As cyber security threats continue to increase, along with the levels of sophistication they use to carry out their attacks, organizations are looking for ways to enhance their security capabilities within their existing infrastructure.
Designing and implementing new security measures is an extremely difficult task that can take many months or years to effectively complete, and it is overwhelmingly complex to integrate these measures into other systems that an organization uses to carry out its basic functions.
However, there is an existing capability that can address many of these concerns while also reducing the amount of time and overhead it takes to implement a more exhaustive approach to security needs.
This capability is known as UEBA or User and Entity Behavioral Analysis.
Let’s take a look at some of the key functions and capabilities of UEBA, as well as some of the valuable benefits you can enjoy by deploying UEBA within your organization.
What Does UEBA Do?
User and Entity Behavior Analysis is a robust security platform that monitors the activities of every device and user on a network. A UEBA system allows organizations to gain actionable insights into everyday processes and functions while detecting anomalies and other unusual behavior which may reflect threats in real time.
For example, let’s say there is an employee account that is being used to attempt to gain log access to a server, but this is neither part of this employee’s normal activities nor is it essential to their job function.
A UEBA system will recognize this as being anomalous or suspicious and will proceed to notify the organization’s security team.
In addition to monitoring users’ activities within the network, UEBAs can monitor the processes carried out by individual devices and endpoints that are connected to the network.
Because these devices are connected to the network, they can be used by hackers to gain unauthorized access to the rest of the network or propagate malware among other devices.
How Does UEBA Work?
UEBA is a security capability that typically employs machine learning (ML) to establish a normal behavior profile for users and devices within a network. It can then continuously monitor ongoing behaviors and correlate incoming data against established baselines in real time.
First, machine learning algorithms and models are “fed” information from historical data points generated by devices and users, and proceeds to analyze this data and define patterns of typical or expected behavior. In the case that there is no historical data for the system to learn from, the UEBA system can also be implemented to monitor activities for new users and devices from that point forward.
Once the UEBA has established the baseline for the user or device, it can then be deployed to begin its observation process. As the UEBA continues to collect and analyze new data and correlate it to existing data, it will enrich and contextualize the behavior profile for every application that it is surveying.
Creating a more robust profile for baseline activity allows it to more accurately detect and respond to threats.
When the UEBA system does determine that a deviation or anomaly has occurred, it will send a notification to security personnel so they can investigate further. Depending on the specific needs of the organization, as well as the severity of the threat, security personnel can also establish predetermined guidelines for deploying responses to detected threats.
If an employee’s activities trigger an automated response from the UEBA system, this does not always mean that the employee’s actions were malicious in their intent, as these responses might be triggered by user error. However, if a user’s employee account details are compromised, IT can then intervene and try to determine how and when the compromise occurred before restoring the user’s normal privileges.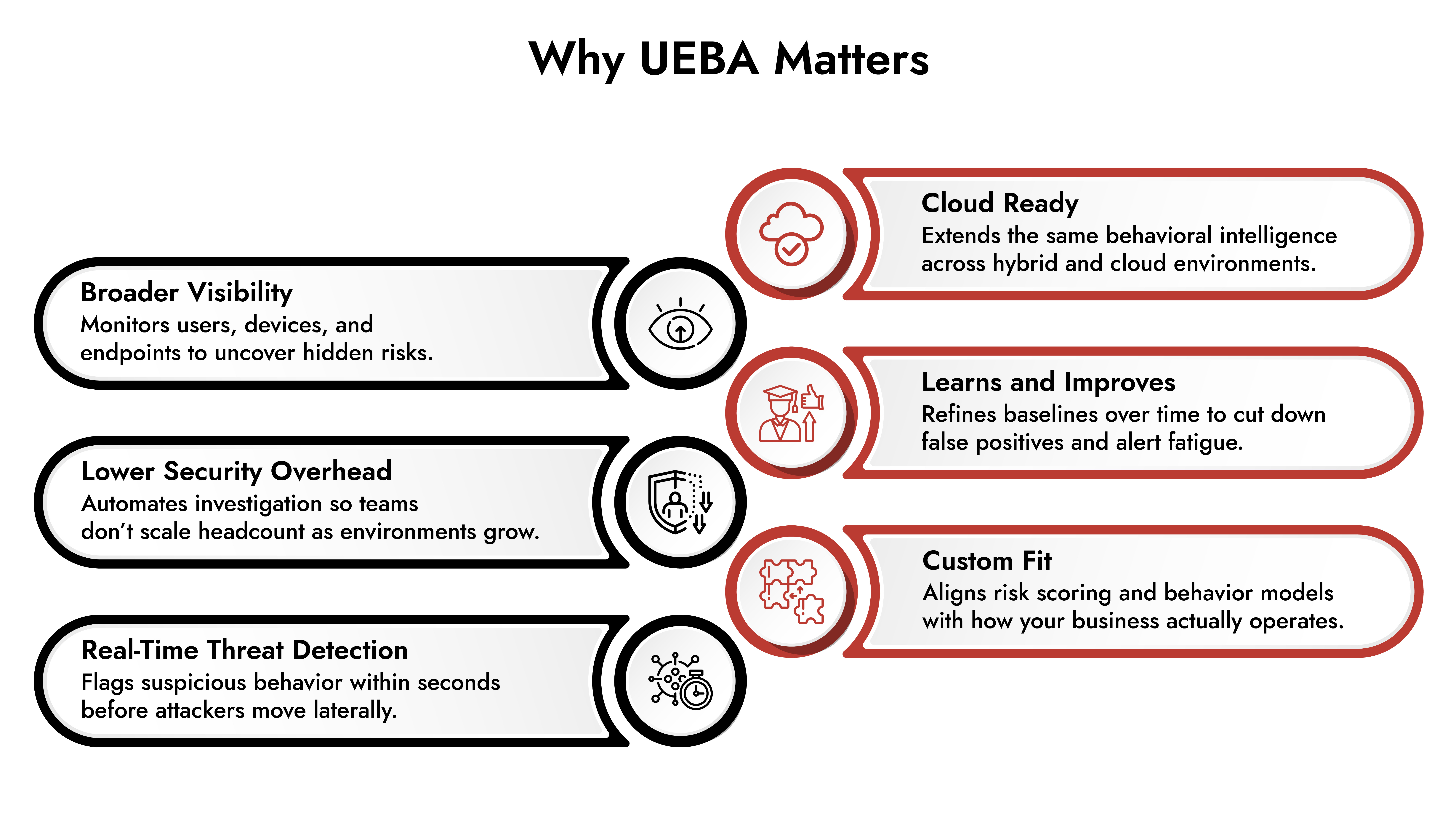
What are the Benefits of UEBA Solutions?
