What features to look for in network visibility software?
- Consolidate Visibility Through Integrated NDR and Monitoring Platforms
- Use Metadata and Behavior to Monitor Encrypted Traffic
- Extend Visibility to Cloud, SaaS, and Remote Environments
- Automate Alert Triage and Investigation Workflows.
- Foster Collaboration and Standardized Processes
- Continuously Audit and Refine Your Visibility Strategy
Introduction
The term “network visibility” refers to being able to understand all activities taking place throughout your digital landscape. Users, devices, and their interactions with applications and data all comprise this digital operations environment; without proper context about these elements, determining the cause of performance problems and finding and preventing threats becomes an exercise in guesswork.
As organizations deploy enterprise-wide cloud infrastructure across multiple cloud platforms, obtaining and retaining visibility into their networks will be one of the most challenging, yet most important, aspects of cybersecurity moving forward.
Understanding network visibility in the proper context means understanding why network visibility is valuable, why network/enterprise visibility is difficult to achieve, and how to develop more effective strategies and tools for dealing with these challenges.
Why Network Visibility Matter?
Visibility tools and solutions for networks provide more than just security monitoring; they help improve compliance with regulations, improve network performance and provide many other benefits.
The first area of focus is Security. Visibility into all the activities on the network allows the security team to quickly detect potential threats, track lateral movement through compromised systems, and take action before the attacker has had sufficient time to establish long-term access.
The second area of focus is Performance. By determining which applications and endpoints consume the most bandwidth, all necessary resources can be taken into account when identifying performance bottlenecks.
Compliance is also one of the areas of focus for visibility tools because many regulatory requirements, for example, PCI-DSS, HIPAA, etc., require that a complete record of an organization’s performance in maintaining the security and protection of sensitive data be maintained.
Troubleshooting, whether it be the result of malicious activity, a misconfigured router, or some other reason. Knowing what is happening on the entire network allows an organization to quickly identify the root cause of signals of business interruption or reduced performance.
Lastly, Business Continuity. Network visibility allows a business to maintain consistent and reliable access to essential applications, even during emergencies, because of the ongoing view of network functionality.
In conclusion, network security visibility moves an organization from reactive defense to proactive control.
The Core Challenges of Network Visibility
1. Encrypted and High-Volume Traffic:
Encryption now secures the majority of network communications, a win for privacy, but a headache for defenders. When data is encrypted, traditional inspection tools can’t be seen inside the traffic. Full-packet capture helps retain data for analysis but doesn’t decrypt it.
The best approach is to focus on encrypted traffic analytics: examining flow metadata (packet size, handshake patterns, session duration) and behavioral anomalies to detect threats without breaking encryption.
High-volume traffic adds another layer. Monitoring terabytes of data in real time can overwhelm infrastructure and analysts alike. Scalable network visibility tools that prioritize critical data and automated analysis are essential to maintain insight at an enterprise scale.
This is where solutions like NetWitness NDR provide a deeper advantage. Instead of relying solely on decrypted data, NetWitness analyzes metadata extracted from full packet capture and enriches it with context from endpoints, logs, and threat intelligence. This allows detection of malicious behavior even in encrypted or partially visible traffic.
2. Remote Access and Cloud Visibility Gaps:
As remote work and multi-cloud architecture became permanent, visibility fragmented. Traffic flows no longer stay within a traditional perimeter. Data now moves between cloud services, SaaS platforms, and unmanaged devices – many of which traditional network visibility solutions were never designed to monitor.
The result is blind spots that attackers exploit to hide lateral movement or exfiltrate data undetected. Achieving full enterprise network visibility now requires unified monitoring across on-prem, virtual, and cloud workloads.
3. Tool Fragmentation and Limited Integration:
Many enterprises rely on multiple monitoring tools – firewall logs here, endpoint telemetry there, cloud analytics elsewhere. This fragmentation makes it difficult to form a complete picture. Analysts waste time correlating data across disconnected systems, often missing early warning signs in the noise.
