Security Information and Event Management SIEM management services has become non-negotiable for enterprises serious about staying ahead of threats. It’s not just about collecting logs anymore. It’s about making sense of the noise, connecting dots across complex environments, and responding fast when something is off.
But here is the million-dollar question: should you manage SIEM internally or hand it off to a dedicated service provider?
There’s no one-size-fits-all answer. The right call depends on your goals, maturity, internal bandwidth, and risk appetite. This blog breaks down so you can decide what works best for your organization.
First, a Quick Primer: What Is SIEM in Cybersecurity?
SIEM stands for Security Information and Event Management, and while it’s a cornerstone of today’s security operations, it wasn’t always this advanced. Early SIEM solutions emerged in the mid-2000s to centralize log management, pulling data from firewalls, servers, and applications into one place. At the time, the goal was mainly compliance reporting and basic rule-based alerting.
Over the years, as threats grew more complex, SIEM management services have evolved into a true investigative and detection engine. Today, SIEM platforms do more than collect logs. They apply analytics, correlate activities across endpoints, networks, cloud environments, and users, and highlight the patterns that matter.
To appreciate this evolution, it helps to step back:
- 로그 are the raw records: who logged in, which file was accessed, what traffic hit the firewall.
- Security events are the meaningful signals extracted from those logs, things that may indicate risk.
- Security incidents, however, go one step further. They aren’t declared by the SIEM itself. Instead, incidents are formally recognized and acted upon by your SOC or Incident Response (IR) team after analysis and validation.
This distinction matters. A SIEM’s role is to surface and contextualize events, giving your analysts the visibility to determine whether an actual incident is unfolding.
Modern SIEM platforms now go well beyond static rules. They incorporate User and Entity Behavior Analytics (UEBA), threat intelligence feeds, and even automation through Security Orchestration, Automation, and Response (SOAR). This means faster, more accurate detections, and fewer false positives.
Put simply, if you’re still asking, “what is SIEM in cyber security?”, think of it as your organization’s control room. The central nervous system that processes signals from across your digital environment, enabling your teams to detect, investigate, and act with clarity.
SIEM Mangement Services: In-House vs. Outsourced
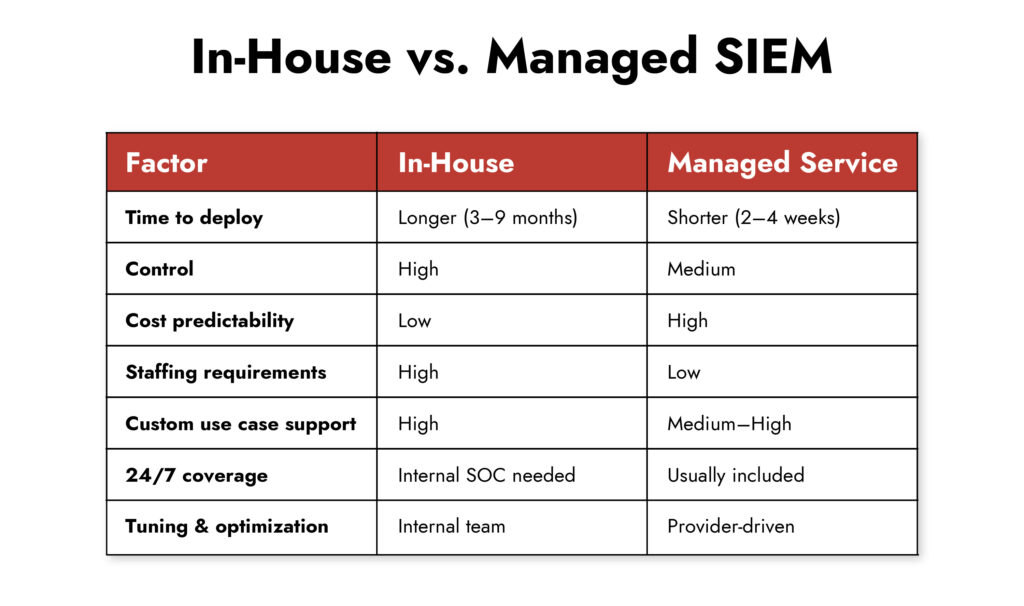
Once you are sold on SIEM, the next decision is how to manage it. Broadly, you’ve got two options:
- In-house SIEM management: You build and maintain the system internally, staffing analysts, engineers, and architects to keep it running.
