No business runs purely on-prem anymore. But it’s not purely cloud either. The current and future forecast is cloudy. We have a mixed reality where workloads and data are spread out. They are found in data centers, clouds, SaaS platforms, and endpoints. Security teams must connect the dots in this large ecosystem. That’s where SIEM solution comes in.
Traditional SIEM tools weren’t designed for this complexity. So, what does cloud SIEM security actually look like when your infrastructure is hybrid, dynamic, and always shifting?
Let’s break it down.
Evolution from Traditional SIEM Solution to Cloud SIEM Security
Old-school SIEM tools were built to ingest logs from servers, network devices, and a handful of cloud apps via connectors. They were heavy, resource-intensive, and rarely scaled without expensive upgrades. As your environment expands beyond the firewall, these SIEM tools either become noisy, blind, or unaffordable.
Cloud based SIEMs are different. They are designed to grow easily. They take in data from cloud APIs. They watch container workloads and serverless functions. They can handle billions of events each day without reaching storage or compute limits. In hybrid security operations, this scalability isn’t optional – it’s foundational.
What Hybrid Infrastructure Demands from your SIEM Security
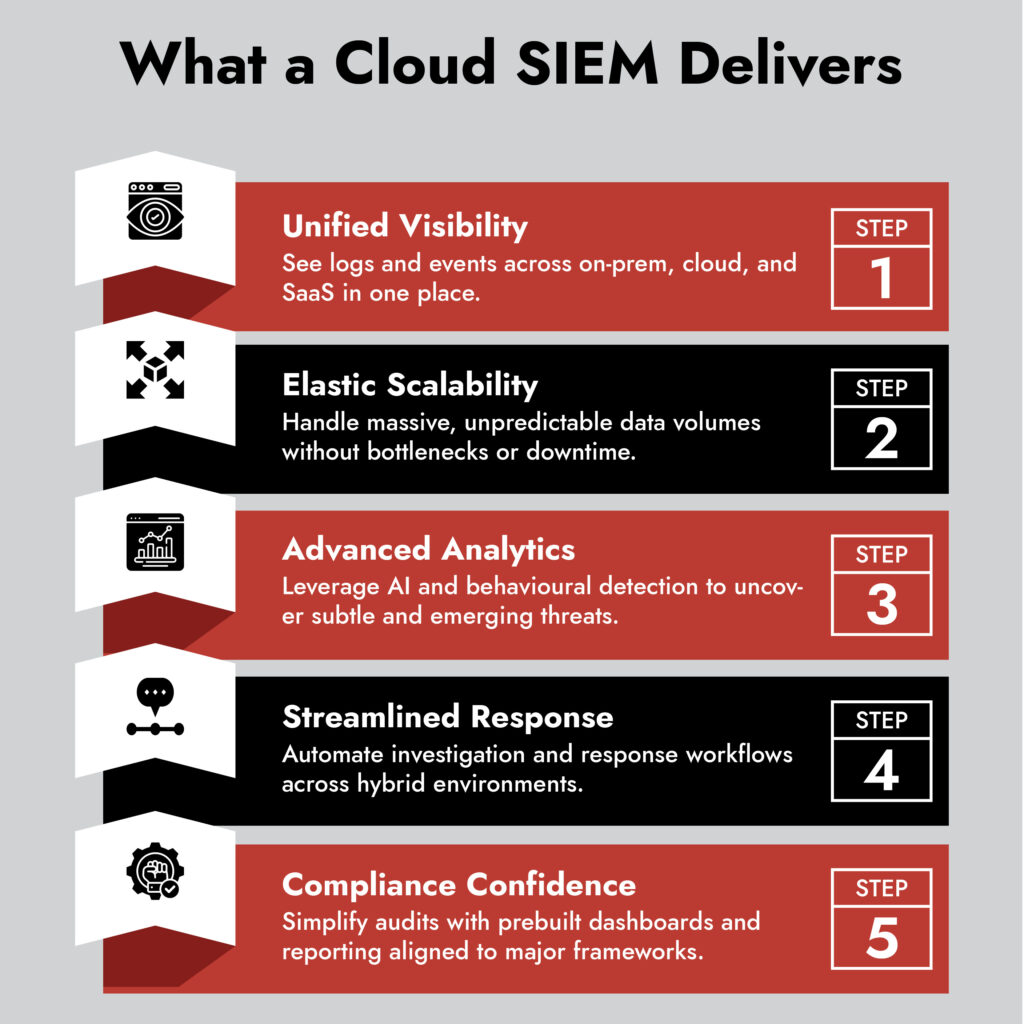
1. Unified visibility across on-prem and cloud
Your SIEM must gather, connect, and analyze data from all sources. This includes on-prem firewalls, cloud workloads, SaaS apps, identity providers, and container platforms, all in one place. Separate monitoring stacks for on-prem and cloud are a recipe for blind spots. Expect your SIEM to integrate natively with AWS CloudTrail, Azure Monitor, GCP Logging, and your existing on-prem tools.
