What is Advanced Threat Detection?
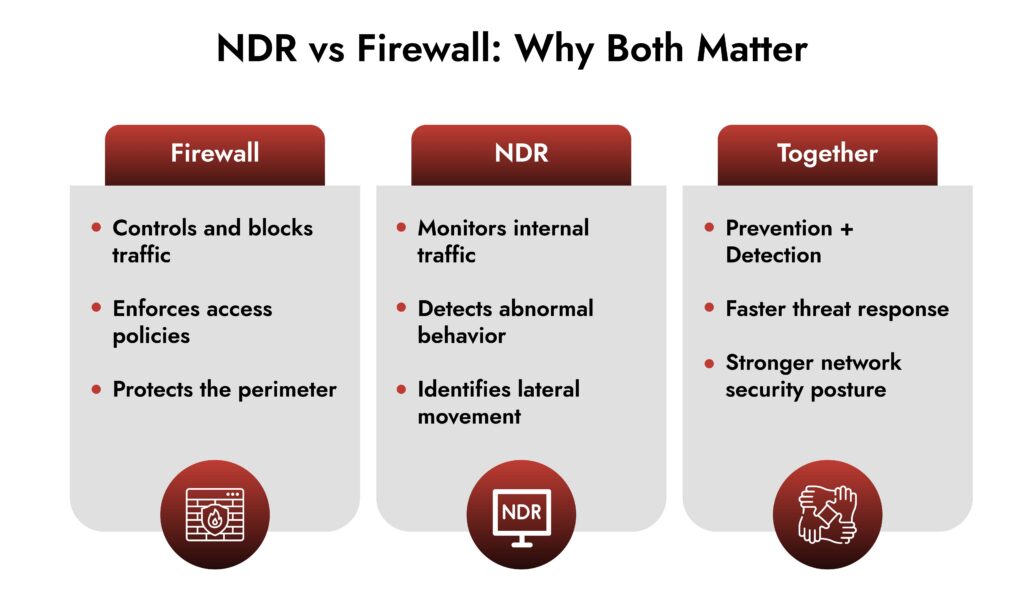
- A firewall controls and blocks unauthorized traffic based on rules.
- NDR monitors internal and external network behavior & traffic to detect advanced threats.
- Firewalls focus on prevention.
- NDR focuses on detection and response.
- Modern security requires both for complete network visibility and protection.
Introduction
If you’re building a serious security program in 2026, this debate keeps coming up: NDR vs firewall. Some teams assume their network firewall security stack already has them covered. Others are investing heavily in NDR security and wondering if traditional firewalls still matter.
Here’s the thing. This isn’t an either-or decision. It’s about understanding roles, gaps, and how attackers actually move inside modern networks. Let’s break it down properly.
What a Firewall Actually Does
A firewall for network security is your gatekeeper. It sits at the boundary of your network and decides what traffic is allowed in or out based on defined rules.
At its core, a network security firewall:
- Filters traffic based on IP, port, and protocol
- Blocks unauthorized access attempts
- Segments internal networks
- Enforces policy-based access control
- Supports firewall & network protection at the perimeter
Modern firewalls, especially next-generation ones, add:
- Application awareness
- Intrusion prevention
- URL filtering
- SSL inspection
In short, firewalls and network security go hand in hand because the firewall is your first line of defense. But here’s the catch. Firewalls are designed to prevent unauthorized traffic based on predefined rules. They are not designed to deeply analyze behavioral anomalies inside the network once traffic is allowed. That’s where NDR enters the picture.
What NDR Actually Does
NDR security stands for Network Detection and Response. Instead of blocking traffic at the edge, NDR monitors what’s happening inside the network.
NDR for SOC teams focuses on:
- Continuous network traffic analysis
- Behavioral anomaly detection
- Lateral movement identification
- Command-and-control detection
- Insider threat visibility
Unlike a network firewall protection system that relies heavily on rule enforcement, NDR uses:
- Behavioral analytics
- Machine learning models
- Threat intelligence correlation
It doesn’t just ask: “Is this port allowed?”
It asks: “Is this behavior normal for this device, user, or workload?”
That shift in mindset changes everything.
NDR vs Firewall: The Core Differences
Let’s compare them directly.
1. Primary Purpose
- Firewall: Prevent unauthorized access and enforce network policy.
- NDR: Detect suspicious or malicious behavior inside allowed traffic.
Firewalls control the gate. NDR watches what happens after the gate opens.
2. Placement in the Network
- Network firewall security: Typically deployed at the perimeter and between network segments.
- NDR security: Monitors internal traffic across east-west and north-south flows.
In modern environments with hybrid cloud and remote work, east-west traffic has exploded. Firewalls often miss what happens between internal systems.
3. Detection Capability
A firewall for network security blocks based on known rules and signatures.
NDR security detects:
- Unknown threats
- Zero-day behavior patterns
- Lateral movement techniques
- Encrypted command-and-control traffic anomalies
That’s why NDR is increasingly considered one of the most effective network threat detection tools for advanced attacks.
4. Response Mechanism
Firewalls respond by:
- Blocking traffic
- Dropping packets
- Denying sessions
NDR responds by:
- Generating high-fidelity alerts
- Enriching attack context
- Integrating with automated incident response tools
- Triggering containment workflows
For SOC teams, this context is critical. NDR for SOC teams provides visibility they can investigate, validate, and act on quickly.