- SIEM management services: You partner with a third-party provider to run, tune, monitor, and evolve your SIEM environment.
Each path comes with trade-offs. Let’s explore them.
In-House SIEM Management: Control, But at a Cost
Managing SIEM solutions internally means you own the process, data, and decision-making end-to-end. That can be a huge advantage, if you have the right people and resources.
Pros:
- Total visibility and control over detection logic, escalation paths, and playbooks.
- Customization: Tailor use cases, dashboards, and integrations to fit your environment.
- Data stays within your perimeter, which may matter for regulatory or privacy reasons.
Cons:
- High operational overhead: SIEM solution isn’t plug-and-play. It demands constant tuning, threat intel updates, and content engineering.
- Talent shortage: SIEM specialists are expensive and hard to maintain. And burnout is real.
- Alert fatigue: If your rules aren’t optimized, analysts drown in false positives- driving up costs and increasing burnout risk.
- Slower time-to-value: Getting full value from a SIEM platform can take months or even years of iteration.
Here’s the thing- a SIEM is only as good as the team behind it. Without experienced staff to maintain and optimize the system, you risk having an expensive logging tool that doesn’t move the needle on actual detection or response.
SIEM Management Services: Scale and Speed Without the Headcount
SIEM management services by a third-party team handles the complexity for you. Think of it like a managed pit crew that keeps your security engine tuned, aligned, and ready to race.
Pros:
- Faster ramp-up: Providers come with prebuilt content, detection rules, and integrations, so you’re up and running sooner.
- 24/7 monitoring: Many services include a dedicated SOC that keeps an eye on your environment around the clock.
- Access to niche expertise: You get skilled SIEM engineers, threat hunters, and incident responders without hiring them full-time.
- Scalability: Easily handle spikes in log volume or new use cases without redesigning your entire SIEM setup.
Cons:
- Less direct control: You may need to align your needs with the provider’s processes and SLAs.
- Potential for slower response handoffs: If the service only monitors and doesn’t respond, you’re still on the hook for action.
- Visibility trade-offs: Depending on the provider, you may not see everything under the hood.
Still, for many enterprises, especially those facing staffing shortages or expanding across hybrid cloud, managed services make a lot of sense. The key is finding a partner who offers transparency, collaboration, and integration with your existing workflows.
Strategic Questions to Ask Before Choosing SIEM Management Services
- Do you have (or can you hire) SIEM engineers, content developers, and incident responders?
- Is your security team large enough to monitor alerts 24/7?
- Can you commit to ongoing tuning, log onboarding, and threat detection updates?
- Do you have budget flexibility for training, tooling, and cloud scaling?
If you answered “no” to more than two of these, consider a hybrid or managed approach.
A Cost Perspective: Consider SIEM Software Pricing
Let us talk about numbers, because that’s usually where the debate lands.
Running a SIEM in-house isn’t cheap. Between licensing, infrastructure, staffing, and content upkeep, costs can escalate fast. According to the Ponemon Institute’s 2023 report, the average cost of running a mid-sized SIEM internally hovers between $1.2 and 1.8 million annually, excluding breach-related losses.
On the other hand, SIEM management services typically come with predictable pricing models based on data volume, endpoints, or SLA tiers. That makes budgeting easier, though you’ll need to watch for hidden costs like onboarding fees or custom detection requests.
