How Phishing Has Evolved
- Phishing remains one of the most common methods for executing cyber attacks. The 2024 Verizon Data Breach Investigations Report indicates that it remains a significant factor in breaches.
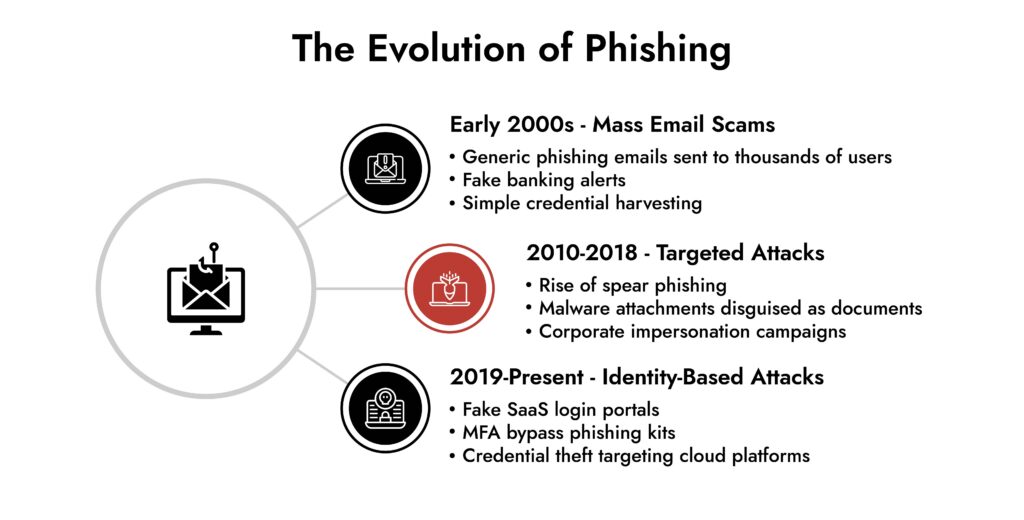
- Initially, the technique employed was bulk spam emails, but currently the prevalent methods are spear phishing, identity impersonation, and SaaS login cloning.
- Today’s hackers are trying to acquire credentials, authentication tokens, and privileged accounts rather than just trying to acquire personal data.
- It is very important that the organization have visibility into the identity systems, the network activity, and the endpoint activity if they want to be successful at implementing anti-phishing strategies.
- It is very important to know what phishing looks like today compared to years ago so you can spot a breach fast.
Introduction
Most security professionals remember the early phishing emails. They were obvious. Poor grammar, strange links, and fake bank alerts that looked nothing like the real thing. Today’s phishing campaigns are very different.
Modern phishing attacks often look like normal business communication. The email may come from a vendor account that was already compromised. The login page may be an exact copy of a legitimate SaaS portal. The message may even reference a real project or internal process.
To comprehend what phishing entails in a contemporary business setting, it is beneficial to examine how the danger has developed.
Attackers have discovered a straightforward truth: taking a user’s identity is frequently simpler than infiltrating a secure network. After a legitimate account is breached, the intruder might possess all the necessary information. This is why phishing continues to be one of the most dependable gateways for significant security breaches.
What is Phishing in Cybersecurity?
Phishing is basically social engineering in which the attacker fools the victim into giving away their information or acting in such a way as to allow the attacker to access their information.
To most people phishing is a means of acquiring someone’s credentials illegally. A smaller subset of phishing hacks function to deliver and distribute viruses and malware to a business for later exploitation.
Phishing schemes all begin with a victim that has received a message that they think is legitimate. For example, a password reset email, document share email, or a message telling someone that they need help as soon as possible from the sender.
The next step is for the attacker to acquire the credentials from the victim or make them go to a location (website) that is injurious to them and their business. The main point to understand with phishing is that phishing attacks are dependent on the victim having trust in the hacker rather than technology.
How Does a Phishing Attack Work?
Security personnel often want to know how does a phishing attack work in the real world. Generally speaking, there is a specific pattern followed in the majority of the attacks.
1. Reconnaissance – The attacker tries to know more about the company. This includes the company profile, the vendors they use, and the employees working in the company.
2. Message Creation – The attacker creates a message that seems legitimate. It could be a fake login message, an invoice notification, or a document notification.
3. Delivery – The attacker sends the message through email, messaging apps, or text messages. Email is the most commonly used method.
4. Credential Capture – The victim clicks on the message and enters the credentials on the fake login page.
5. Account Access – The attacker logs in and starts exploring the system.
At this stage, the phishing email is not the real threat. The threat is the compromised account.
Types of Phishing Attacks Security Teams See Today
Security managers frequently concentrate on malware attacks, but some attacks begin with any of several types of phishing attacks.
Spear Phishing: In contrast to typical phishing schemes, spear phishing focuses on particular individuals. The assailant focuses on a specific individual and then creates an email that seems particularly pertinent to that person. Finance, business, and IT are common targets.
Corporate Email Fraud: Business Email Compromise, or BEC, occurs when an assailant impersonates a trusted individual within the organization. The assailant might request a money transfer, change payment information for vendors, or seek confidential information. The FBI Internet Crime Complaint Center indicates that BEC attacks result in billions of dollars in losses.
Smishing: SMS phishing messages are referred to as smishing. These messages frequently assert that they are notifications about deliveries or account updates.
OAuth and SaaS Phishing: Attackers are increasingly replicating login pages for cloud services like Microsoft 365 or Google Workspace. This kind of phishing aims to obtain authentication credentials that grant access to corporate systems. These instances illustrate how phishing and spear phishing attempts have evolved to fit contemporary business frameworks.
