What are modern network attacks and why are they harder to detect?
Modern attacks are stealthy, using stolen or reused credentials to access networks and operate via legitimate tools within encrypted traffic. Attackers move laterally to expand control before launching data theft, ransomware, or DoS attacks. Traditional, perimeter-focused and signature-based detection is ineffective against such internal (east-west) threats. Organizations must adopt real-time, behavior-based monitoring that correlates user, network, and encrypted activity to identify anomalies, rather than relying on static rules or known attack patterns.
Introduction
Most network attacks today don’t look like attacks. There’s no noisy exploit chain. No obvious malware beacon. No sudden surge in traffic that triggers alerts. Instead, adversaries gain access using credentials obtained through social engineering, credential theft, or prior breaches. They then navigate laterally using normal protocols and operate within encrypted sessions that blend into everyday network activity. That adjustment alters the detection formula.
Contemporary network assaults are designed to take advantage of intricacy. Hybrid systems, decentralized identities, secure communications, and disjointed monitoring solutions form an ideal disguise. The issue isn’t that security teams lack comprehension of threats. The signal is concealed within genuine activity This isn’t about awareness. It’s about visibility at depth.
The Numbers Behind Modern Network Attacks
- Lateral movement remains present in the majority of advanced intrusions, according to CISA and multiple 2024 incident advisories.
Modern network attacks are not just more frequent. They last longer, cost more, and exploit identity misuse more than perimeter weaknesses.
How Modern Network Attacks Actually Unfold
Modern network attacks follow a disciplined progression. They’re methodical, patient, and deliberate.
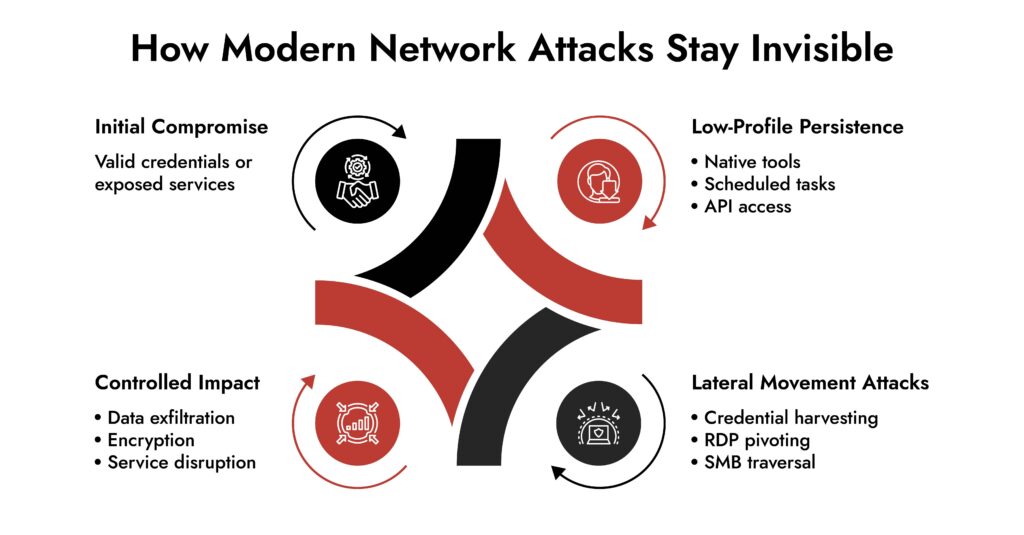
Most campaigns move through four stages:
- Initial Access – Phishing remains common, but stolen credentials, exposed services, and third-party compromise are increasingly dominant. Access brokers lower the barrier to entry.
- Persistence Without Noise – Attackers avoid heavy malware. They leverage scheduled tasks, remote management tools, cloud APIs, and native system utilities.
- Lateral Movement Attacks – This is where real damage begins. Adversaries pivot using RDP, SMB, Kerberos, or token abuse. East-west traffic becomes the operational channel.
- Impact or Exfiltration – Data theft, ransomware deployment, or operational disruption follows once control stabilizes.
The critical observation: modern network attacks don’t rely on zero-days in every case. They rely on architectural familiarity. They exploit trust relationships and monitor gaps. That makes them harder to disrupt.
Why Modern Network Attacks are Harder to Detect
Modern network attacks hide inside expected behavior. Three structural factors explain why detection becomes harder each year.