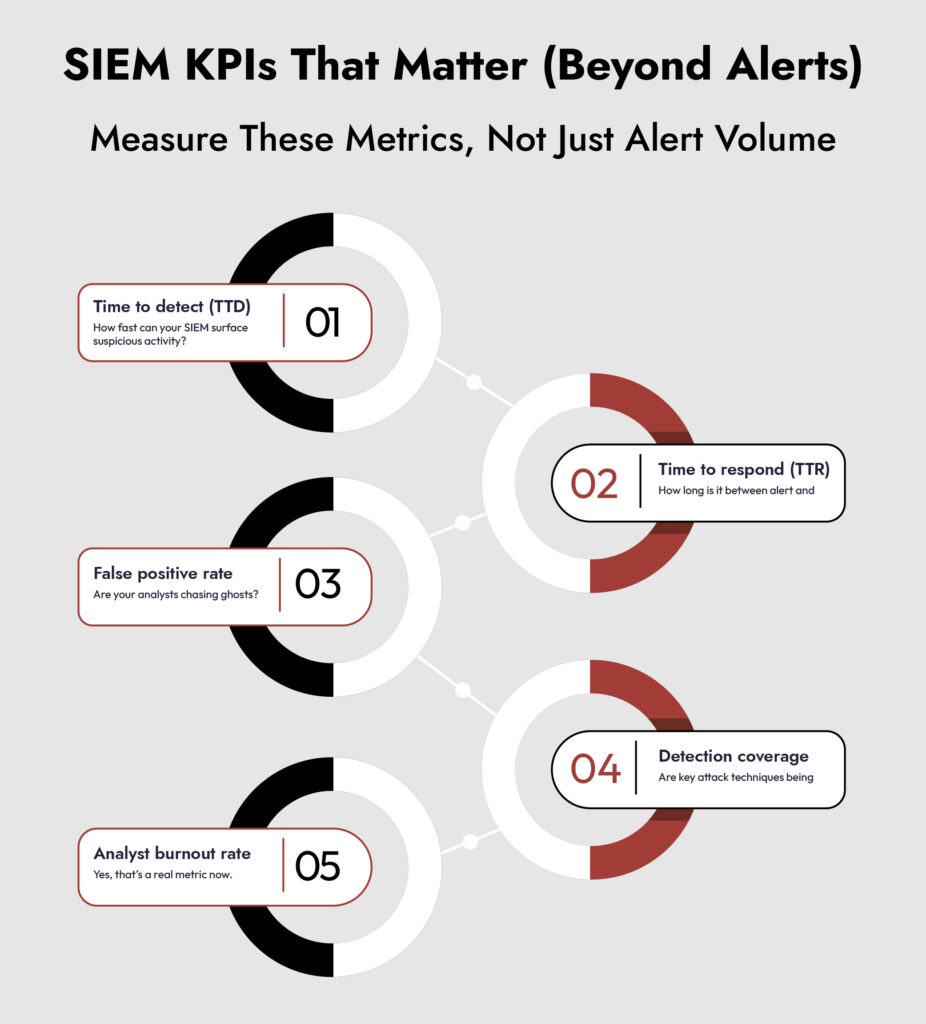
But here is what matters more than upfront cost: operational value.
If your in-house SIEM is missing threats or overwhelming analysts with noise, it’s not delivering value, no matter how much you’ve invested. The same holds true for managed SIEM. A SIEM vendor may handle log collection, tuning, and monitoring, but if they stop short of helping you act on alerts or supporting incident response, the cost can quickly outweigh the benefit.
In both models, the real test isn’t how the security information and event management is deployed, it’s whether it helps your organization detect, investigate, and respond to threats in a meaningful way.
Hybrid SIEM Management: The Middle Ground
Not every decision needs to be binary. Many enterprises adopt a hybrid model:
- Keep detection engineering or response in-house
- Outsource platform management or 24/7 monitoring
This gives you control where it matters most while offloading the heavy lifting that slows your team down.
