What OT Security Means for You?
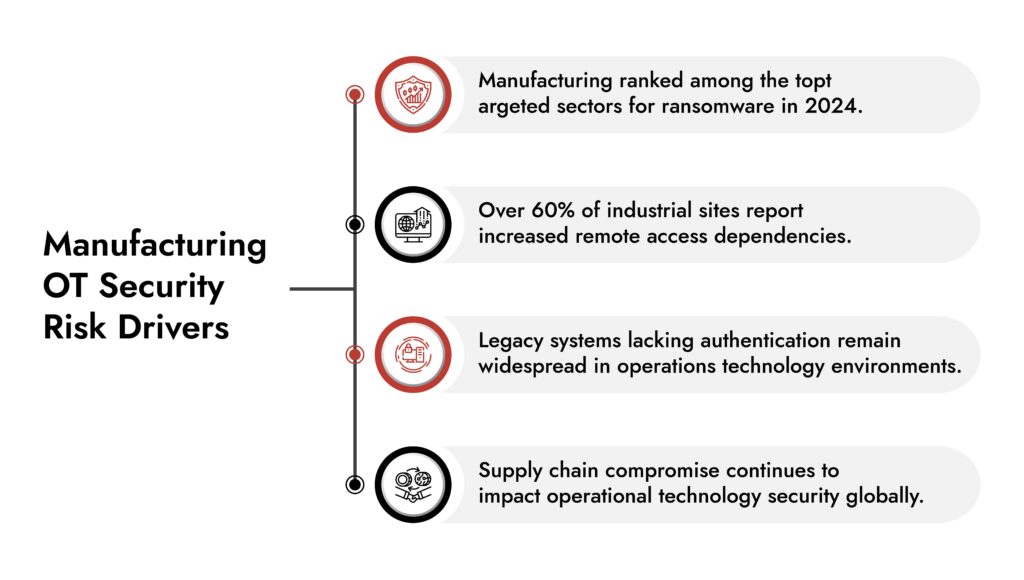
- Manufacturing remains one of the top targeted sectors for ransomware and extortion attacks.
- Most breaches exploit visibility gaps across operations technology environments.
- Strong OT security depends on segmentation, continuous monitoring, and SOC integration.
- Modern industrial cybersecurity requires aligning IT telemetry with OT threat detection.
- Platforms like NetWitness support unified visibility across enterprise and operational environments.
Introduction
Walk through any modern manufacturing plant and you won’t only see conveyor belts and control panels. You’ll see Ethernet cables running alongside power lines, remote vendor sessions open in the background, cloud dashboards tracking production metrics in real time. The factory floor has become a connected system of systems. That connectivity drives performance. It also expands the attack surface. OT security now decides whether production continues as planned or stops mid-shift because ransomware locked a critical controller.
Throughout 2024, CISA and the FBI issued repeated advisories warning that manufacturing remains a prime target, especially in critical infrastructure sectors. Threat actors no longer guess their way in. They look for flat networks, exposed remote access, and unmanaged operation technology assets. The debate is no longer about whether OT security deserves a budget. The sharper question is whether current controls reduce operational risk at the speed attackers evolve.
Why OT Security is Now a Board-Level Risk Issue
Manufacturing leaders lose sleep over more than stolen data. A breached email server is painful. A stopped production line is existential. When operations stall, revenue halts, contracts slip, safety risks rise, and regulators start asking questions. Add supply chain dependencies to the mix, and a single incident can ripple across multiple plants and partners within hours.
OT security exists to protect the systems that keep physical processes running. That means PLCs issuing control commands, DCS environments balancing complex operations, HMIs guiding operators, SCADA systems coordinating distributed assets, and the industrial sensors feeding them all. These are not abstract IT assets. They move valves, regulate pressure, control temperature, and keep heavy machinery synchronized. When they fail or get manipulated, the impact jumps from a screen to the shop floor.
NIST’s Cybersecurity Framework 2.0 and SP 800-82 make this clear. OT risk management requires structure, repeatability, and governance. These frameworks don’t offer theoretical advice. They outline practical controls for industrial environments where uptime and safety matter as much as confidentiality. Treat them as operational discipline, not paperwork. In manufacturing, that discipline separates manageable risk from full-scale disruption.
Here’s what changed:
- IT and operations technology environments are converging.
- Remote maintenance access expanded post-pandemic.
- Legacy systems lack built-in authentication or encryption.
- Threat actors specifically research industrial environments.
Industrial cybersecurity now demands discipline, not improvisation.
