Is XDR replacing SIEM in modern SOCs?
In modern security architectures, XDR capabilities often extend SIEM visibility by incorporating deeper multi-sensor analytics rather than functioning as an entirely separate technology layer. SIEM is non-negotiable, especially when compliance and long-term retention are required.
As a part of the cybersecurity team, you must have often heard, “Do we need SIEM, XDR, or both?” A few years ago, the default answer would have been SIEM. But now, XDR makes a compelling case about speed, automation, and reducing analyst burnout.
As detection architectures evolve, many SOC teams are now evaluating how traditional SIEM capabilities align with newer cross-domain detection approaches often described as XDR.
Let’s cut through the noise and find out!
Why the SIEM vs XDR Conversation Matters Now
Traditional SIEM (security information and event management) platforms were designed for centralized infrastructure and clear network perimeters. SIEM cybersecurity solutions were multitasking between aggregating logs, enabling compliance reporting, and supporting investigations.
But today’s attack surface looks different:
- Hybrid cloud and SaaS sprawl
- Remote endpoints everywhere
- Identity-based attacks
- API-driven workloads
- Faster attacker dwell time
Modern security platforms increasingly combine log-centric visibility with deep telemetry analytics. As a result, the conversation is shifting from tool replacement to architectural expansion.
According to the IBM Cost of a Data Breach Report 2025, the average time to identify and contain a breach is 241 days. That number explains why many SOC cybersecurity teams are reassessing their detection models.
What Is the Difference Between SIEM and XDR?
The difference in the SIEM vs XDR comparison comes down to primary design intent. They were simply designed to solve different problems. Understanding that design intent helps security leaders avoid forcing one tool to do the job it was never meant to handle.
In practice, the distinction between SIEM and XDR is becoming architectural rather than categorical. Many modern platforms integrate multiple telemetry sensors, analytics engines, and log management capabilities within a unified detection framework.
SIEM (Security Information and Event Management)
A SIEM solution centralizes logs across infrastructure, applications, identity systems, and security tools.
Core strengths:
- Log aggregation at scale
- Rule-based correlation
- Compliance reporting
- Long-term retention
- Forensic search
Most mature enterprises still rely on SIEM solutions for compliance and meticulous record-keeping.
But traditional SIEM security requires:
- Ongoing rule tuning
- Careful log normalization
- Dedicated engineering resources
To know more about SIEM, its benefits and limitations, and how it can elevate threat detection and response, read this blog.
XDR (Extended Detection and Response)
XDR architectures typically prioritize high-fidelity telemetry analytics across multiple proprietary sensors, while many platforms also incorporate log ingestion and retention capabilities traditionally associated with SIEM.
Core strengths:
- Endpoint, network, identity, and cloud telemetry integration
- Behavioral analytics
- Built-in correlation
- Automated investigation workflows
SIEM centralizes logs and correlates data to support threat detection. Whereas XDR focuses on security-relevant telemetry and attempts to detect higher-fidelity alerts. During investigations, SIEM requires manual stitching, and XDR tries to pre-correlate activity chains.
How Detection Approaches Differ Operationally
When comparing the detection approach, it depends on what kind of detection challenge you are trying to solve.
Where SIEM Still Performs Well With
- Complex custom correlation use cases
- Highly regulated environments
- Long-tail forensic investigations
- Broad visibility across business systems
Many advanced SOC cybersecurity teams still build sophisticated detection logic within their SIEM security stack. However, detection performance depends heavily on rule maturity and tuning quality. The threat landscape ranges from identity misuse, phishing, to credential abuse, attack types that can be detected by behavioral analytics rather than static correlation alone.
Where XDR Often Has the Edge With
- Early-stage behavioral anomalies
- Lateral movement detection
- Endpoint-driven investigations
- Reducing false positives
As XDR platforms are purpose-built for detection, they often find suspicious activity faster without relying solely on predefined rules.
Wondering why XDR is getting so much attention?
So, in the SIEM vs XDR question for threat detection specifically:
- SIEM offers breadth and flexibility.
- XDR often offers speed and clarity.
They serve different operational priorities, hence neither is superior to the other.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.

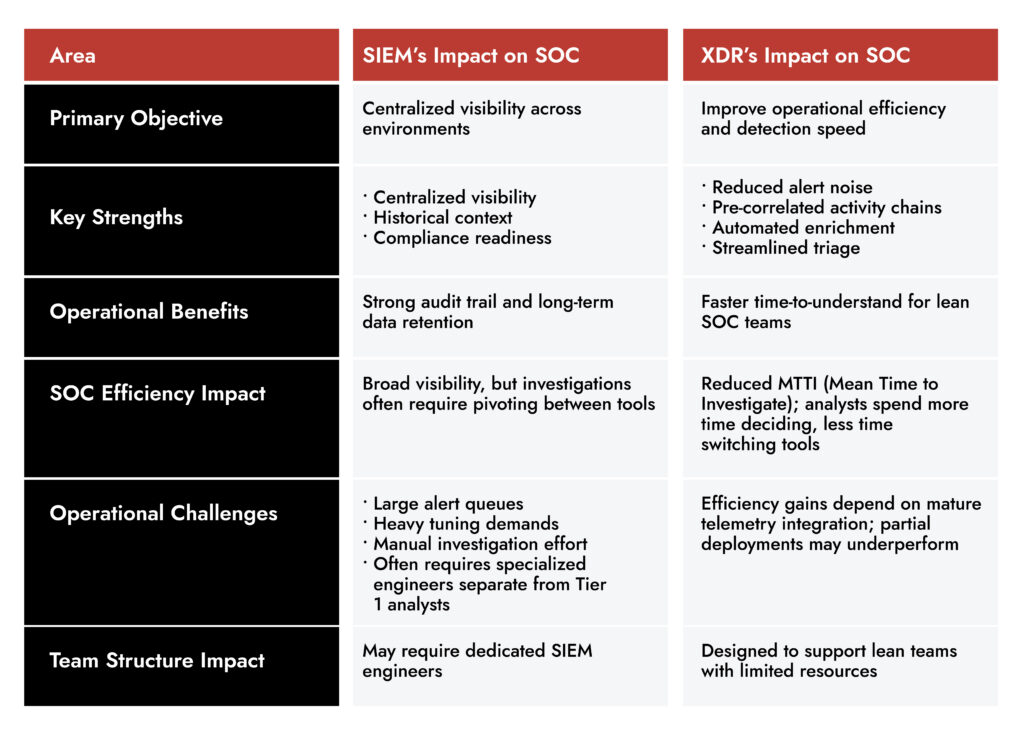
How Do SIEM and XDR Impact SOC Efficiency?