Why Firewalls Alone Are No Longer Enough
There was a time when perimeter defense worked.
Now consider:
- Remote users connecting from unmanaged networks
- Cloud workloads communicating internally
- Encrypted traffic hiding malicious payloads
- Attackers using valid credentials
A network security firewall will allow traffic that matches policy, even if that traffic is malicious but well disguised.
For example:
- Stolen credentials used legitimately
- Malware communicating over allowed HTTPS ports
- Insider misuse within internal segments
What this really means is simple:
- If an attacker gets past your firewall, you need visibility inside the network.
- Without NDR, that visibility is limited.
Why NDR Alone Is Not Enough
On the flip side, relying only on NDR security without network firewall protection is risky.
Without a firewall:
- You increase exposure at the perimeter
- You lose granular traffic control
- You weaken segmentation policies
- You allow unnecessary attack surface
NDR is not designed to replace a network firewall security system. It is designed to enhance detection where prevention alone falls short.
How NDR and Firewalls Work Together
This is where the real power lies.
When combined:
- Firewall enforces access control – Only approved traffic enters and leaves the network.
- NDR monitors allowed traffic deeply –It inspects behavior patterns across internal systems.
- Context is correlated – Firewall logs + NDR analytics provide complete visibility.
- Response becomes faster – NDR detects lateral movement → triggers automation → firewall blocks malicious IPs or segments hosts.
For SOC teams, this layered approach dramatically improves mean time to detect and respond.
Think of it this way:
Firewall = Prevention
NDR = Detection + Context
Together, they strengthen overall firewall & network protection architecture.
Real-World Attack Scenario
Imagine this sequence:
- Phishing email compromises a user credential.
- Attacker logs in using legitimate VPN access.
- Firewall allows connection because credentials are valid.
- Attacker begins lateral movement across internal servers.
The firewall sees normal authenticated traffic.
NDR security sees abnormal behavior patterns:
- Unusual internal scans
- Access to high-value servers
- Suspicious data transfers
NDR flags the activity. SOC responds. Firewall updates rules to block the malicious source. That’s layered security in action.
DORA Compliance with NetWitness® Network Detection & Response (NDR)
Strengthen Digital Operational Resilience with Deep Network Visibility
Meet EU DORA requirements with continuous network monitoring, advanced threat detection, and automated response across complex financial environments.
Should Small Organizations Use Both?
Many smaller organizations assume NDR is only for large enterprises.
But here’s the reality:
- Ransomware targets mid-sized businesses aggressively
- Supply chain attacks don’t discriminate
- Cloud adoption increases internal complexity
Even a lean deployment combining:
- A properly configured network firewall protection setup
- Lightweight NDR capabilities can significantly reduce blind spots.
Budget constraints are real. But so is breach cost.
NetWitness NDR
NetWitness NDR helps SOC teams move beyond basic network firewall protection with deeper visibility and behavioral detection.
Key capabilities:
- Full packet and metadata analysis for deep network visibility
- Detection of lateral movement and encrypted command-and-control traffic
- Behavioral analytics to uncover unknown and zero-day threats
- Correlation of firewall logs with network activity for richer context
- Faster investigation and response workflows for SOC teams
Is NDR Necessary for Enterprise Environments?
For large enterprises, the answer is almost always yes.
Enterprise environments include:
- Hybrid cloud infrastructure
- Multi-branch connectivity
- High east-west traffic volume
- Complex identity ecosystems
In these settings, network threat detection tools that only rely on logs are insufficient.
NDR for SOC teams delivers:
- Deep packet metadata analysis
- Cross-segment behavioral visibility
- Rapid lateral movement detection
- Scalable monitoring across distributed environments
At enterprise scale, internal visibility becomes non-negotiable.
Building a Modern Network Security Strategy
If you’re evaluating NDR vs firewall, don’t frame it as replacement.
Instead ask:
- Where are my visibility gaps?
- How quickly can I detect lateral movement?
- Do I rely solely on rule-based prevention?
- Can my SOC correlate network behavior in real time?
Strong network firewall security creates a hardened perimeter. Strong NDR security ensures that once traffic is inside, suspicious activity cannot hide. Security maturity isn’t about choosing one tool. It’s about layering controls intelligently.
Frequently Asked Questions
1. What is the main difference between NDR and a firewall?
A firewall enforces network access rules and blocks unauthorized traffic. NDR analyzes internal network behavior to detect suspicious activity, including threats that bypass perimeter controls.
2. Can NDR replace a firewall?
No. NDR complements but does not replace a network security firewall. Firewalls provide essential perimeter protection, while NDR delivers internal visibility and behavioral detection.
3. How do NDR and firewalls work together?
Firewalls filter and control traffic. NDR monitors allowed traffic for anomalies. When combined, they improve detection accuracy and speed up response actions.
4. Should small organizations use both firewall and NDR?
Yes, if budget allows. Even small organizations face advanced threats. A properly configured firewall plus basic NDR capabilities significantly improves network security resilience.
5. Is NDR necessary for enterprise environments?
In most enterprise environments, yes. Large, distributed networks require continuous internal monitoring that traditional firewalls alone cannot provide.
Proactive Network Threat Detection with NetWitness® NDR
-Spot threats fast with AI-driven analytics.
-See everything across your network and cloud traffic.
-Investigate efficiently with built-in forensic tools.
-Adapt and scale to meet growing security needs.