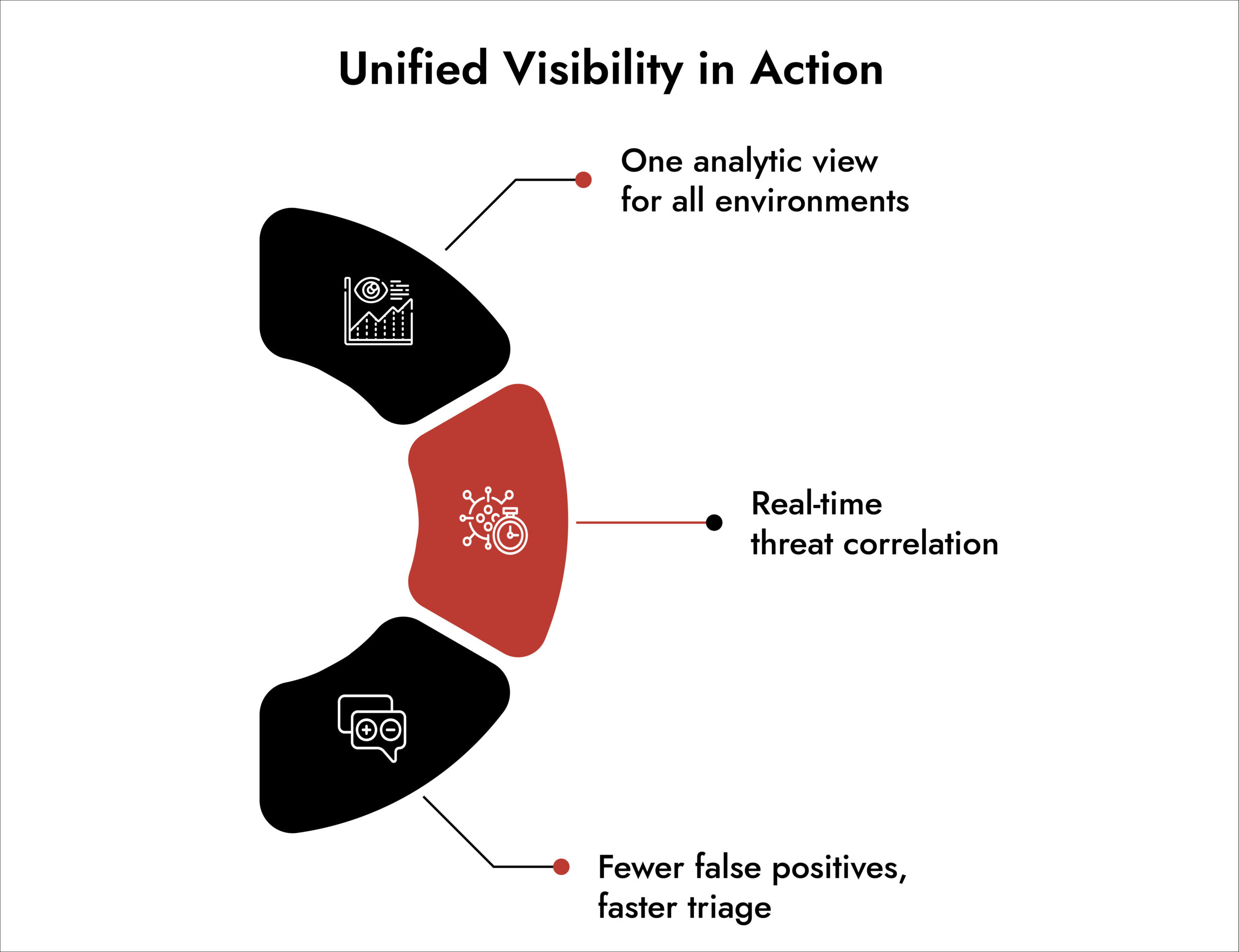
The fix lies in integrated visibility, where NDR, SIEM, and EDR telemetry converge into a single analytic layer. When data is centralized and correlated automatically, network threat visibility becomes actionable rather than overwhelming.
4. Network Complexity and Emerging Technologies:
Modern networks constantly expand through IoT devices, APIs, and virtualized services. Each addition increases complexity and introduces potential blind spots.
Technologies like SDN and NFV have improved flexibility but created challenges because traffic paths change dynamically.
Without adaptive monitoring, teams end up looking at yesterday’s network map while attackers exploit today’s.
