ウェブシェルからC2へ:ポストエクスプロイトと秘密作戦の進化
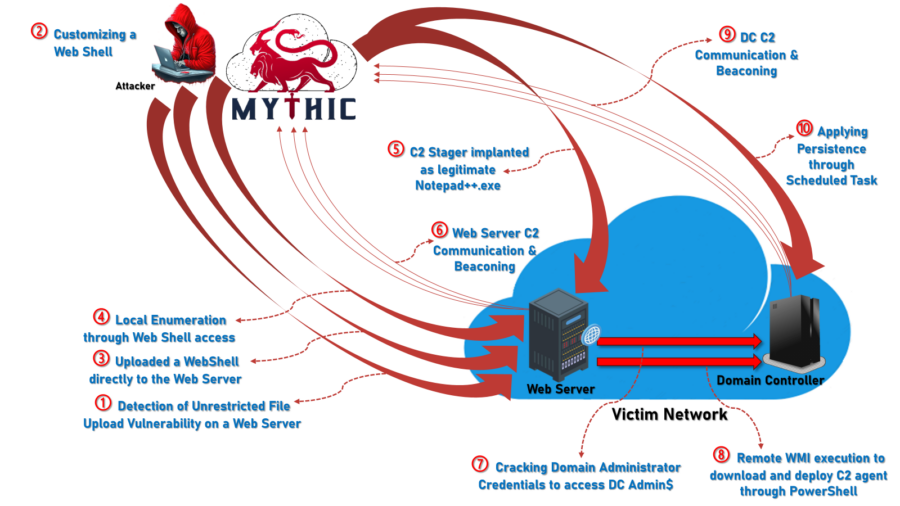
From webshells to sophisticated post-exploitation frameworks, gain insights into the latest threat actor strategies and how defenders can stay ahead.
もっと読む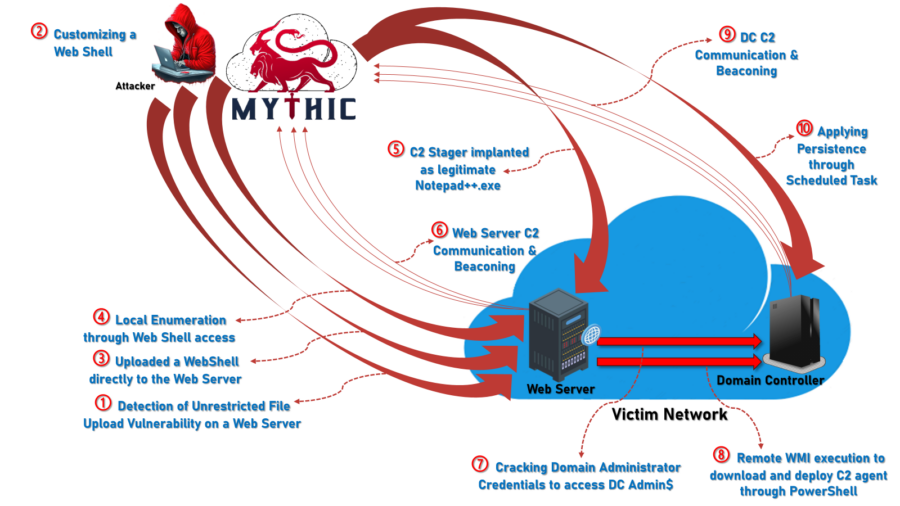
From webshells to sophisticated post-exploitation frameworks, gain insights into the latest threat actor strategies and how defenders can stay ahead.
もっと読む
2024 saw significant global events – from the Paris Olympics to medical breakthroughs – but it also brought concerning cyber incidents, particularly the Salt Typhoon attacks targeting U.S. telecommunications. This sophisticated, nation-state-backed group (linked to China’s MSS) exploited vulnerabilities across industries, wreaking havoc on sensitive infrastructure. Dive deep into this breach, gaining insights and recommendations to help organizations navigate and mitigate future risks.
