What is network log analysis and how does it work with NDR in a SIEM-driven SOC?
Network log analysis examines logs generated by network devices, applications, and security tools to identify suspicious activity and reconstruct events during a security investigation. In a modern SOC, SIEM SOC network analysis correlates logs from multiple sources, while Network Detection and Response (NDR) adds deeper visibility through network packet capture and network packet analysis.
When SIEM and NDR integration is implemented, security teams can combine network log management, network visibility, and network forensic analysis to understand both the event timeline and the actual data that moved across the network. This layered approach allows analysts to validate alerts, detect stealthy attacks, and investigate incidents with full packet-level evidence.
Introduction
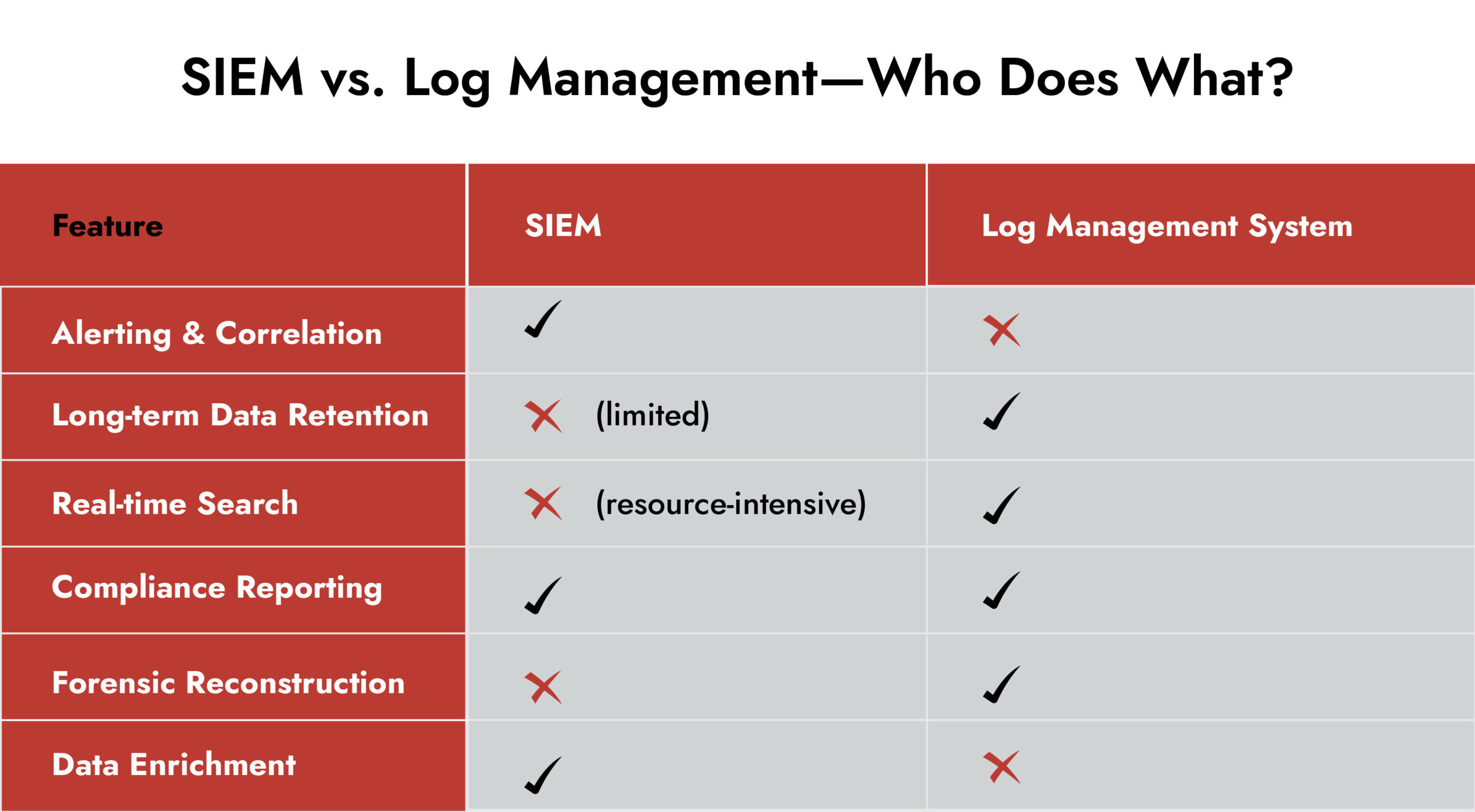
Security teams rely on SIEM platforms to stitch together events across their entire environment. SIEM collects logs, correlates alerts, and enables SIEM SOC network analysis across endpoints, cloud services, and infrastructure. But here’s the reality: SIEM alone cannot always provide the packet-level evidence required to understand what happened during an attack.
That is where network log analysis combined with Network Detection and Response (NDR) becomes essential. By integrating network packet capture, network packet analysis, and centralized network log management, security teams gain deeper network visibility and stronger investigative capabilities. The result is a SOC that can move from alerts to verified evidence faster.
Why Network Log Analysis Still Matters with SIEM
Modern SIEM solutions ingest enormous volumes of logs, normalize them, and correlate events into a single view. That’s invaluable, but it can’t replace network log analysis for several reasons:
- Aggregation ≠ Analysis: SIEM summarizes data for performance. Packet details and subtle anomalies are often abstracted out.