5. Operational Overload and Analyst Fatigue:
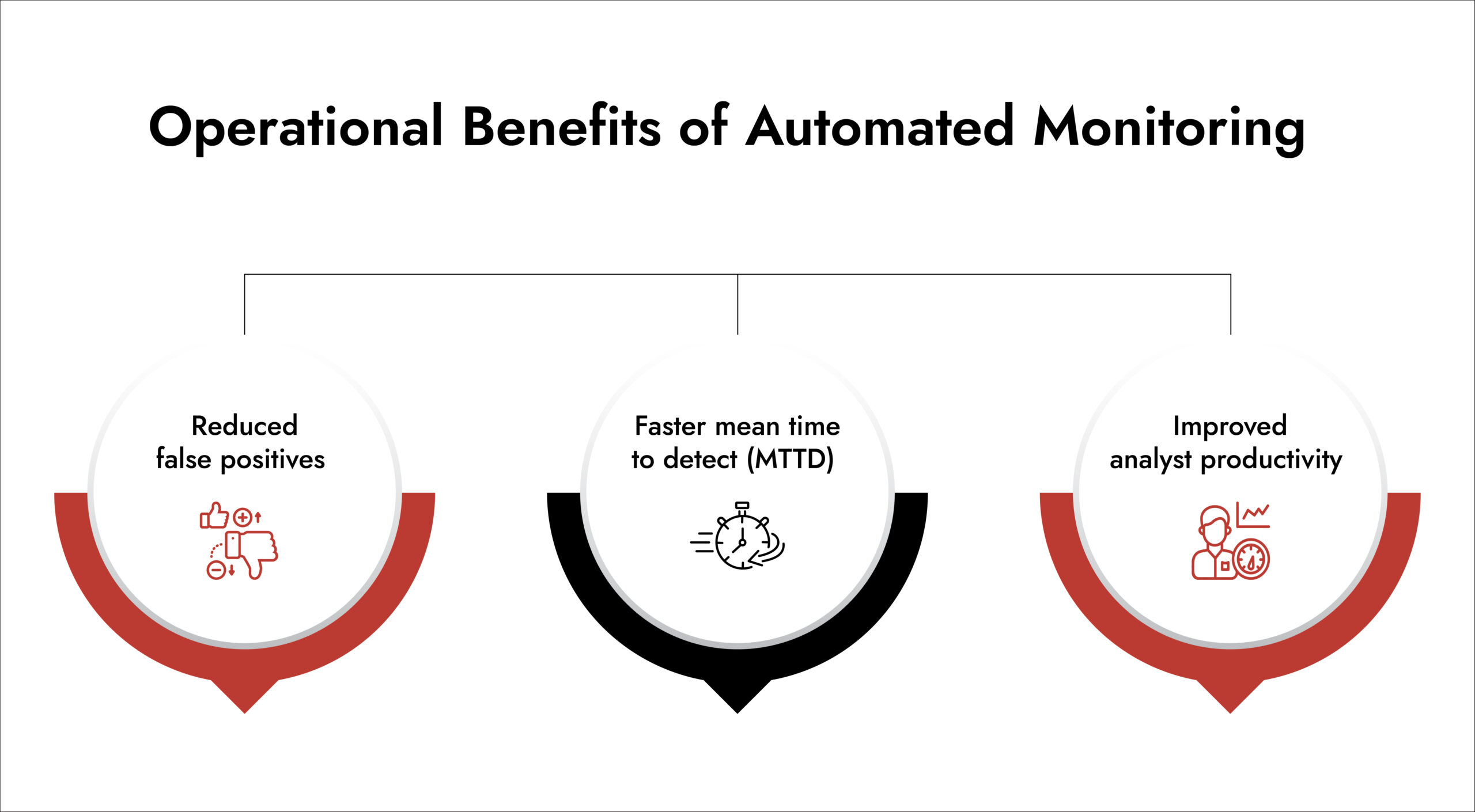
Even with the right tools, many SOCs struggle with overloading. Thousands of alerts, repetitive investigations, and limited automation drain analyst focus. Visibility without prioritization becomes noisy.
Reducing this overload requires automation – intelligent correlation, context enrichment, and workflows that separate the meaning from the trivial.
Top Features to Look for in Network Visibility Software
1. Consolidate Visibility Through Integrated NDR and Monitoring Platforms:
Fragmented tools create fragmented insight. The first step is consolidation – deploying NDR tools that capture network data, analyze behavior, and integrate directly with SIEM and EDR. This unified approach delivers deeper network security visibility and reduces manual effort.
2. Use Metadata and Behavior to Monitor Encrypted Traffic:
Rather than decrypting traffic, analyze its metadata. Metrics like session length and TLS fingerprinting can reveal anomalies consistent with command-and-control or exfiltration.
Pair behavioral analytics with historical baselines to detect suspicious trends without violating privacy.
3. Extend Visibility to Cloud, SaaS, and Remote Environments:
Comprehensive network monitoring must now include cloud-native workloads and remote endpoint visibility. Choose visibility tools that support cloud traffic mirroring, virtual taps, and API-based telemetry collection.