A well-designed hybrid model aligns your internal capabilities with external strengths, so you’re not forced to choose between visibility and velocity.
Where NetWitness SIEM Fits In
The debate between in-house and SIEM management services often comes down to trade-offs: control vs. cost, visibility vs. complexity, flexibility vs. staffing requirements. NetWitness SIEM is designed to reduce those trade-offs and give enterprises the best of both worlds.
- Bridging control and efficiency: For organizations that want to manage things themselves, NetWitness offers clear analytics and complete visibility. This helps avoid problems like alert fatigue and blind spots. With deeper correlation across endpoints, networks, and users, teams spend less time tuning noise and more time investigating real threats.
- Supporting managed or hybrid models: If you lean toward managed services, NetWitness integrates smoothly with service providers. The platform’s transparency and rich telemetry make it easy for partners to monitor, tune, and escalate alerts without cutting the enterprise out of the loop.
- Scaling without staffing strain: Whether run internally or with a provider, NetWitness SIEM’s automation and built-in orchestration reduce the manual lift of log management, use case development, and response, easing the pressure on overextended security teams.
- Professional Services for lasting value: Successful SIEM deployments require more than technology. NetWitness Professional Services works with organizations during design, rollout, and ongoing tuning to ensure the SIEM program aligns with business priorities and delivers sustained results.
In short, NetWitness SIEM minimizes the compromises that enterprises typically face when deciding between in-house and managed models. It adapts to your operating model, helping you maintain control of where you want it, and leverage external support where you need it. Learn more about NetWitness SIEM
Final Thoughts: Choose for Agility, Not Just Ownership
SIEM isn’t a checkbox. It’s an engine. And like any engine, it needs regular tuning, expert hands, and clear telemetry to perform well.
If you have the team, time, and tooling, managing it in-house can offer incredible control and customization.
But if you’re stretched thin, chasing alerts, or struggling to scale, managed SIEM services may be the smarter move.
What this really comes down to is agility. Choose a model that helps you detect and respond faster, without burning out your team or overextending your budget.
This is where NetWitness SIEM solution stands out. It’s built to give organizations flexibility in how they deploy and manage it – whether fully in-house, through managed services, or in a hybrid approach. With its unified visibility across logs, endpoints, networks, and cloud data, plus built-in orchestration and analytics, NetWitness helps security teams pivot quickly as threats evolve. That agility means faster detection, more relevant alerts, and response workflows that adapt to your environment, not the other way around.
Ready to take a closer look at your SIEM strategy? Whether you’re building from scratch or optimizing what you already have, the right model is the one that keeps you informed, fast, and focused. Not just on threats, but on outcomes.
자주 묻는 질문
1. Can I start with managed SIEM services and later bring it in-house?
Yes. Many organizations start with a managed provider to get up and running, then gradually transition parts of the operation in-house as their team matures.
2. How do I evaluate the right SIEM vendor?
Look beyond certifications. Ask about use case coverage, tuning frequency, integration support, and how they handle alert fatigue.
3. What’s the biggest mistake enterprises make with SIEM?
Treating it as a one-time installation instead of a living and breathing system. Regular tuning, training, and integration are essential for value.
4. Is SIEM solution still relevant with EDR and NDR in play?
Absolutely. SIEM solution provides a broader, correlated view. EDR sees endpoints. NDR sees network traffic. SIEM ties it all together.
5. Can NetWitness SIEM integrate with third-party tools?
Yes. NetWitness supports many SIEM integrations through APIs, connectors, and custom parsers. This makes it easy to combine your current security tools.
6. How can I find out what my current approach is missing?
That’s where a Compromise Assessment comes in. NetWitness Incident Response (IR) can assess your current state of compromise and deliver a detailed report on what’s happening in your network. This gives you a clear comparison point: what you’re currently detecting versus what NetWitness can uncover. It’s often the fastest way to expose blind spots and validate whether your tools and



