunting give teams the ability to find things before they escalate. This happens when detection is not limited to known signatures, and rule triggers fire after the fact.
Why Network Detection Remains the Backbone of Unified Security
There is a reason network telemetry keep coming up in post-incident reviews, even when organizations have mature endpoint and log coverage. Endpoints get compromised. Agents get disabled or tampered with. Logs get deleted. These are standard attacker behaviors once someone has enough access to act on them.
The network is harder to manipulate. Full packet capture, in particular, gives you a record of what actually moved across the environment, independent of what the endpoint or the SIEM is reporting. That independence matters a lot when you are trying to reconstruct an incident, and you cannot fully trust the other data sources.
This is clearly evident in lateral movement scenarios, when an attacker moves between internal systems, staging data before exfiltration, or maintains command-and-control communication. In such cases, even though the endpoint activity looks clean, the network footprint gives the attack away.
NDR catches the things that other layers miss, not because it is more sophisticated, but because it is watching a different surface that the attacker cannot easily blind.
That is why network detection does not get retired as environments modernize. It sits underneath everything else as the one layer that consistently provides forensic ground truth and, in a unified platform, that telemetry feeds directly into the correlation and investigation workflows where it is most useful.
Conclusion
The reality is that most organizations are not losing ground because they lack security tools. They are losing ground because those tools do not talk to each other. Cloud, on-premises, remote endpoints — the environment has expanded in every direction, and a stack of point solutions watching different pieces of it was never going to keep up.
What unified platforms actually change is the ability to connect those pieces. Not in a theoretical sense, but in the practical, day-to-day sense of an analyst being able to follow an attacker across the full environment without hitting a dead end because the data lives somewhere else. Network telemetry — packets, flow data — stays at the center of that, because it is the one record that is genuinely difficult to tamper with and consistently tells you what actually happened.
Dwell time does not shrink because teams work harder. It shrinks because the investigation gets faster, the context is already there, and the response does not require coordinating across five different tools manually. That is what a unified platform delivers, and for any team defending a complex environment, that operational difference is what matters.
Why NetWitness?
When a threat hits a hybrid environment, the last thing a SOC team needs is to switch between five different tools trying to figure out what happened and where.
NetWitness pulls network detection, endpoint visibility, SIEM, and threat intelligence into one platform. This is what moves investigations faster, as the data is already connected. With NetWitness Platform, an analyst chasing a suspicious login does not have to pivot to a separate system to check the network traffic or the endpoint activity it is all accessible from one single location.
NetWitness Platform’s coverage spans encrypted traffic, lateral movement, and the gaps that typically fall between disconnected tools. For teams managing complex environments, the difference shows up in how quickly an incident gets contained.
Frequently Asked Questions
1. What are the 4 types of network security in cybersecurity?
The four primary types of network security are:
- Access control
- Firewalls and perimeter security
- Intrusion detection and prevention systems (IDS/IPS)
- Network monitoring and analytics
2. How does a unified security platform strengthen network cybersecurity?
A unified security platform provides a centralized view of network, endpoint, and identity data. This facilitates faster investigation through cross-layer correlation, allowing SOC teams to respond to the incidents more efficiently.
3. What challenges do organizations face without a unified security platform?
Without a unified security platform, SOC teams struggle with disconnected tools and alert fatigue. Investigation timelines are longer as the teams have to manually correlate data. An increase in dwell time directly raises the potential impact of the breach.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.