ランサムウェアの標的としてのUSMSと法執行機関への広範な影響
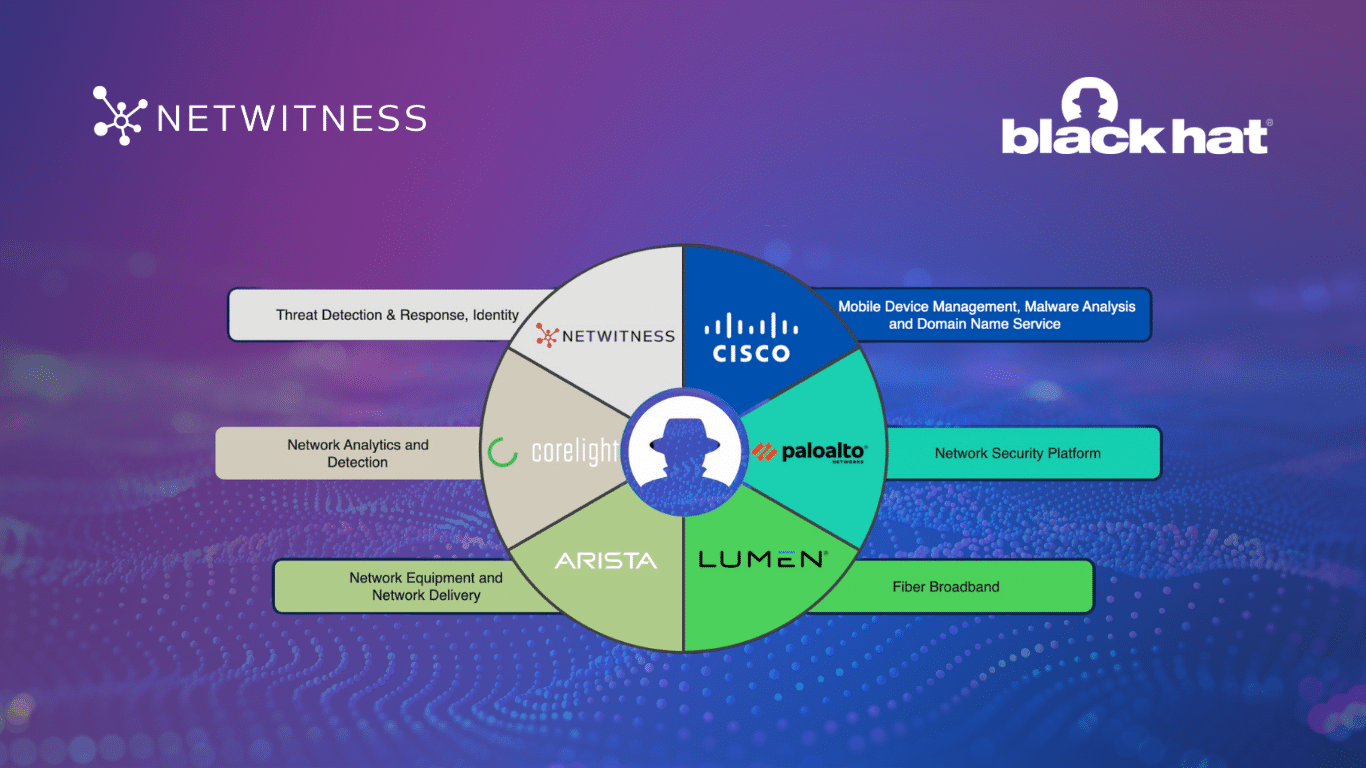
The mission of the U.S. Marshals Service (USMS) is “to enforce federal laws and provide support to virtually all elements of the federal justice system” through multiple disciplines. Its law enforcement (LE) focus, reach and scope make this week’s report of a recent cyberattack involving both ransomware and data exfiltration especially concerning. While this news is fresh, and the incident ongoing, it’s a good time for us all to reflect on why LE entities can be especially attractive targets to bad actors. As with all important things in life, it always pays off to understand motivations and incentives, and how they can drive behaviors and actions. Low-hanging fruit of […]
もっと読む