Five Core Practices That Strengthen OT Security in Manufacturing
Core Practice #1: Establish Full Asset Visibility for OT Security
You cannot protect what you cannot see. Manufacturing environments often contain decades-old equipment layered with modern sensors and gateways. Asset inventories frequently rely on spreadsheets or outdated diagrams. That gap undermines operational technology security from the start.
Effective OT security begins with:
- Passive asset discovery (no active scanning that disrupts production)
- Protocol-aware monitoring (Modbus, DNP3, OPC, EtherNet/IP)
- Baseline mapping of normal communication patterns
- Continuous updates to asset inventory
According to Gartner’s 2024 industrial cybersecurity research, organizations with continuous OT network monitoring detect incidents significantly faster than those relying on manual audits. OT network monitoring should not operate in isolation. It must feed into enterprise security analytics to enable correlation across IT and OT.
Example: A manufacturing plant detects abnormal Modbus to write commands during off-shift hours. Without centralized visibility, that activity appears harmless. With integrated OT threat detection, it triggers escalation before damage occurs. Visibility is not a dashboard. It is intelligence.
Core Practice #2: Implement OT Network Segmentation With Discipline
Flat networks invite disruption. OT network segmentation separates critical systems from enterprise IT, remote access points, and external vendors. Done properly, segmentation limits lateral movement and restricts blast radius.
Operational technology security improves dramatically when:
- Firewalls enforce strict zone-to-zone communication.
- Industrial DMZs isolate business and control systems.
- Access control policies follow least privilege.
- Remote vendor access routes through monitored gateways.
ISA/IEC 62443 standards provide structured guidance for segmentation in industrial cybersecurity programs. Organizations that follow zoned architectures consistently reduce OT risk exposure.
OT network segmentation must also include monitoring. A firewall without telemetry simply blocks or allows traffic. It does not tell you when someone probes it repeatedly.
Key principle: Segment, then monitor. Not one or the other.
Core Practice #3: Strengthen OT Threat Detection Capabilities
Detection determines resilience. Many manufacturing organizations rely heavily on perimeter defenses. Attackers no longer respect perimeters. They pivot.
Effective OT threat detection requires:
- Behavioral analytics tuned to industrial protocols.
- Detection of abnormal command sequences.
- Monitoring firmware modifications.
- Identifying suspicious remote sessions.
- Correlating IT and OT telemetry.
OT security tools must understand both Windows-based HMIs and PLC traffic. Traditional IT security controls often misinterpret industrial communication as anomalous. Specialized industrial cybersecurity capabilities close that gap.
NIST guidance emphasizes anomaly detection in operational environments because signature-based detection often fails in legacy OT systems. SOC teams must gain contextual insight into OT events. That requires structured integration between OT network monitoring and enterprise SIEM workflows.
Choose the Right OT Cybersecurity Solution with Confidence
- Evaluate platforms built for industrial environments and operational safety.
- Gain full visibility across IT, OT, and industrial control systems.
- Identify solutions that detect threats without disrupting production.
- Make smarter decisions with NetWitness OT security expertise.
Core Practice #4: Formalize OT Risk Management Frameworks
OT risk management requires governance, not just technology.
A mature OT security strategy includes:
- Risk assessments specific to operational technology.
- Safety impact analysis.
- Vendor access reviews.
- Incident response plans tailored to industrial systems.
- Recovery procedures aligned with production continuity goals.
Many organizations treat industrial cybersecurity as an extension of IT security policy. That approach misses critical safety and uptime variables. Operational technology security plans should address:
- Production downtime tolerance thresholds.
- Environmental and safety consequences.
- Regulatory reporting obligations.
- Third-party service dependencies.
The goal is not zero risk. The goal is controlled risk with documented mitigation paths.