1. Encryption Masks Intent
Over 90% of web traffic now travels via TLS. Command-and-control traffic, data staging, and internal pivoting often sit inside encrypted channels. Traditional network intrusion detection inspects patterns. It struggles when payload visibility disappears. Without behavioral context, encrypted sessions look routine.
2. Identity Has Become the Attack Surface
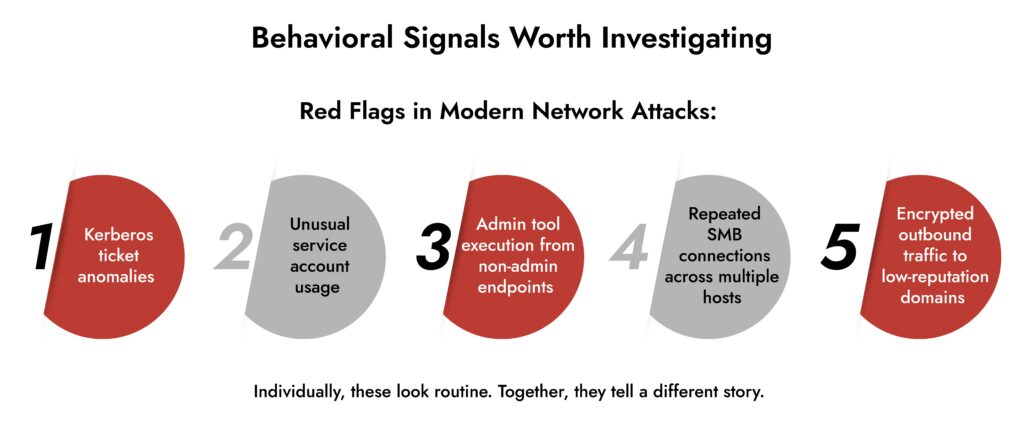
Attackers increasingly weaponize identity:
- Credential reuse
- Kerberos abuse
- Token manipulation
- Privileged account compromise
When adversaries authenticate properly, alerts decrease. Logging systems show successful logins, not intrusions. Detecting network attacks in this environment demands identity-behavior correlation, not simple rule matching.
3. East-West Traffic is Under-Scrutinized
Perimeter defenses matured. Internal monitoring often lagged.
Once inside, attackers pivot across file servers, application tiers, and domain controllers. Lateral movement attacks generate subtle patterns:
- Slightly elevated authentication attempts
- Administrative tools executed from atypical hosts
- Gradual data aggregation
Without continuous network analysis tools inspecting internal flows, those patterns remain invisible.
Why Signature-Based Detection Falls Short
Signature-based detection worked when malware reused recognizable code. Modern network attacks don’t depend on static indicators. They rely on:
- Living-off-the-land techniques
- Short command intervals
- Low-and-slow data transfers
- Legitimate administrative binaries
If your network intrusion detection depends on known patterns, it will detect yesterday’s threats. IBM’s 2024 data still shows extended breach lifecycles. That’s not a tooling shortage. It’s a context shortage.
Detection requires reconstruction. Analysts need to replay sessions, correlate identity shifts, and examine behavioral anomalies across time. That’s forensic visibility, not alert fatigue.
Rolling the Dice: Ransomware in the Gaming Industry
Discover how ransomware attacks hit gaming companies, how attackers moved laterally, and why network visibility is key. Learn real-world lessons and strategies to detect, respond, and protect critical systems.

The Growing Risk of Lateral Movement Attacks
Once adversaries establish footholds, lateral movement attacks become the force multiplier. They don’t rush. They map. They identify:
- Domain trust relationships
- High-value service accounts
- Backup servers
- Cloud control planes
Each pivot increases enterprise network security risks exponentially. Verizon’s findings reinforce this pattern: attackers spend significant time expanding internal control before triggering impact. By the time ransomware encrypts systems, the groundwork has already been laid.
Stopping lateral movement attacks early disrupts the entire campaign lifecycle. That requires inspection of internal traffic with context, not perimeter-only oversight.
Detecting Network Attacks Requires Depth, Not Volume
More data doesn’t solve the problem. Correlation does. Detecting network attacks effectively requires visibility across:
- Full packet data
- NetFlow and telemetry
- Endpoint process behavior
- Identity events
- Cloud access patterns
Network threat detection solutions must unify this data, not scatter it. When analysts can reconstruct sessions, validate anomalies, and trace lateral movement attacks step by step, decision-making improves. False positives decline. Response accelerates. Without this depth, teams operate reactively, not strategically.
