What are SIEM Solutions and How do they Work?
Security Information and Event Management (SIEM) solutions are centralized SIEM cybersecurity platforms that collect, analyze, and correlate security data from across an organization’s IT infrastructure.
They ingest logs from firewalls, servers, cloud applications, endpoints, and other security tools, normalize the data, and apply correlation rules, behavioral analytics, and threat intelligence to detect suspicious activity.
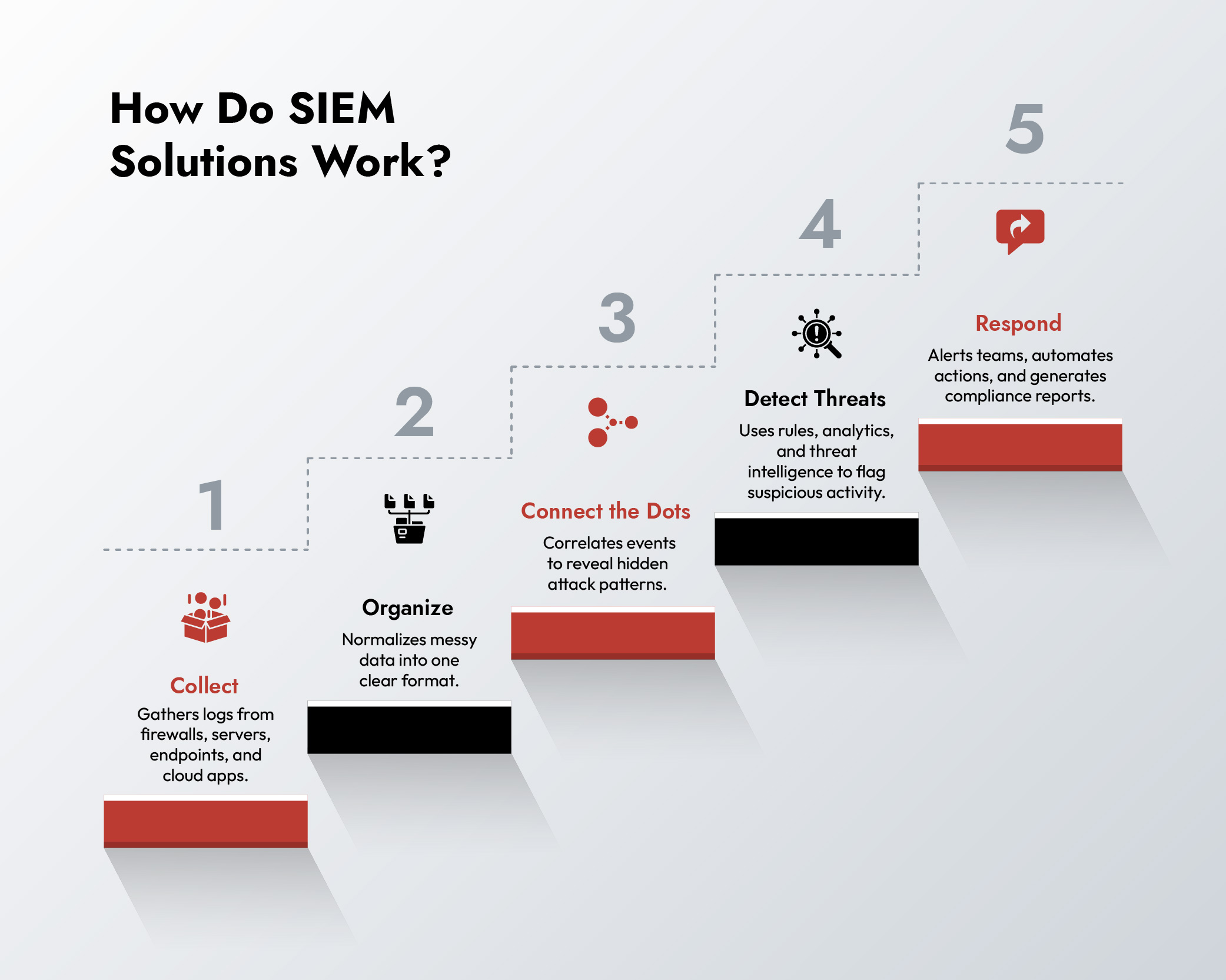
In simple terms, how SIEM works is this:
- Collect security logs from across systems
- Normalize and store the data
- Correlate events to identify patterns
- Detect threats using analytics and intelligence
- Alert analysts and trigger response actions
Modern SIEM security solutions also support SIEM integration with threat detection platforms, automation tools, and response workflows, helping security teams detect and stop attacks faster.