2. Elastic scalability
Hybrid workloads generate unpredictable data volumes. Your SIEM solution must handle ingestion bursts, long-term retention, and analytics scale-out without manual reconfiguration. Otherwise, incident investigations stall when you need them most.
3. Advanced analytics powered by cloud
The true benefit of cloud SIEM is its ability to provide analytics that old SIEMs cannot manage. This includes behavioral analytics, UEBA, and AI-driven anomaly detection. These tools can identify subtle threats, such as on-prem lateral movement and cloud IAM abuse.
4. Streamlined threat hunting and response
Modern cloud SIEMs automatically add context to alerts. This includes details like asset importance and IAM policies. They also coordinate responses across your hybrid environment. Blocking malicious IPs in your firewall and cloud security groups simultaneously shouldn’t require separate playbooks.
5. Flexible deployment models
Many vendors now provide hybrid deployments. In these setups, sensitive data stays on-site or in private clouds. Meanwhile, analytics run in the provider’s environment. This matters for regulated industries with strict data residency requirements.
6. Compliance and audit readiness
Your SIEM should make compliance easier. It does this by normalizing logs for standards like PCI DSS, HIPAA, or ISO 27001. It also automates reporting across different environments. Hybrid infrastructures are compliance nightmares if you don’t have unified visibility.
Key trends shaping cloud SIEM for hybrid security
- Convergence with XDR: SIEMs are integrating with endpoint and network detection tools to provide extended detection and response.
- AI-driven detection and investigation: Machine learning models are becoming core to identifying anomalies across hybrid workloads.
- Decoupled storage and compute: This enables cost-effective long-term data retention with flexible processing power on demand.
- Open integration ecosystems: Closed proprietary SIEMs are giving way to open, API-driven architectures that integrate with diverse tools.
- Privacy-preserving analytics: Techniques like federated learning allow detection across domains without breaching data residency.
Choosing your Cloud SIEM security for the hybrid world
If you’re evaluating cloud SIEM secuirty solutions, ask:
- Does it integrate natively with your cloud providers and SaaS apps?
- Can it handle ingestion spikes without spirallingspiraling costs?
- Does it unify analytics across cloud and on-prem data?
- Can it orchestrate responses across your entire environment?
- Does it support open APIs to connect with your security stack?
Final thoughts
Here’s the thing. Hybrid infrastructure isn’t going away. Security teams need visibility and detection that keeps up. That’s where NetWitness SIEM makes a difference.
ネットウィットネス SIEM lets you monitor logs from one place, no matter where they come from. This includes on-prem, virtual, hybrid, or public cloud sources. Its pervasive log visibility helps your team administer and analyze data across distributed and virtual environments, enabling faster detection and response.
In a world where your digital landscape keeps expanding, NetWitness ensures your SIEM keeps up.
よくある質問
1. What is cloud SIEM security?
A cloud SIEM is a Security Information and Event Management solution hosted in the cloud. It collects and analyses security data from on-prem, cloud, and hybrid environments to detect threats in real time.
2. How does cloud SIEM support hybrid infrastructures?
Cloud SIEMs work with on-prem systems, public clouds, private clouds, and SaaS platforms. They give you a clear view and scalable analytics for your whole digital environment.
3. Why are traditional SIEMs insufficient for hybrid security?
Traditional SIEMs have trouble scaling, integrating with the cloud, and analyzing large data volumes. This can create blind spots and slow down threat detection.
4. What makes NetWitness SIEM effective for hybrid security?
NetWitness SIEM provides clear log visibility and centralized monitoring. It allows you to deploy collection components on-site, virtually, or fully in the cloud. This setup helps with quick detection and response.
5. What are the key benefits of using a cloud-native SIEM?
Cloud-native SIEMs provide elastic scalability, advanced analytics, automated threat response, and easier compliance reporting across hybrid infrastructures.