The Role of Network Detection and Response
Network Detection and Response (NDR) addresses this gap directly. NDR platforms analyze traffic behavior, reconstruct sessions, and surface anomalies that evade static signatures. They focus on:
- Continuous inspection of east-west traffic
- Behavioral baselining
- Automated investigation support
- Forensic-level evidence retention
This approach aligns with NIST guidance on incident response maturity and continuous monitoring. Effective network cyber security now depends on visibility into behavior, not just perimeter events.
Where NetWitness Aligns
NetWitness focuses on forensic depth within Network Detection and Response. Its capabilities emphasize:
- Full packet capture and replay
- Deep network analysis tools for session reconstruction
- Correlation across network, endpoint, and cloud telemetry
- Investigation workflows designed to reduce uncertainty
In environments where modern network attacks operate inside encrypted sessions and lateral pivots, that level of visibility enables teams to confirm compromise rather than speculate. It supports informed response, not reactive containment.
Strengthening Defenses Against Modern Network Attacks
Modern network attacks will continue to evolve. Defense must evolve faster. Focus on structural improvements:
- Elevate East-West Monitoring – Internal traffic deserves equal scrutiny.
- Correlate Identity and Network Behavior – Privileged misuse often precedes impact.
- Retain Forensic Evidence – Packet-level reconstruction supports both containment and compliance.
- Continuously Validate Detection Gaps – Simulate adversary techniques. Measure response friction.
- Integrate Network Threat Detection Solutions with IR Processes – Detection without coordinated response extends dwell time.
Network cyber security strategy must shift from reactive alerting to proactive behavioral analysis. That’s not theoretical. It’s operational reality.
Conclusion
Modern network attacks succeed because they exploit trust, encryption, and operational complexity. They don’t need loud exploits. They need time and visibility gaps. Detecting network attacks now requires behavioral depth, integrated telemetry, and forensic clarity. Lateral movement attacks remain the decisive phase. Stop them early, and the broader campaign collapses.
The question is no longer whether your tools generate alerts. It’s whether they provide enough context to act with confidence. Reassess your visibility. Close internal blind spots. Strengthen your network threat detection solutions before modern network attacks exploit the next gap.
Frequently Asked Questions
1. What are network attacks?
Network assaults are intentional efforts to obtain unauthorized access, interrupt operations, or retrieve data from systems. Contemporary network assaults often utilize valid credentials and internal maneuvering instead of conspicuous malware.
2. What can protect your network from DoS attacks?
Strong network cyber security controls help mitigate DoS attacks. Traffic filtering, rate limiting, DDoS mitigation services, and continuous monitoring through network threat detection solutions reduce disruption risk.
3. What are the types of network attacks?
Common network attacks include:
- Denial-of-Service (DoS) and Distributed DoS
- Man-in-the-Middle attacks
- Lateral movement attacks
- Credential-based intrusions
- Data exfiltration campaigns
Modern network attacks often combine several techniques.
4. What network attack seeks to create a DoS for clients?
A Distributed Denial-of-Service (DDoS) is when multiple sources flood a system with so much traffic that it overwhelms the infrastructure, causing legitimate users to be unable to access services.
5. How to detect a DDoS attack on your network?
To identify network attacks such as DDoS requires tracking traffic baselines. You will notice abnormal request rates, sudden increases in bandwidth utilization, and distributed sources of IP addresses. Using network analysis tools, as well as a network intrusion detection system will help quickly identify aberrations in traffic and confirm DDoS activity.
6. Why are modern network attacks harder to detect?
Modern network attacks blend into legitimate traffic, use encrypted channels, and rely on lateral movement attacks. Detecting network attacks now requires behavioral analytics and integrated network threat detection solutions rather than signature-only controls.
FIN13: Inside a Fintech Cyber Attack
FIN13 is one of today’s most disruptive threat groups targeting fintech organizations with precision and persistence. This whitepaper breaks down their full attack chain—from reconnaissance and credential theft to lateral movement, data exfiltration, and evasion techniques. Gain insights into their TTPs, discover detection opportunities across the kill chain, and learn how NetWitness empowers faster response and mitigation.