Introduction
Most cyberattacks aren’t flashy smash-and-grab jobs. They’re quiet, calculated, and designed to blend into the background noise of your IT systems. And make no mistakes, the background noise is deafening. The average enterprise generates hundreds of gigabytes of security logs per day across firewalls, endpoints, applications, and cloud workloads. Buried inside that mess might be a single entry that reveals a ransomware payload, a rogue insider, or a stolen credential being used at 3 a.m.
That’s where SIEM solutions earn their reputation. They aren’t just log collectors. They are pattern hunters, context builders, and early-warning radars for modern security teams. Without SIEM tools, your analysts are staring at raw logs. With SIEM cybersecurity platforms, they’re staring at a storyline – who attacked, how, and what to do about it.
How is SIEM Solution Different from Just “Log Management”?
A lot of teams confuse SIEM tools with simple log management. But here’s the expert truth: logs without correlation are just haystacks; SIEM security solutions turn them into needles you can actually see.
SIEM tools don’t just dump data into a warehouse. They:
Ingest from everywhere: Firewalls, IDS/IPS, servers, cloud apps, endpoints, OT systems.
Normalize the chaos: Stripping different log formats into a common structure.
Correlate across time and context: Tying login failures, privilege escalation, and data exfiltration into one coherent attack chain.
This SIEM integration across multiple security technologies is critical because attackers rarely operate in a single system. The ability to correlate events across environments is one of the most powerful SIEM benefits.
That correlation is the difference between spotting an insider threat in hours versus discovering it months later when your data is already on the dark web.
How SIEM Solutions Detect Threats
Detection isn’t magic, it’s layered. A properly tuned SIEM cybersecurity platform combines rules, analytics, and intelligence feeds to spot trouble others miss.
Correlation Rules: If ten failed logins happen in under a minute from a foreign IP, that’s not bad typing, that’s brute force. SIEM tools connect those dots.
Behavioral Analytics: Advanced SIEM security solutions track normal user and system behavior. When your CFO downloads 20GB of HR data at midnight, it knows that’s not “business as usual.”
Threat Intelligence Integration: Through SIEM integration with external intelligence feeds, systems can identify whether an IP address contacting your infrastructure is linked to known malware campaigns, botnets, or command-and-control servers.
This is why many organizations deploy threat detection solutions that integrate with SIEM tools – combining endpoint, network, and threat intelligence insights into a single investigation workflow.
Alerts without context are noise; SIEM cybersecurity platforms make them evidence.
What Happens After a SIEM Solution Detects a Threat?
Here’s where weak implementations fail. A good SIEM cybersecurity doesn’t just scream “something’s wrong.” It guides response:
- Smart Alerting: Instead of 10,000 pings, it escalates the 200 that actually matter.
- Automated Playbooks: Through SOAR integrations, some SIEM solutions can isolate an endpoint or block traffic before human hands are on deck.
- Forensic Timelines: Analysts get a narrative—who logged in, what they touched, and when they escalated privileges.
- Compliance-Ready Reports: PCI, HIPAA, GDPR—all prebuilt so your SOC isn’t wasting cycles making auditors happy.
The net effect? From overwhelm to focus. From firefighting to control.
Key SIEM Benefits for Security Teams
Here’s where the benefits of SIEM solution investment really stack up:
- Visibility at Scale: Attackers rely on blind spots. SIEM strips those away by giving SOCs a panoramic view across hybrid and multi-cloud environments.