Why Modern Phishing Attacks are Harder to Detect
Many organizations invest heavily in email security tools and employee awareness programs. Yet phishing continues to succeed. The reason lies in advanced phishing techniques.
Attackers now rely on:
- cloned SaaS login pages that look identical to the real platform
- compromised vendor accounts used to send legitimate-looking messages
- phishing kits designed to bypass multi-factor authentication
- targeted messages based on real company activity
In many cases, the attacker does not need to exploit a technical vulnerability. They simply need a user to trust the message. Once credentials are stolen, the attacker logs in using valid authentication. From the system’s perspective, it looks like a normal user session. This is why phishing detection increasingly relies on behavioral analysis rather than simple email filtering.
Rolling the Dice: Ransomware in the Gaming Industry
Discover how ransomware attacks hit gaming companies, how attackers moved laterally, and why network visibility is key. Learn real-world lessons and strategies to detect, respond, and protect critical systems.

Phishing Prevention Strategies That Actually Work
The majority of organizations implement spam filters and provide phishing awareness training. Those controls remain important, but they represent only a portion of the overall situation.
Effective phishing defense measures typically consist of multiple tiers.
User Awareness – Employees should know how to identify suspicious requests and unexpected login prompts.
Identity Monitoring – Security teams need visibility into authentication activity across identity providers and SaaS platforms.
Behavior Monitoring – Unusual login locations or abnormal account behavior can indicate compromised credentials.
Incident Investigation – Once a phishing attempt succeeds, investigators must quickly determine what systems were accessed.
These capabilities form the foundation of effective phishing protection strategies.
Investigating Phishing Incidents in Enterprise Environments
The most critical inquiry following the success of a phishing attack is: what actions did the hacker undertake following the compromised credential?
Security departments need to piece together the behaviour established across several different systems that are usually examined within an incident investigation, including network traffic, authentication logs, and all endpoints in addition to any access to SaaS based applications.
There are several solutions available (for example, NetWitness) that allow investigators to collate the events associated with the previously referenced data sources. By using the visibility provided by the network, historical logs, and endpoint, the analyst can determine if the hacker was able to gain access to any sensitive systems.
By using this visibility, it is possible to gain a greater level of understanding about the overall potential impact that is related to the phishing incidents and can reduce the response times related to these types of incidents.
Why Phishing Remains a Strategic Security Risk
Phishing is not just an email problem. It is an identity problem. Once attackers gain access to a valid account, they may be able to read internal communications, access documents, or launch further attacks from inside the organization.
In many incidents, phishing becomes the first step toward:
- ransomware deployment
- financial fraud
- data exfiltration
- long-term espionage
Security teams that clearly understand what is phishing recognize that the real damage often happens after the initial compromise. Stopping the email is helpful. Detecting suspicious activity after login is critical.
How NetWitness Strengthens Detection After Phishing Attacks
Phishing attacks rarely stop at credential theft. The real risk begins after the attacker logs in. At that point, traditional controls lose visibility. The session appears legitimate. The user is authenticated. From the system’s perspective, nothing is wrong. This is where most security gaps exist.
NetWitness addresses this challenge by providing deep, correlated visibility across network traffic, endpoints, and logs. Instead of treating phishing as an email event, it enables teams to investigate it as a full attack sequence.
With NetWitness, security teams can:
- Trace attacker activity after login- Identify what systems were accessed using compromised credentials.
- Detect abnormal behavior tied to valid users- Surface anomalies in access patterns, data usage, and session behavior.
- Correlate identity, network, and endpoint telemetry- Connect signals across environments to uncover lateral movement.
- Investigate historical activity- Analyze past sessions to determine whether the attack existed before detection.
- Understand true impact- Move beyond “a user clicked” to “this data was accessed and these systems were affected”.
This level of visibility shifts phishing response from assumption to evidence.
Instead of asking “Was this email malicious?”, teams can answer:
- What did the attacker do after access?
- How far did they move?
- What data did they touch?
That difference is critical. Because in modern phishing attacks, detection after compromise determines whether the incident is contained or escalates into a breach.
Conclusion
Over the last two decades, phishing has developed substantially. Originally, the technique consisted of sending spam emails to many people. Today, there are phishing targets, meaning individuals are being targeted for the purpose of obtaining access to business computer systems. Attackers combine social engineering with identity theft and steal user identity credentials to carry out the crime.
Organizations need to have a clear understanding that email security and training on email security will not solve all of their problems regarding phishing. In order to prevent modern phishing attacks, organizations need to have broad visibility into their identity management systems, network usage, and endpoint devices.
By understanding what phishing is today, security teams will be able to earlier detect compromises of user credentials and reduce the damage when attackers use one compromised credential to access numerous businesses.
Frequently Asked Questions
1. What is phishing in cyber security?
Phishing in cybersecurity is when attackers pretend to be another person and trick others into giving out sensitive information such as passwords and money details.
2. What are the four types of phishing attacks?
The different types of phishing attacks include spear phishing, business email compromise, smishing, and the harvesting of credentials through fake login pages.
3. What is the difference between phishing and spear phishing?
Phishing is the type of attack that is sent to a number of users, whereas spear phishing is the type of attack that is sent to a number of users individually. Since these types of attacks appear to be authentic, phishing and spear phishing attacks are successful in the corporate world.
4. Why are modern phishing attacks difficult to detect?
Modern phishing attacks are difficult to detect because they utilize advanced techniques like using cloned SaaS login pages, taking advantage of stolen vendor accounts, and circumventing multi-factor authentication systems.
5. Which industries are commonly targeted by phishing attacks?
Phishing attacks commonly occur in the financial industry, healthcare industry, government organizations, and the technology industry because they contain valuable financial and personal information that can be exploited by cyber attackers.
Autonomous AI Defenders for a Smarter SOC