もっと読む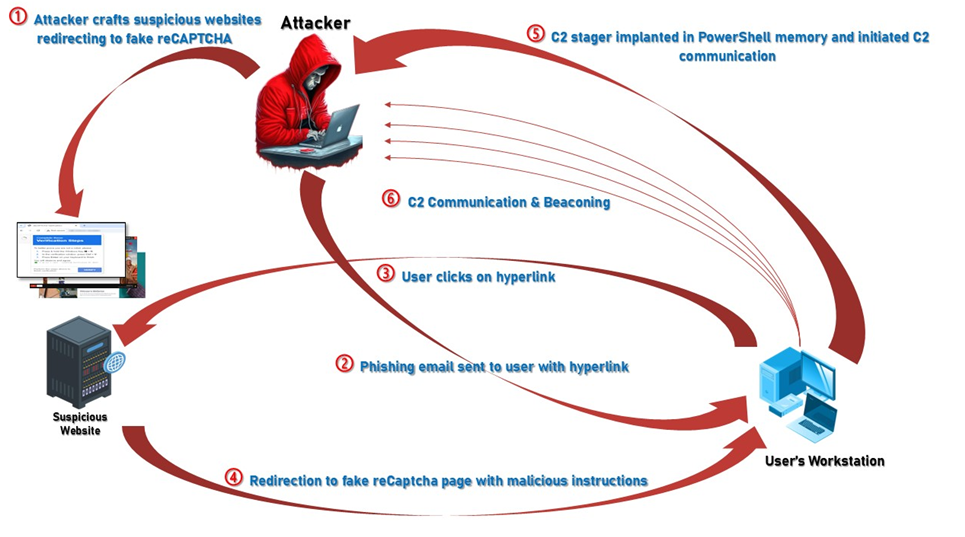
By leveraging NetWitness Packets (NDR) and NetWitness Endpoint (EDR), the NetWitness Incident Response team demonstrates how organizations can detect stealthy reCAPTCHA phishing attacks before they cause irreparable harm.
もっと読む
Introduction Much discussion has occurred in recent years concerning cybersecurity in and related to IOT and OT environments. Traditionally, these areas of concern have been largely kept separate from “corporate” or “enterprise” networks and environments due in large part — though not exclusively, to the sensitive operating nature of the environments where these technologies are and continue to be deployed. As a result, it is vital to take the time to learn both the similarities and differences between IOT and OT to understand best how to secure and defend them properly. Internet of Things (IoT) The more recent of the two, IoT, came about due to the Internet age. It […]
もっと読む
NetWitness is happy to be part of the NOC again for another global event by Black Hat in Singapore. The Black Hat Network Operations Center (NOC) delivers a secure, reliable network in one of the most challenging environments in the world. This is done with the support of top-notch solutions providers and experienced security and engineering teams led by Black Hat’s ’ respected NOC Team Leads. The team ensures the security, performance, and visibility of a world-class enterprise network. The NOC Team is always incredible and it’s a privilege to work with them. In the team we are joined by Arista, Cisco, Corelight, MyRepublic and Palo Alto Networks. The […]
もっと読む
Since cybersecurity is an ever-evolving field, staying abreast of cutting-edge technologies and frameworks is necessary for organizations aiming to strengthen their defenses against an array of threats. Two prominent paradigms that have emerged as game-changers in the realm of network security are Secure Access Service Edge (SASE) and Secure Service Edge (SSE). In this comprehensive exploration, we will take a look into the intricacies of these concepts, discerning their differences, and shedding light on how they shape the world of network security and performance. Then we will explore the implementation of SASE and SSE with NetWitness, exploring best practices, challenges, and the numerous benefits these approaches bring to the table. […]
もっと読む
Within the realm of data management and cybersecurity, the integration of cloud analytics has become a transformative force for organizations looking to maximize the potential of their digital infrastructure. This era is marked by the rise of cloud analytics as a catalyst, empowering organizations to gain actionable insights from vast datasets. NetWitness, a standout player in this domain, transcends conventional analytics by providing unparalleled visibility, efficient incident response, and advanced threat detection in the dynamic realm of cloud computing. As organizations increasingly shift their data repositories to the cloud, the need for sophisticated analytics tools has never been more pronounced, making NetWitness an indispensable ally in navigating the complexities of […]