If you ask most SOC leaders what their biggest challenge is, most of them would say analyst burnout.
The SIEM vs XDR comparison becomes very real when you measure:
- Alert volume
- Investigation time
- Escalation quality
- Analyst workload
According to Gartner’s research on SOC modernization, organizations increasingly prioritize automation and integrated detection workflows to improve analyst productivity.
Can SIEM and XDR Work Together Effectively?
The SIEM vs XDR discussion rarely ends with one solution replacing the other. In many modern platforms, SIEM and XDR capabilities are no longer deployed as separate tools but as integrated functions within a unified security operations architecture:
- SIEM as the centralized log and compliance backbone
- XDR as the active detection and response layer
This model preserves:
- Audit and regulatory requirements
- Long-term retention
- Broad business visibility
While also improving:
- Detection precision
- Investigation speed
- Analyst workload balance
The value of hybrid models depends on how well the platforms are integrated. If SIEM and XDR run separately without coordination, teams often end up with duplicate alerts and the same investigation happening in two different consoles.
The strongest integration setup is where each platform has a clearly defined role, and both platforms work towards a single workflow.
What Should Enterprises Consider When Choosing Between SIEM and XDR?
The SIEM vs XDR decision should start with operational challenges, and not with feature comparisons.
Here are the questions that matter:
1. What Is Driving the Decision?
- Compliance requirements? → SIEM likely mandatory
- Detection gaps? → XDR may deliver faster improvement
- Both? → Hybrid strategy
2. How Mature Is the SOC?
- Mature engineering team? SIEM tuning may be sustainable
- Lean team? XDR automation may provide immediate relief
3. What Is the Data Strategy?
A security information and event management solution excels at long-term log retention. If regulatory retention is non-negotiable, SIEM remains foundational.
4. What Does Attack Surface Look Like?
Highly distributed endpoints and identity-driven environments often benefit from XDR’s cross-domain visibility.
5. Is Tool Sprawl Already a Problem?
If analysts are pivoting across five consoles daily, adding technology without integration may worsen fatigue.
In most enterprise cases, the SIEM vs XDR outcome isn’t binary. It’s architectural.
SIEM + XDR Use Case
Assume there is a financial institution called CashIN. Audit readiness is a part of daily operations. Log retention requirements exceed one year. Compliance reporting is not negotiable. Hence, SIEM is not optional.
However, the SOC has more challenges. The detection workflows are slower than they should be. Tier 1 analysts spend a significant portion of their shift validating alerts that are correlated but lack enough context to make quick decisions. Escalations happen without clarity building up friction over a period.
An XDR here will not replace the SIEM. Instead, it will shift frontline detection to a more behavior-driven engine. The SIEM will continue serving as the authoritative data repository. The results will be measurable:
- Fewer escalations without context
- Faster containment on endpoint-driven incidents
- Reduced Tier 1 fatigue
Practical Takeaways for Security Leaders
When evaluating SIEM vs XDR, the security leaders should bear the following in mind:
- SIEM remains foundational for compliance, retention, and enterprise-wide visibility.
- XDR strengthens detection, precision, and investigation speed.
- SOC cybersecurity efficiency improves when automation reduces manual stitching.
- Replacement strategies often create risk; integration strategies tend to create balance.
- The right architecture aligns to your team’s constraints, not market trends.
The organizations seeing the strongest results aren’t chasing acronyms. They’re aligning SIEM security capabilities and modern threat detection and response platforms to measurable SOC outcomes. The SIEM vs XDR decision ultimately isn’t about which is more advanced. It’s about which operational gaps you’re solving — and whether your architecture reflects how attackers actually move today.
Frequently Asked Questions
1. Is XDR replacing SIEM in modern SOCs?
In most organizations, XDR supplements SIEM rather than replacing it. SIEM is non-negotiable, especially when compliance and long-term retention are required.
2. How does SIEM vs XDR affect compliance requirements?
SIEM is built for log retention, audit trails, and reporting that are critical for compliance. XDR focuses on detection and response efficiency, not long-term regulatory record-keeping.
For many enterprises, SIEM supports compliance, while XDR strengthens operational detection.
3. Does XDR reduce alert fatigue compared to traditional SIEM solutions?
Often, yes, but it depends on implementation.
Traditional SIEM solutions rely heavily on rule-based alerts, which can create high volumes if not carefully tuned. XDR platforms are designed to correlate security telemetry before generating alerts, which typically improves alert quality.
That said, XDR only reduces fatigue when detection roles are clearly defined.
Choose the Right SIEM with Confidence