- Storage Trade-offs: Many SIEM deployments limit retention, so low-level activity may vanish before an investigation begins.
- Alert Fatigue: Quiet, multi-stage attacks may never trigger an automated alert.
Pairing SIEM log management with NDR-driven network log analysis ensures you retain the full story, not just the headlines.
Redefining Network Log Analysis with NDR
Traditionally, network log analysis referred to parsing logs from routers, firewalls, and switches. That still matters, but NDR changes the game.
NDR sensors capture packets and extract rich metadata – flows, payloads, and session details, while simultaneously feeding your SIEM. This creates a multi-layer view:
- Logs show who connected and when.
- NDR shows what moved and how.
Together, they give analysts the confidence to validate alerts and hunt hidden threats.
Simplify Log Management and Threat Detection with NetWitness® Logs
- Centralize and analyze logs from across your environment in one platform.
- Detect threats faster with real-time visibility and automated correlation.
- Reduce noise through advanced filtering and context-driven analytics.
When Network Log Analysis with NDR Makes the Difference
Imagine your SIEM reports a privileged account making an unusual outbound connection. Without NDR-backed network log analysis, you can’t answer questions that matter:
- Did the event follow repeated failed logins?
- Did packet captures confirm data exfiltration?
- Was it a scheduled process or a human command?
Only by combining packet capture with log correlation can you reconstruct the full timeline.
Why Network Visibility Requires Both Logs and Packets
Effective detection depends on network visibility, and that visibility comes from combining multiple telemetry sources.
Network log analysis provides structured records of authentication events, system activity, and device behavior. But attackers often hide inside legitimate sessions, which makes deeper inspection necessary.
This is where network packet analysis and network packet capture become critical. Instead of relying only on summarized logs, analysts can inspect the raw traffic moving across the network.
When SIEM and NDR integration is implemented, security teams gain:
- Full network forensic analysis capabilities for incident investigations
- Correlated insights across logs, packets, and alerts
- Deeper SIEM SOC network analysis across hybrid environments
- Stronger detection of stealthy threats and lateral movement
Together, these capabilities turn fragmented telemetry into actionable intelligence.
Role of Log Management Systems
Strong log management systems remain the foundation of effective network log analysis. They handle:
- High-volume collection and indexing.
- Long-term retention for compliance and retrospection.
- Tamper-proof storage for legal defense.
- Flexible querying for ad-hoc investigations.
A dedicated log management tool ensures packet-level insights from NDR and high-fidelity logs from SIEM log management stay accessible long after an incident.
How NetWitness NDR Complements SIEM for Deeper Network Log Analysis
NetWitness unifies SIEM and NDR into one investigative environment where network log analysis thrives:
- Full-Packet and Metadata Integration – Analysts move seamlessly from an alert to the underlying packets and related logs.
- Contextual Reconstruction – Packet data combined with log events tells the entire attack story.
- Retrospective Hunting – Search weeks or months of packets and logs for indicators of compromise.
- Custom Retention Policies – Align storage with compliance mandates and internal security needs.
This synergy means your team can pivot from a SIEM alert to NDR packet evidence in seconds, reducing mean time to detect and respond. 
Best Practices for Effective Network Log Analysis
- Centralize Network Log Management
Feed logs from firewalls, servers, applications, and identity systems into SIEM while integrating NDR telemetry for deeper analysis. - Enable Network Packet Capture for Critical Segments
Packet capture ensures that investigators have access to the raw network evidence needed for network forensic analysis. - Combine Packet and Log Correlation
Strong SIEM and NDR integration allows analysts to pivot from alerts to network packet analysis instantly. - Maintain Long-Term Data Retention
Both logs and packet metadata should be retained long enough to support investigations that rely on historical network log analysis. - Use Network Visibility to Establish Baselines
Understanding normal traffic patterns helps SOC teams identify suspicious behavior faster during SIEM SOC network analysis.
Final Thought: Logs and Packets Together Tell the Truth
Dashboards are summaries. The reality of an intrusion lives in packets and raw logs.
With SIEM for correlation and NDR for deep inspection, network log analysis becomes the SOC’s most reliable truth source. It may not be flashy, but when an investigation turns critical, you’ll be glad those packets and logs were captured, stored, and ready to tell the full story
Frequently Asked Questions
1. What is network log analysis in cybersecurity?
Network log analysis is the process of examining logs from network devices, servers, and security tools to detect suspicious activity. It helps SOC teams maintain network visibility and supports investigations through structured network log management.
2. How does network log analysis enhance a SIEM solution?
Network log analysis strengthens SIEM by providing detailed event data for SIEM SOC network analysis. With centralized network log management, SIEM platforms can correlate logs across systems to detect threats faster.
3. What role does NDR play in network log analysis?
Network detection and response (NDR) enhances network log analysis by adding network packet capture and network packet analysis. This gives analysts deeper network visibility into the traffic behind security alerts.
4. How does network log analysis improve threat investigation?
Network log analysis helps investigators reconstruct events during an incident. When combined with network forensic analysis and network packet analysis, analysts can understand how an attack started and moved across the network.
5. What are best practices for effective network log analysis in a SOC?
Best practices include centralized network log management, strong SIEM and NDR integration, enabling network packet capture, and using network visibility to baseline normal traffic for faster threat detection.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.