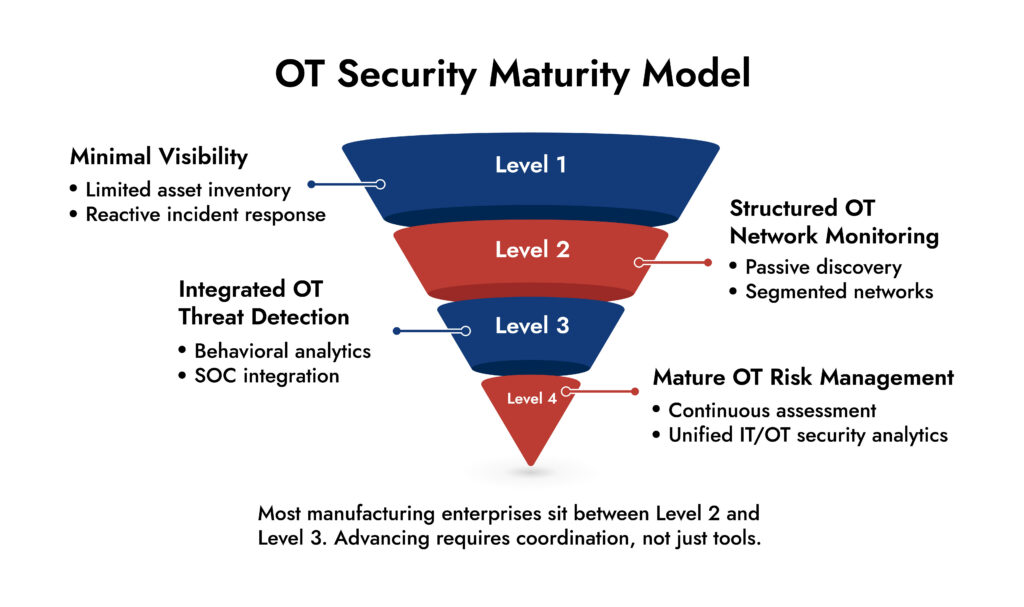
Core Practice #5: Integrate OT Security Into the SOC
The SOC cannot ignore production systems. Historically, OT incidents stayed within engineering teams. Today, ransomware campaigns target both IT and operations technology simultaneously. Segregated response models fail under pressure.
Modern OT security benefits from:
- Unified logging across IT and OT.
- Centralized investigation workflows.
- Correlation between endpoint, network, and industrial telemetry.
- Automated playbooks for containment.
This is the point at which integrated OT security solutions become essential. Platforms that consolidate data ingestion and analytics across areas minimize blind spots.
NetWitness has improved the security of operational technology by collecting and analyzing all relevant types of digital records from a single point of view – whether it be native network traffic, log, or endpoint – through a single pre-defined investigation process in which security teams can more conveniently transition between IT and OT events without having to switch tools or lose context of the overall occurrence.
The outcome: quicker containment and enhanced forensic clarity.
Selecting the Right OT Security Solution
Not all OT security vendors approach the problem the same way. When evaluating OT security tools, focus on:
- Protocol awareness for industrial communication.
- Passive monitoring capabilities.
- Integration with existing SOC platforms.
- Scalability across multi-site manufacturing.
- Support for forensic investigation.
Industrial cybersecurity does not tolerate disruption. Solutions must observe without interfering. An effective OT security solution does more than alert. It provides investigative clarity. That clarity determines whether a potential incident becomes a brief interruption or a plant-wide shutdown.
Conclusion: OT Security is Operational Strategy
The resilience of manufacturing relies on strict execution of OT security. Malicious actors focus on operational settings as interference provides them with advantages. The defense necessitates visibility, segmentation, identification, and coordinated response. Industrial cybersecurity should be in sync with production environments rather than theoretical IT models.
Organizations that consider operational technology security a key component, instead of an afterthought, lower risk in quantifiable ways. The question is not whether your manufacturing environment faces threats. It does. The question is how prepared your OT security program stands when the next attempt unfolds.
Frequently Asked Questions
1. What is OT security in manufacturing?
Security for only networks is a term that encompasses all areas of cybersecurity, including threats to industrial control systems (also known as operation technology, or OT for short) such as process control systems, SCADA systems, and PLCs, thus ensuring standardization of operations on the production floor, safeguarding employees working on machinery, and ensuring that machinery works as intended.
2. What are the biggest OT security risks in manufacturing?
Prioritized threats to OT security include ransomware attacks on production networks, the existence of unsegmented OT networks, unsecure remote access to OT networks, legacy systems that have no authentication process, and a lack of monitoring on OT networks.
3. What core practices reduce OT security risk?
Best practice steps include accurate/complete visibility of all OT assets, segmentation of OT networks using a systematic approach (i.e. subnetwork/switching), accurate identification of OT threats using an advanced threat intelligence platform, appropriate OT risk management through systems and processes, and integrating OT security into SOC processes.
4. Why is network visibility important for OT security?
Network visibility allows for the prompt detection of irregular industrial commands, unauthorized access, and lateral movements. In the absence of OT network monitoring, organizations are unable to identify threats prior to operational disruption happening.
5. What role does the SOC play in OT security?
The SOC is essential as it links IT and OT telemetry, examines alerts, coordinates response measures, and guarantees uniform incident management throughout environments. The coordination is essential for effective operational technology security.
Network Visibility Readiness Guide
Discover how to identify blind spots, monitor traffic across cloud and on-prem environments, and strengthen detection with a practical 7-step evaluation framework. Download the guide to improve investigation speed and security clarity.