- Faster Mean Time to Detect (MTTD): Breaches that once sat unnoticed for 200+ days can now be flagged in minutes. That delta is the difference between a contained incident and a multimillion-dollar breach.
- Operational Efficiency: Instead of analysts drowning in log files, they focus on high-value investigations. Repetitive triage tasks get automated.
- Audit Simplification: Compliance stops being a time sink because reports are baked into the system.
Remember this line: a single prevented breach pays for SIEM ten times over.
Elevate Threat Detection and Response with NetWitness® SIEM
-Correlate data across users, logs, and network for unified visibility.
-Detect advanced threats with AI-driven analytics and behavioral insights.
-Accelerate investigations using automated enrichment and guided workflows.

Why Managed SIEM Services are Growing Rapidly
Many organizations deploy SIEM tools, then struggle to maintain them. Correlation rules grow outdated. Integrations break. Analysts ignore alerts. That’s why managed SIEM services are becoming increasingly common.
Specialized providers manage the platform and continuously optimize it by:
- Keeping detection rules updated
- Maintaining SIEM integration with evolving security technologies
- Monitoring threats 24/7
- Delivering tuned alerts directly to internal SOC teams
For mid-size enterprises, especially SIEM services provide the expertise needed to maximize the value of SIEM cybersecurity platforms.
Challenges Organizations Face with SIEM Solutions
It’s not all glory. Any security information and event management deployment faces hurdles:
- Integration Complexity: Plugging in legacy systems can feel like forcing square pegs into round holes.
- False Positives: Poorly tuned SIEMs overwhelm teams with noise.
- Cost Sprawl: Log storage and ingestion costs can grow quickly if retention policies are not optimized.
The reality is simple: SIEM solutions deliver value only when organizations invest in tuning, governance, and skilled analysts.
The Future of SIEM Cybersecurity
The next generation of SIEM tools is already reshaping the security operations landscape.
- AI and Machine Learning- Advanced analytics are replacing static detection rules.
- UEBA Integration- User and Entity Behavior Analytics helps detect insider threats and compromised accounts.
- SOAR Integration- Modern SIEM security solutions increasingly combine monitoring with automated response.
- Cloud-Native Architectures- New SIEM tools are built specifically for hybrid and multi-cloud environments.
Whether called SIEM evolution or convergence with XDR, one thing is clear, modern SIEM cybersecurity platforms are moving from passive monitoring to active defense.
Conclusion
SIEM solutions work because they transform noise into knowledge. They cut through the flood of events, surface the signals that matter, and give organizations a fighting chance against attackers who thrive in complexity.
Whether deployed internally or delivered through managed SIEM services, the outcome remains the same: visibility, speed, and resilience.
In today’s threat landscape, those capabilities are not optional. They are foundational to modern SIEM cybersecurity strategies.
Frequently Asked Questions
1. What is a SIEM solution and why is it important?
A SIEM solution is a centralized cybersecurity platform that collects and analyzes security logs from across an organization’s infrastructure. It is important because it provides real-time threat detection, improves visibility across systems, and enables faster incident response.
2. How does a SIEM detect threats?
A SIEM cybersecurity platform detects threats using correlation rules, behavioral analytics, and threat intelligence feeds. By analyzing patterns across multiple systems, SIEM tools can identify suspicious activity that might otherwise go unnoticed.
3. How does a SIEM solution work?
Understanding how SIEM works involves five key steps: data collection, normalization, correlation, threat detection, and alerting. Modern SIEM solutions also integrate with automation tools to trigger response actions when threats are detected.
4. What are the key benefits of a SIEM solution?
Key SIEM benefits include improved threat visibility, faster detection of attacks, operational efficiency for security teams, and simplified compliance reporting.
5. How are next-generation SIEM tools evolving?
Next-generation SIEM tools are evolving through AI-driven analytics, behavioral monitoring, deeper SIEM integration with security platforms, and cloud-native architectures designed for modern hybrid environments.
Choose the Right SIEM with Confidence