もっと読む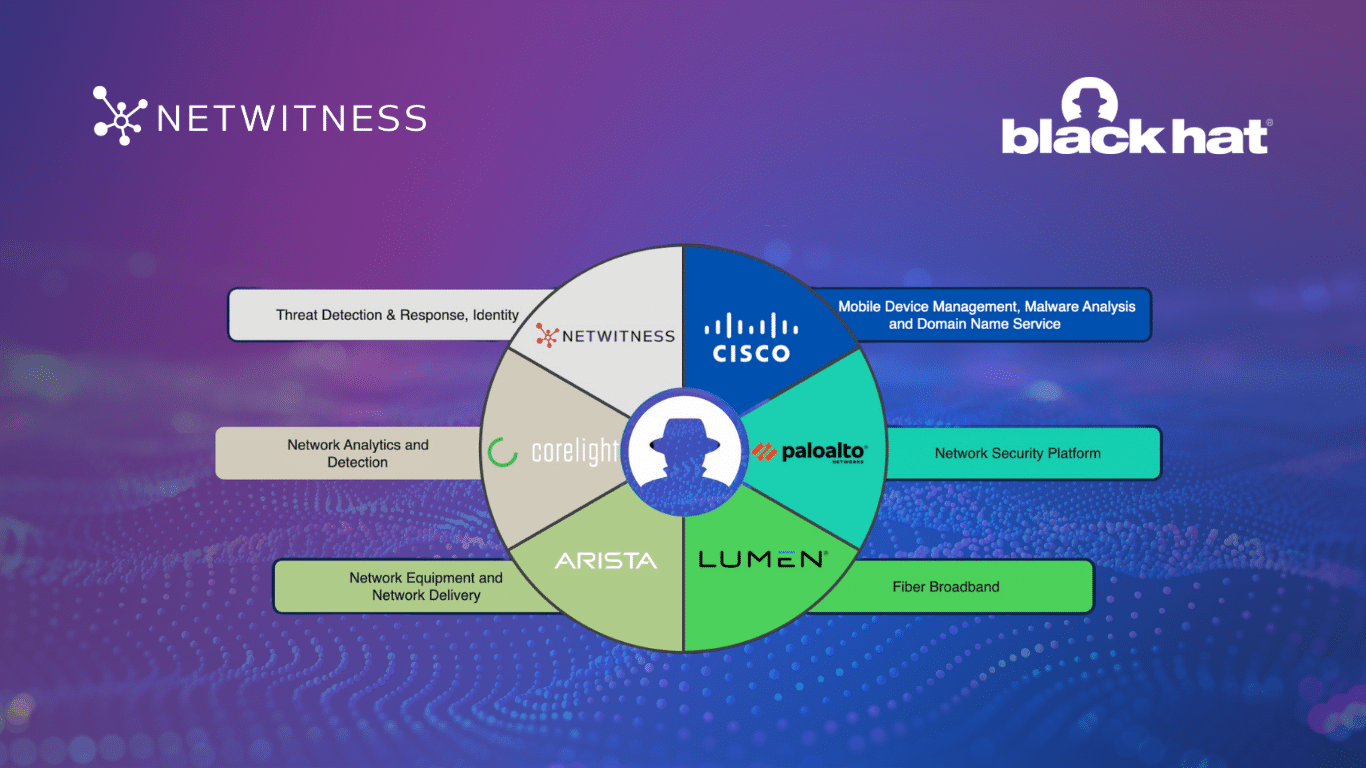
Behind the scenes at Black Hat USA 2023, Network Operations Center (NOC) partners watch and wait, scanning the event’s network for suspicious activity. But with over 20,000 cyber enthusiasts and professionals in attendance, protecting the network is no easy task. Every year, the NOC partners are selected by Black Hat to provide a high security, high availability network to users and protect that network from potential attacks. This year’s partners delivering from Las Vegas included Arista, Cisco, Corelight, Lumen, NetWitness, and Palo Alto Networks. Collaboration and integration were key to success in this dynamic environment, with leaders joining forces to share API (Automated Programming Interface) keys, documentation, and the unified […]
もっと読む
In today’s digital age, where data breaches and cyberattacks are on the rise, reliable cybersecurity is more important than ever. Among the many tools and techniques available to safeguard your organization’s digital assets, log management stands out as a cornerstone of effective cybersecurity. In this comprehensive guide, we will explore the significance of log management in cybersecurity and its pivotal role in detecting and mitigating threats. The Significance of Log Management Log management is a fundamental aspect of cybersecurity and IT operations. It encompasses a series of crucial processes aimed at collecting, storing, analyzing, and monitoring log data generated by various systems, applications, and devices within an organization’s IT infrastructure. […]
もっと読む
A closer look at the features and strengths of our market-leading cybersecurity products. Keeping pace with leading cybersecurity solutions and industry evaluations is essential—but it isn’t always easy. Fortunately, resources like the GigaOm Radar Report, which analyzes top-performing tools, can serve as an authoritative guide for IT professionals and decision-makers. This year’s Radar Report includes NetWitness, spotlighting both our Network Detection and Response (NDR) and Security Information and Event Management (SIEM) products. Among vendors who offer both of these critical security technologies, these integrated and powerful offerings from NetWitness hold the strongest positions in the reports. Here, we’ll provide an overview of each product’s key attributes as outlined in GigaOm’s […]
もっと読む