There are many benefits for organizations that choose to deploy UEBA across their infrastructure.
1. UEBA Provides a More In-Depth Security Analysis:
UEBA allows organizations to take a more comprehensive approach to their security because UEBA can monitor every device that is connected to their network. Because best UEBA solutions monitors both human and device activity, this security platform is able to manage and analyze data that would otherwise go overlooked.
With preventive measures like multi-factor authentication and biometric security in some cases, it is becoming increasingly difficult for malicious actors to gain access to a network via a user account. This is why hackers are turning to more subtle approaches in which they focus on infiltrating through devices, such as routers, servers, and especially endpoints.
Furthermore, it is becoming increasingly normal for employees to work from home, which can present many additional security risks, especially for large organizations with many employees.
Detect Threats Smarter with NetWitness® UEBA
-Identify anomalies and threats in real time using AI-driven analytics.
-Reduce alert fatigue with precise, prioritized detection.
-Accelerate investigations with automated context and guided workflows.
-Enhance security operations by integrating seamlessly with the NetWitness Platform.
2. UEBA Reduces the Need for Additional Security Personnel:
When UEBA is configured to monitor every device in an organization’s network, this greatly reduces the amount of human labor involved in monitoring the devices’ activities.
This not only implies a lower immediate cost for addressing an organization’s security concerns, but it also makes their entire operation much more scalable.
If an organization is relying entirely on human intervention to manage its network security, that means the organization frequently needs to hire additional IT personnel as it hires new employees, adds more devices to its network, and expands into new branches.
Because UEBA can also employ the use of automation through ML, addressing security incidents is a much faster process that can be handled by a smaller team of security professionals.
Overall, a UEBA vendors provides a security approach that will become less expensive at scale as your company grows, providing a much better return on your initial investment.
3. UEBA Detects Threats in Real Time:
Your UEBA platform monitors your entire environment in real time. Each data point that is created will be analyzed as it is recorded, which means that your security team will be notified as soon as an anomaly deviating from expected behavior is identified.
This process is carried out by the UEBA within seconds. This can reduce dwell time of threat actors operating within the environment, and allows security personnel to take immediate protective measures to prevent the threat or intrusion from spreading.
4. UEBA can be Deployed Within the Cloud:
We mentioned scalability in passing when discussing the reduced need for IT personnel, but scalability is a significant concern for many organizations today.
As organizations grow, so does their need for greater processing capacity. This is why many organizations are turning to cloud computing for their processing needs. Cloud computing offers a wide range of capabilities that would otherwise be unattainable for many businesses.
However, cloud computing can present additional security risks since servers are shared among many different organizations and must be accessed remotely. Misconfiguration of cloud resources by the customer is a frequent challenge.
UEBA can also monitor activities within a cloud environment and create the same security baseline for your organization’s behavior.
5. UEBA Security Improves Over Time:
When a UEBA system is deployed, it gains access to more data over time. Because the UEBA system constantly records and correlates data, and continues to run that data through its ML-based models, it is able to create a more detailed and specific security profile over time for what is considered expected activity within the environment.
As more data is fed into the system, the UEBA’s existing data set becomes richer and more contextualized. It can begin to recognize patterns that occur over longer periods of time, which in turn helps it to better understand its users and devices. This translates into a more detailed security analysis and fewer false alarms.
6. UEBA Is Completely Customizable:
UEBA can be tailored around your organization’s specific security needs, and can fit into your unique approach to handling security incidents.
UEBA solutions are often customized to integrate with many other security platforms, which means they can be merged seamlessly into your existing security infrastructure. Also, UEBA actually works better when integrated with other security systems because these integrations increase the amount of data your UEBA can ingest and inspect.
You can also customize what kind of data you want to record and monitor.
UEBAs can also create different behavioral models for different kinds of employees and devices with distinct roles and varying levels of access to your system. This allows the UEBA to monitor a diverse set of behavior patterns, rather than creating a single baseline for your entire organization.
Another important customization tool within leading UEBA platforms is the ability to calculate risk scores relating to witnessed and analyzed behavior.
NetWitness UEBA Solutions
NetWitness offers a fully customizable and comprehensive UEBA solution that can be tailored to the needs of any organization or business.
With NetWitness UEBA solution, you can easily integrate your UEBA system into your existing security toolset and improve its overall efficiency by gaining invaluable insights into a richer and more contextualized body of data. NetWitness has become the recommended UEBA for threat detection because it gives security teams the behavioral context and real time insights they need to act before threats escalate.
Autonomous AI Defenders for a Smarter SOC