By mapping traffic patterns across all environments, teams eliminate blind spots and ensure uniform security controls regardless of location.
4. Automate Alert Triage and Investigation Workflows:
The sheer volume of alerts is one of the most cited pain points. Automation helps analysts focus on what matters most.
AI-assisted correlation groups related events and contextualizes them with user, endpoint, and network data. Dashboards should highlight the few high-impact alerts instead of the noise.
5. Foster Collaboration and Standardized Processes:
Visibility gaps often stem from human silos. Shared playbooks and communication channels between IT, network, and security teams ensure consistent investigation and escalation.
6. Continuously Audit and Refine Your Visibility Strategy:
Networks evolve daily; your visibility approach must be too. Conduct regular audits to identify coverage gaps, outdated detection rules, and under-monitored assets. Integrate new cyber threat intelligence feeds and adapt monitoring baselines as business operations change.
Continuous improvement keeps visibility aligned with your actual risk surface, not last year’s assumptions.
Strengthen Network Visibility with NetWitness® Network Traffic Security Assessment
-Uncover hidden threats through deep packet inspection and analytics.
-Identify vulnerabilities and blind spots before they’re exploited.
-Enhance detection and response with NDR-driven intelligence.
How NetWitness Delivers Complete Network Visibility
Network visibility is about seeing what truly matters and understanding it in context. NetWitness Network Detection and Response (NDR) delivers that depth by analyzing every packet, flow, and log across physical, virtual, and cloud environments.
NetWitness NDR at its core provides:
- Full Packet Capture and Metadata Analytics: NetWitness records every packet that is sent or received and extracts a wealth of metadata that provides an efficient means of quickly analyzing the network. Analysts are able to drill down into the full session data whenever necessary or jump instantly to the specific packets being referenced by versatile metadata.
- Behavioral Analytics and Machine Learning: With advanced analytics to detect anomalies, NetWitness applies machine learning algorithms to provide insight into potential threats that other legacy signature-based technology has likely missed (for example, during the analysis of encrypted traffic). The result is that security teams can gain visibility into malicious behaviours associated with threat actors without relying only on the decrypted network traffic.
- Threat Intelligence Correlation: Threat Intelligence and contextual indicators enrich network data; consequently, analysts have better access to identify lateral movement, data exfiltration, and command-and-control behaviours much sooner when correlating established contextual threats to that of the network traffic itself.
- End-to-End Integration with SIEM and SOAR: Repository of Security Data Management (RSDM: SIEM, SOAR, and other security repositories) that are based on a common data model and investigation interface. Analysts benefit from the ability to detect, correlate and automate responses from one single source of intelligence. The common data model also provides required support to integrate SIEM and SOAR tools into a unified work environment (as opposed to separate systems).
- Hybrid and Multi-Cloud Visibility: NetWitness technology provides consistent visibility across all sources of network traffic whether the source of the traffic was from customer-inflicted or cyber-attack. Lightweight sensors are placed and operate within the cloud environment. NetWitness’s scalable and high-performance architecture is designed to scale easily for distributed environments.
This single platform effectively converts from disparate to actionable intelligence, thereby allowing analysts to quickly detect emerging threats and respond to them effectively.
Conclusion
True network visibility goes beyond seeing packets, it’s about understanding what they mean in context. With its unified NDR platform, NetWitness helps security teams connect network data to broader threat intelligence, accelerating detection and response across every environment. Because in modern cybersecurity, you can’t defend what you can’t see.
Explore how NetWitness helps security teams gain clarity across the network, accelerate investigations, and strengthen defense against evolving threats.
Frequently Asked Questions
1. What is network visibility in cybersecurity?
Network visibility is the ability to monitor, analyze, and understand all traffic across your environment – on-prem, cloud, or remote. It helps detect threats and ensure compliance.
2. What features should I look for in network visibility software?
Look for NDR software and tools that offer full-session capture, metadata enrichment, behavioral analytics, and SIEM/EDR integration. These ensure depth and context in network visibility solutions.
3. What are the major challenges to attain network visibility?
The common challenges include encrypted traffic, remote access, tool fragmentation, high data volume, and analyst overload.
4. What are the best tools for network monitoring and security?
Effective network visibility tools combine traffic capture, analytics, and automation. Solutions such as NetWitness unify these capabilities toward end-to-end visibility.
5. Can network visibility solutions help prevent cyberattacks?
Yes. Network visibility solutions prevent breaches before they blow out of proportion by offering early detection of anomalies, correlating data, and enabling fast response.






